New ‘Penguin’ Pig Butchering as a Service Selling PII, Stolen
A dangerous evolution in cybercrime is underway as pig butchering scams transform into turnkey services, drastically lowering entry barriers for malicious actors worldwide. The “Penguin” operation...
A dangerous evolution in cybercrime is underway as pig butchering scams transform into turnkey services, drastically lowering entry barriers for malicious actors worldwide.
The “Penguin” operation represents a growing marketplace that provides everything scammers need to launch large-scale fraud campaigns, from stolen personal data to ready-made fraud templates.
This service-based model mirrors other crime-as-a-service platforms but targets victims through social engineering schemes that drain life savings and retirement funds.
Over the past decade, Chinese-speaking criminal groups have built industrial-scale scam centers across Southeast Asia, creating special economic zones dedicated entirely to fraud operations.
These compounds staff thousands of forced workers who execute romance scams, investment fraud, and other pig butchering schemes.
The transformation from individual scammers to organized service providers has created what experts call Pig Butchering as a Service, or PBaaS.
This model supplies criminal networks with tools, stolen credentials, infrastructure, and management platforms that enable operations to scale rapidly.
Hendryadrian and Infoblox Threat Intel analysts identified the Penguin operation through underground marketplace analysis, revealing a comprehensive fraud ecosystem.
The service provider operates under multiple names including Heavenly Alliance and Overseas Alliance, advertising openly on encrypted platforms.
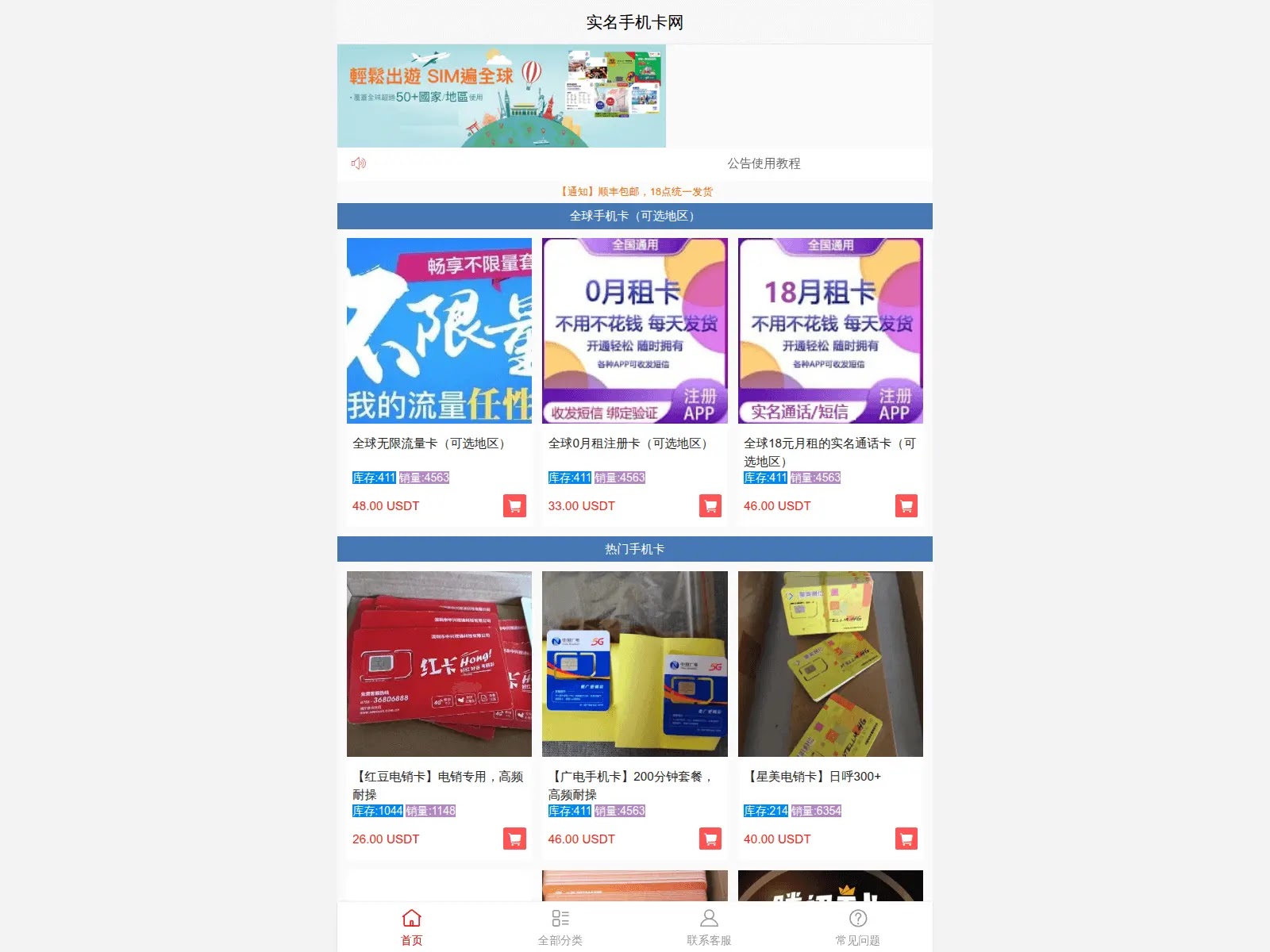
They offer fraud kits, pre-registered SIM cards, stolen social media accounts, and payment processing systems that allow scammers to launch operations with minimal technical knowledge.
