FancyBear Server Exposure: Stolen Credentials & NATO Targets
An operational security failure by the Russian state-linked hacking group FancyBear has provided security researchers an unusually clear view into an active espionage campaign. This operation...
An operational security failure by the Russian state-linked hacking group FancyBear has provided security researchers an unusually clear view into an active espionage campaign. This operation specifically targets government and military organizations across Europe.
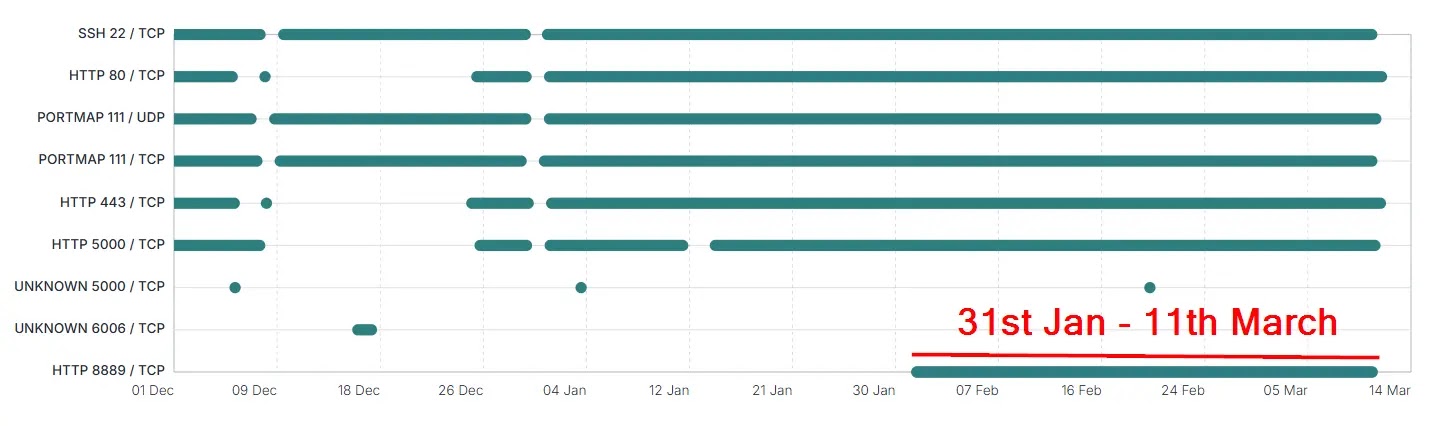
On March 11, 2026, threat intelligence firm Hunt.io published findings on a campaign it tracks as Operation Roundish, based on an exposed open-directory first scanned on January 13, 2026.
FancyBear — also tracked as APT28, Forest Blizzard, and Sednit — is assessed by the UK’s NCSC to be Russia’s GRU Military Intelligence Unit 26165.
What started as a focused webmail exploitation campaign had been quietly running for over a year before the group inadvertently left its server door wide open.
The exposure stemmed from a NameCheap Virtual Private Server located in the United States, operating on IP address 203.161.50.145.
This same server had been publicly attributed to FancyBear by Ukraine’s CERT-UA as far back as September 2024 — yet the group continued operating from it for over 500 days without switching infrastructure.
Within the open-directory, researchers uncovered 2,800 exfiltrated government and military emails, 240 sets of stolen credentials including passwords and TOTP 2FA secrets, 140 silent email-forwarding rules, and 11,500 contact addresses harvested from victims’ address books across multiple targeted countries.
Ctrl-Alt-Intel analysts discovered a second exposed open-directory on the same server — one not captured in Hunt.io’s January 2026 archive.
Inside sat FancyBear’s full command-and-control source code, additional JavaScript payloads, campaign telemetry logs, and exfiltrated data that provided a near-complete picture of the entire operation.
Victims spanned Ukraine, Romania, Bulgaria, Greece, Serbia, and North Macedonia, with email addresses tied to four NATO member states — including NATO’s own headquarters infrastructure — recovered directly from the stolen contact data.
