OAuth Attack Bypasses Microsoft Entra Auth to Steal
As the year drew to a close, a clever new OAuth-based attack, dubbed ConsentFix, emerged. It exploits legitimate authentication flows to extract authorization codes from Microsoft Entra systems,...
As the year drew to a close, a clever new OAuth-based attack, dubbed ConsentFix, emerged. It exploits legitimate authentication flows to extract authorization codes from Microsoft Entra systems, presenting a significant challenge to the security landscape.
This attack represents an evolution of the ClickFix technique, demonstrating how attackers continue to refine their methods to compromise cloud-based authentication systems without triggering traditional security controls.
ConsentFix operates by creating a malicious Microsoft Entra login URL that targets the Azure CLI application and Azure Resource Manager, directing users to this specially crafted link through phishing tactics.
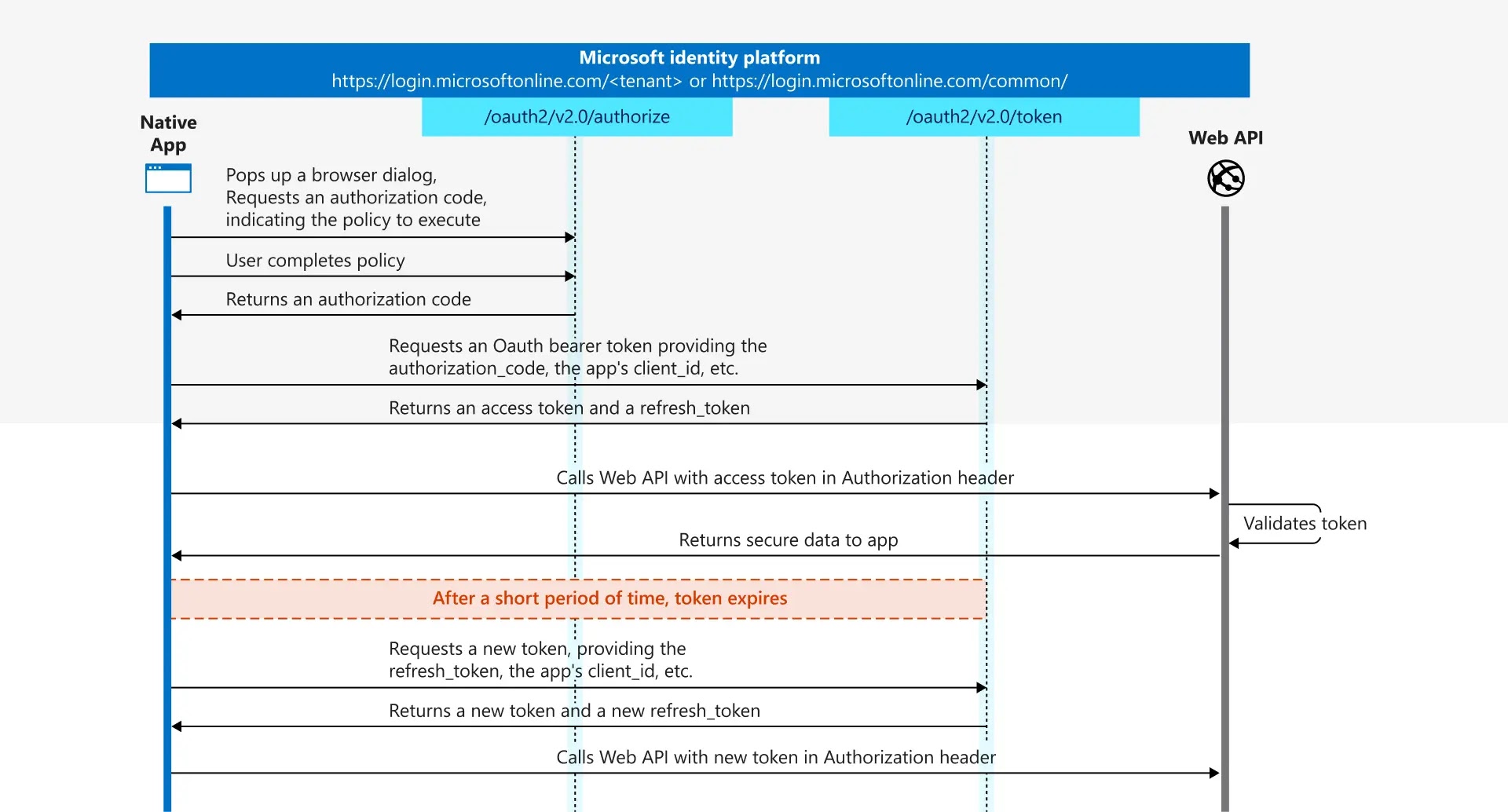
When an unsuspecting user visits a compromised website, the attack chain begins. The attacker leverages the OAuth 2.0 authorization code flow, a standard authentication mechanism that most users interact with daily when logging into cloud applications.
The user successfully authenticates with their credentials, and their browser redirects to what should be a legitimate reply address.
Instead of a functional application receiving the authentication code, the user encounters an error because no service listens on that localhost address.
The critical vulnerability lies in what happens next. The error page still contains the sensitive authorization code within the redirect URL, and the attacker simply requests the user copy and paste this information through drag-and-drop functionality.
Glueck Kanja analysts noted that this technique remarkably bypasses Conditional Access policies and device compliance requirements, making it particularly dangerous for organizations with otherwise robust security frameworks.
Detection and Response Mechanisms
Security teams must understand how ConsentFix manifests in logs to detect this attack effectively. When this attack occurs, Azure sign-in logs reveal two distinct authentication events from the same session.
The first event represents legitimate user interaction, appearing as an interactive sign-in from the victim’s location. The second event, originating from the attacker’s infrastructure, appears as a non-interactive sign-in as the attacker redeems the stolen authorization code for access tokens.
The temporal relationship between these events provides the most reliable detection signal. Azure authorization codes remain valid for approximately ten minutes, establishing a clear window where attackers must redeem tokens.
By correlating matching SessionIDs, ApplicationIDs, and UserIDs between the two events within this timeframe, defenders can identify attack attempts.
Analysts must also note that IP addresses typically differ between events, as the user and attacker operate from separate systems.
Advanced detection strategies filter out legitimate automation scenarios like GitHub Codespaces, which complete this authentication dance in mere seconds, distinguishing benign activity from malicious token theft attempts.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.