2025 Report: AI Phishing & QR Code Surge AI-Driven
Cybercriminals continue to find the distribution of malicious software through pirated games and cracked applications a highly effective strategy. By exploiting the widespread desire for free access...
Cybercriminals continue to find the distribution of malicious software through pirated games and cracked applications a highly effective strategy.
By exploiting the widespread desire for free access to premium content, attackers can easily bypass initial user suspicions and deliver complex threats directly to personal devices.
A newly identified campaign exemplifies this persistent trend, utilizing a sophisticated loader that hides within modified game launchers to execute a multi-stage infection process without alerting the unsuspecting victim.
This emerging threat leverages the structure of the Ren’Py visual novel engine, making the malicious files appear as legitimate components of the game.
Victims who attempt to download these compromised packages are often redirected through multiple websites before finally reaching a file-hosting service.
Once the user executes the downloaded file, the malware initiates its operation under the guise of a standard loading screen, effectively masking the background malicious activity that is taking place.
Securelist analysts identified the malware as RenEngine, a distinct loader family that has been circulating since March 2025.
Although earlier iterations were primarily used to distribute the Lumma stealer, recent incidents reveal that the attackers have updated their toolkit to deliver ACR Stealer.
This evolution demonstrates the adaptability of the threat actors, who have also expanded their targets to include users searching for pirated graphics software and other productivity tools.
These stealers are designed to extract passwords, cryptocurrency wallets, and session cookies from the victim’s machine.
The impact of this campaign is significant, with widespread active incidents recorded across multiple countries including Russia, Brazil, and Spain.
The use of a modular loader allows the attackers to customize the infection chain, making it more difficult for standard security solutions to detect and block the initial compromise before damage occurs. This creates a major challenge for personal security.
Infection Mechanism and Evasion Tactics
The technical sophistication of RenEngine lies in its ability to avoid detection during the initial execution phase.
The attack begins with Python scripts that simulate a game loading process while simultaneously performing critical environment checks.
These scripts utilize a specific function called is_sandboxed to determine if the code is being analyzed by security researchers.
If the system is deemed safe, the malware proceeds to use xor_decrypt_file to unpack the next stage of the payload from an encrypted archive.
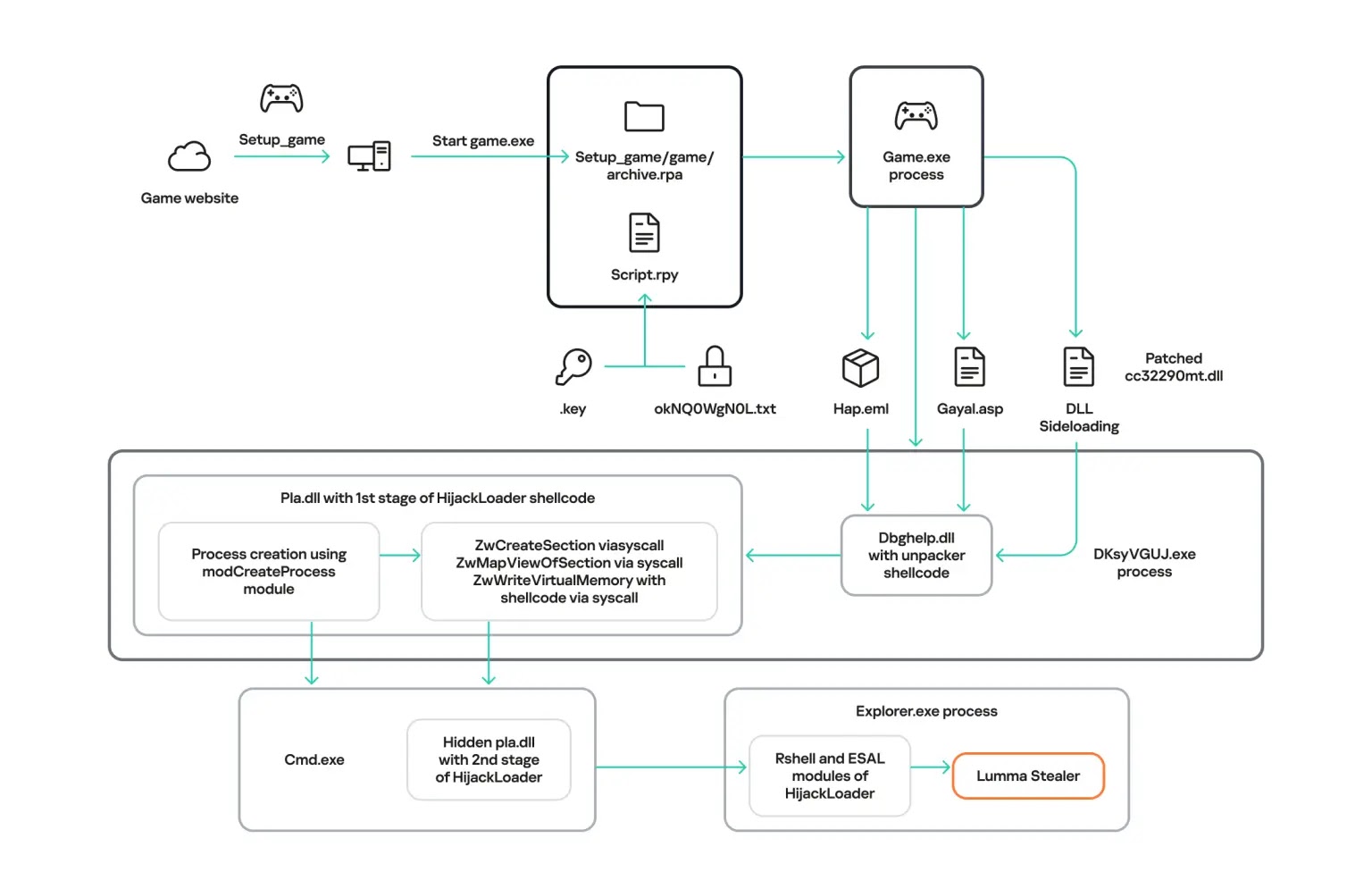
Following the initial decryption, the malware employs a technique known as DLL hijacking to load the HijackLoader module.
By overwriting the memory of a legitimate system library, specifically dbghelp.dll, the attackers can inject malicious code into a trusted process.
This method allows the loader to decrypt and launch the final payload, such as Lumma or ACR Stealer, within the memory space of a system process like explorer.exe.
This seamless injection ensures that the malware can operate persistently on the infected device, harvesting highly sensitive user data while remaining hidden from view.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.