New Malware Campaigns Turn Devices Into DDoS & Crypto Bots
Two previously unknown malware strains have emerged, posing a significant new threat to network security. These strains are quietly transforming routers, IoT devices, and enterprise network equipment...
Two previously unknown malware strains have emerged, posing a significant new threat to network security. These strains are quietly transforming routers, IoT devices, and enterprise network equipment into weapons for large-scale distributed denial-of-service (DDoS) attacks and cryptocurrency mining operations.
These campaigns mark a clear shift in how threat actors are exploiting the very network infrastructure that organizations depend on daily.
On March 6, 2026, security researchers captured new samples of two never-before-documented malware strains.
The first, named CondiBot, is a DDoS botnet built on the well-known Mirai framework, designed to infect Linux-based network devices and transform them into remotely controlled nodes capable of flooding targeted systems with overwhelming traffic.
The second strain, called “Monaco,” is a sophisticated SSH scanner and crypto miner written in Go 1.24.0 that breaks into servers, routers, and IoT devices by brute-forcing weak SSH credentials, then silently deploys Monero cryptocurrency mining software.
Neither strain had been previously flagged on major threat intelligence platforms, including VirusTotal, ThreatFox, and Hybrid Analysis.
Eclypsium researchers identified both malware strains and noted that targeting network infrastructure is no longer limited to nation-state advanced persistent threat groups.
These findings confirm a growing pattern in which financially motivated actors, including crypto-mining operations, are actively exploiting the same vulnerabilities that state-sponsored hackers have long favored.
The broader threat landscape backs this concern. According to the 2025 Verizon Data Breach Investigation Report, there was an 8x increase in vulnerability exploits targeting network devices, with the median time to exploit sitting at zero days while the median time to patch stretched to 30 days.
Google Threat Intelligence Group further found that nearly a quarter of all zero-day vulnerabilities exploited in 2025 specifically targeted network and security systems, confirming that this attack surface is becoming a primary battleground.
