Threat Actors Scam Winter Olympics 2026 Fans with Beware Fake
Security teams report a rapid expansion of scam operations, evidenced by the active emergence of additional domain registrations. Malwarebytes now blocks these fraudulent domains, safeguarding users...
Security teams report a rapid expansion of scam operations, evidenced by the active emergence of additional domain registrations. Malwarebytes now blocks these fraudulent domains, safeguarding users worldwide from falling victim to the growing threat.
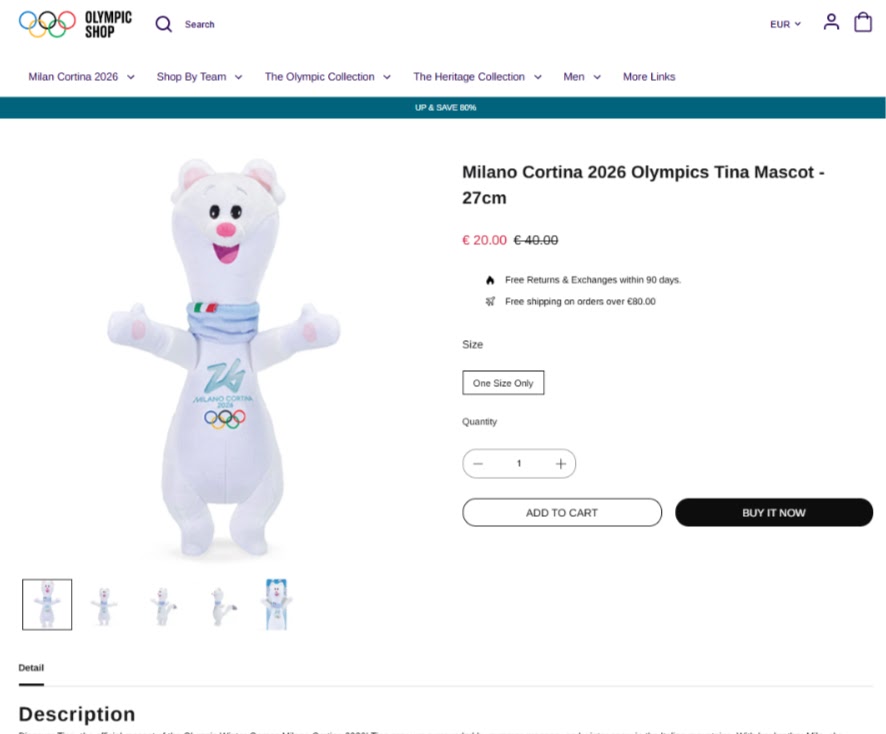
The fraudulent websites lure victims with deep discounts on items that are unavailable elsewhere.
While the official Tina plush toy costs €40 and remains completely out of stock, these fake shops advertise the exact same product for just €20 with banners claiming “UP & SAVE 80%.”
This aggressive pricing strategy serves as irresistible bait to attract unsuspecting Olympic fans who are desperate to purchase the popular merchandise for themselves or their children.
Scam Operation Tactics
The fake Olympic shops operate with multiple malicious objectives that extend far beyond simply taking payment without delivering products.
Threat actors actively harvest payment card details that victims enter during checkout, while simultaneously collecting names, addresses, email addresses, and phone numbers for use in future cyberattacks.
Many victims subsequently receive follow-up phishing emails carefully designed to extract additional sensitive information or login credentials.
Some scammers even distribute malware through fake order confirmations or malicious tracking links sent to victims after purchase, further compromising their devices and networks.
Security experts strongly recommend purchasing merchandise only from the official shop.olympics.com website by typing the address directly into browsers and bookmarking it for future use.
Shoppers should consistently avoid clicking links from advertisements, social media posts, or unsolicited emails. They should remain highly skeptical of extreme discounts being offered on items that are officially sold out everywhere else.
Customers must carefully inspect domain names for suspicious top-level extensions, extra hyphens, or subtle character substitutions before making purchases.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.