Website templates start at just $50, while complete fraud packages cost around $2,500, making entry into this criminal economy surprisingly affordable.
Inside Penguin’s Operation and Service Offerings
Penguin began by selling shè gōng kù databases, which contain stolen personally identifiable information of Chinese citizens collected through government corruption or data breaches.
These databases include years of bank records, travel history, political affiliations, and family details that scammers use to identify wealthy targets and build trust during social engineering attacks.
The platform now sells Western social media accounts from Tinder, WhatsApp, Adobe, and Apple’s developer platforms. Pre-registered accounts cost as little as $0.10, with prices increasing based on registration date and authenticity verification.
The service extends beyond stolen data to include complete operational support. Penguin provides “character sets,” which are collections of stolen photos harvested from social media profiles used to create convincing fake identities.
They also offer 4G and 5G routers, IMSI catchers, and SCRM platforms that automate victim engagement across social channels.
The BCD Pay payment processing system connects directly to anonymous peer-to-peer networks rooted in illegal gambling operations, allowing scammers to launder stolen funds and move cryptocurrency outside law enforcement reach.
Criminal groups purchase management platforms like UWORK that centralize fraud operations through customer relationship management dashboards.
These platforms let administrators create agent profiles, set deposit thresholds, track profitability metrics, and geofence websites to avoid law enforcement in high-risk countries.
First-level agents handling direct victim contact have restricted access, preventing them from stealing money meant for operation leaders.
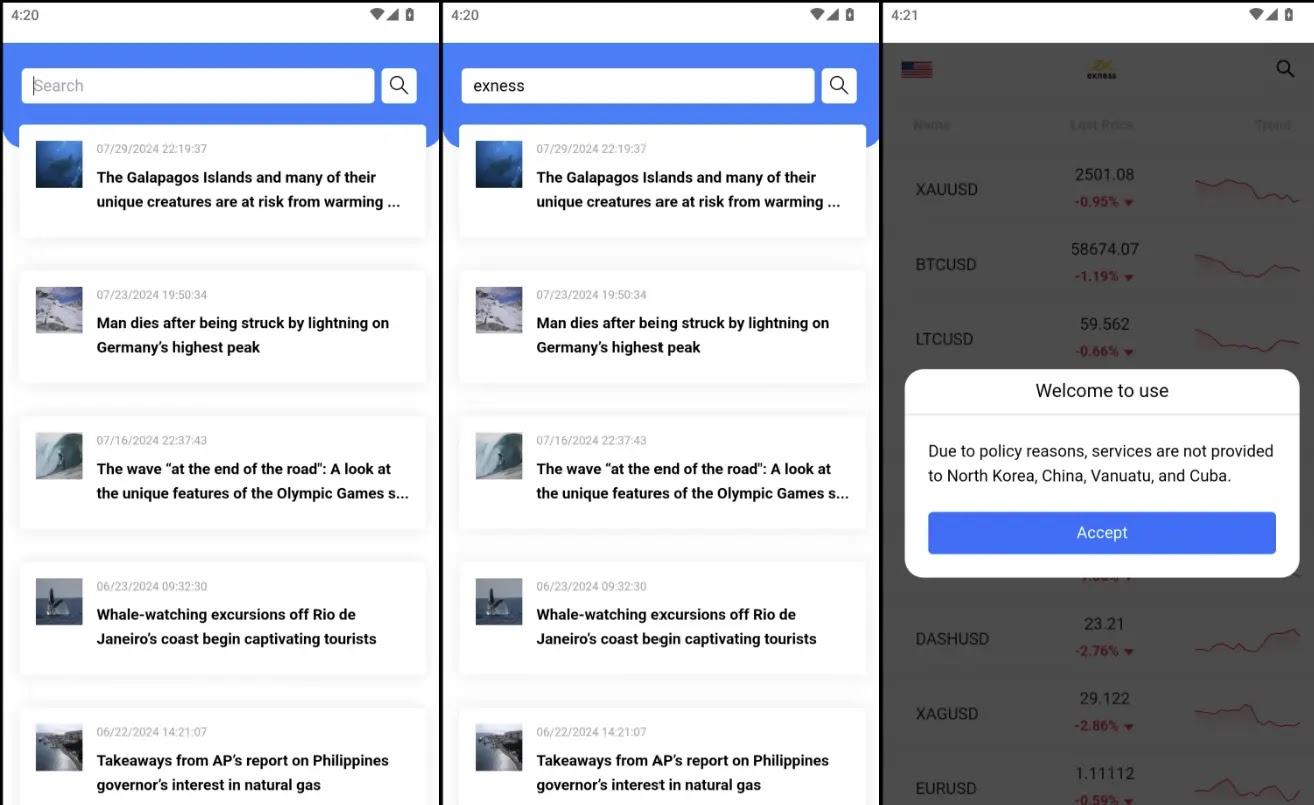
The systems integrate with legitimate trading platforms like MetaTrader, displaying real-time financial data that makes fake investment sites appear credible.
Mobile apps distributed through iOS provisioning files and Android APK sideloading bypass official app store verification, installing scam platforms directly onto victim devices while potentially granting device management access to criminals.
The commodification of these fraud services has dramatically increased both the scale and sophistication of pig butchering operations globally.
Law enforcement and security professionals now face an organized, service-based criminal ecosystem rather than isolated scam groups.
Disrupting this threat requires targeting the service providers, financial enablers, company formation facilitators, and DNS infrastructure that underpin the entire PBaaS economy.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.