What makes these campaigns especially dangerous is a fundamental visibility gap in most enterprise environments. Most endpoint detection and response tools are completely blind to the embedded firmware layers of network appliances.
Since these devices cannot run traditional security agents, attackers can operate undetected for months, quietly harvesting compute power or laying the groundwork for far larger attacks against downstream targets.
CondiBot’s Infection Mechanism and Persistence Tactics
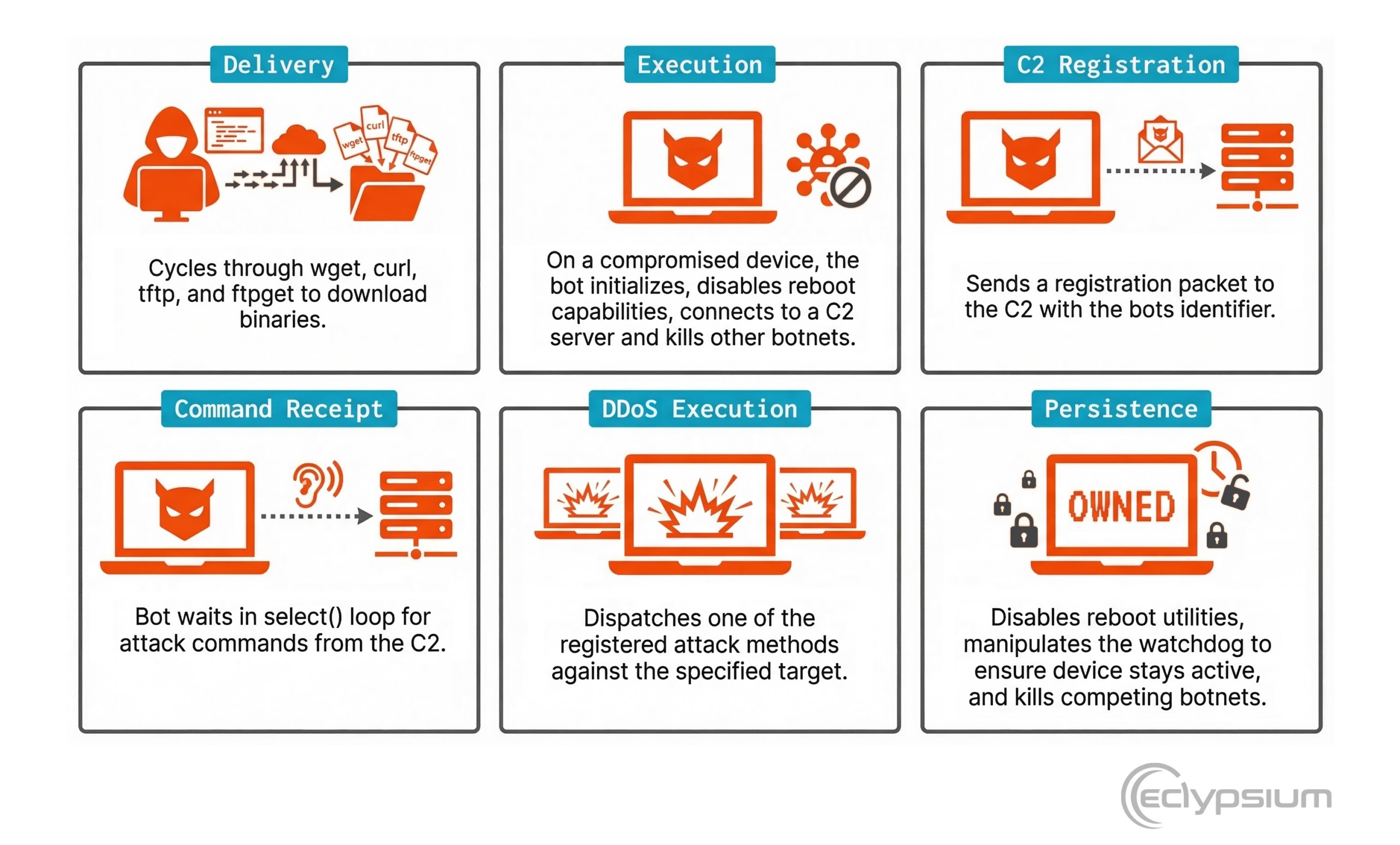
CondiBot’s attack process begins the moment it lands on a vulnerable Linux device. It uses a payload delivery method that cycles through multiple file transfer utilities — including wget, curl, tftp, and ftpget — to ensure the malicious binary reaches the target regardless of what tools are available on the device.
Once the binary executes, it immediately disables the system’s reboot utilities by setting their file permissions to 000, preventing a simple restart from clearing the infection. It then connects to a command-and-control (C2) server and registers itself using a unique bot identifier.
After registration, CondiBot enters a waiting loop, listening for attack commands from the C2. When an order arrives, it dispatches one of its 32 registered attack handlers against the specified target.
This marks a notable expansion from earlier Condi variants documented by Fortinet in 2023, which registered far fewer attack modules.
Analysts extracted a string labeled “QTXBOT” from the binary — an internal identifier not seen in any prior Condi documentation, suggesting this may be a forked variant or a separately maintained build by a different developer group.
The malware also actively kills competing botnets running on the same infected device, including a process named /bin/sora, ensuring full control over the compromised system’s resources.
It manipulates the hardware watchdog to keep the device running without interruption, making the infection very difficult to remove without direct physical intervention.
Organizations should enforce strong, unique SSH credentials and disable default passwords on all internet-facing devices.
Firmware integrity monitoring should be applied to routers, firewalls, and IoT equipment. Patches should be applied as quickly as possible, given that exploit timelines can be as short as zero days.
Monitoring for unusual outbound traffic and unexpected processes on network appliances is also strongly advised.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.