Research Reveals 28 IPs & 85 Domains Hosting Uncovers Unique
An investigation recently exposed the technical infrastructure supporting underground carding operations, pinpointing 28 unique IP addresses and 85 domains actively hosting illegal marketplaces for...
An investigation recently exposed the technical infrastructure supporting underground carding operations, pinpointing 28 unique IP addresses and 85 domains actively hosting illegal marketplaces for the trade of stolen credit card data.
These platforms operate as sophisticated e-commerce sites for financial fraud, enabling criminals to trade stolen payment information ranging from $5 to $150 per card depending on credit limits and additional identity details.
The research conducted between July and December 2025 utilized internet-wide scanning techniques to identify servers hosting carding infrastructure before they could hide behind protective measures.
By performing searches across HTTP and HTTPS title banners on ports 80 and 443, investigators detected servers broadcasting carding-specific keywords such as “CVV,” “Dumps,” “Carding,” and “Shop.”
This scanning approach allowed researchers to capture server identities during initial configuration phases, before Content Delivery Networks like Cloudflare obscured their true locations.
Team Cymru analysts noted that the infrastructure analysis revealed significant patterns in how these criminal operations establish their technical presence.
The IP addresses discovered were hosting login pages and forum landing pages for carding sites, providing critical evidence that can support law enforcement actions including subpoenas and takedowns.
The most common top-level domains used by these operations were .su, .cc, and .ru, which offer jurisdictional advantages and loose registration policies that criminals exploit for operational security.
Credit card data theft occurs at multiple transaction points through various methods. Web skimming attacks inject malicious JavaScript into checkout pages, while database breaches target central servers of retail and financial organizations.
Physical theft techniques include skimming devices at ATMs and point-of-sale terminals that capture magnetic stripe data and PINs.
Once stolen, this data enters a sophisticated supply chain where specialized criminals handle different stages from theft to sale to conversion into cash.
The investigation also examined X.509 certificates and analyzed Subject Common Names to cluster related infrastructure based on reused certificate attributes.
This methodology enables tracking of bulletproof hosting environments where illicit marketplaces reside, even when operators attempt to use website cloning techniques to replicate legitimate carding markets for phishing purposes.
Hosting Infrastructure Analysis
The distribution analysis of Autonomous System Numbers from the 28 IP addresses showed that many hosting providers operate in offshore jurisdictions with limited law enforcement cooperation.
Privex emerged as the most common hosting provider, advertising privacy-minded infrastructure with dedicated VPS options that criminals purchase without providing identification.
These hosting services typically support multiple malicious activities beyond carding, including offensive security tools and hacking campaigns.
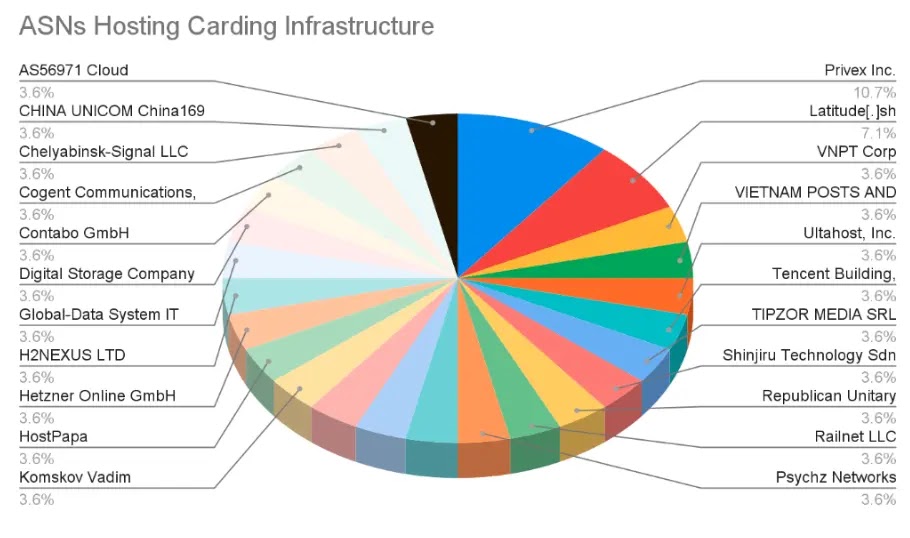
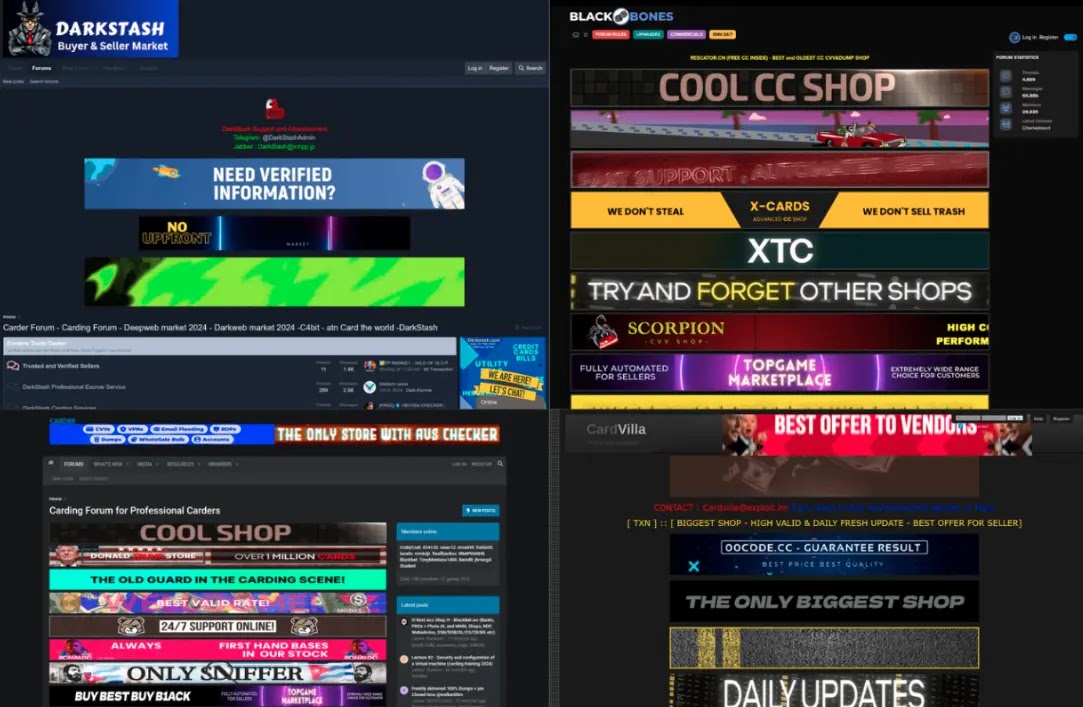
This above infrastructure displays the ASN distribution, while other above ones show the examples of carding market login pages and forum interfaces discovered during the research.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.