The geopolitical pattern of targeting was clearly deliberate. Ukraine’s regional prosecutors, likely connected to war crimes investigations, formed the single largest victim group.
Romania’s Air Force, Greece’s National Defence General Staff, Serbia’s Ministry of Defence, and Bulgarian government entities were also compromised.
Romania, Bulgaria, and Greece had signed a military mobility agreement in July 2024, and Greece had been involved in training Ukrainian F-16 pilots — both facts that strongly point to intelligence-driven target selection rather than random opportunistic intrusions.
How FancyBear Bypassed 2FA Without Victims Ever Knowing
The most technically alarming discovery in this campaign was FancyBear’s method for silently stealing TOTP-based 2FA secrets from victims who believed their accounts were fully protected.
The group deployed a JavaScript module called keyTwoAuth.js, which ran entirely inside the victim’s already-authenticated Roundcube webmail session — no additional click or separate login was ever required from the target.
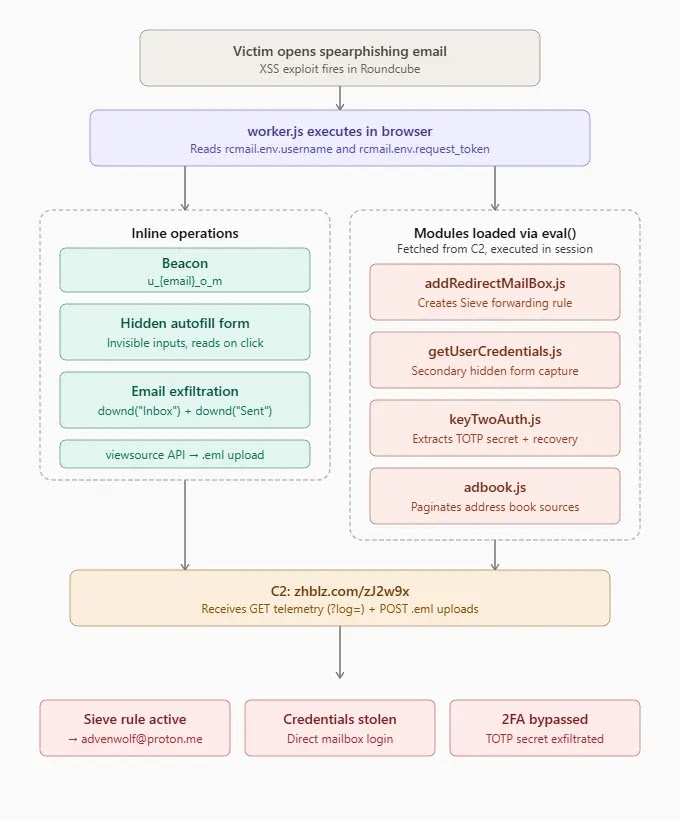
Once the XSS payload triggered, keyTwoAuth.js sent an HTTP request to Roundcube’s 2FA settings page for the twofactorgauthenticator plugin.
It then parsed the returned HTML, pulled out five hidden password fields — one TOTP secret and four recovery codes — base64-encoded everything, and quietly delivered the package to FancyBear’s C2 server at zhblz.com using the log prefix ktfu.
With both the victim’s password and TOTP secret secured, FancyBear could generate valid authentication codes at any future point, bypassing two-factor protection entirely without ever needing physical access to the victim’s device.
Ctrl-Alt-Intel recovered 516 log entries under the ktfu prefix across 108 unique victim addresses. Of those, 256 accounts had real TOTP secrets stolen, hitting targets at Romania’s Air Force, Greece’s GEETHA, Ukraine’s Asset Recovery Agency, and Serbia’s Ministry of Defence. The remaining 260 returned “nokey,” meaning those accounts had no 2FA configured at all, making them even more straightforward to access.
Organizations running Roundcube with the twofactorgauthenticator plugin should treat all existing TOTP secrets as potentially compromised and rotate them without delay.
Administrators are advised to audit Sieve email-filtering rules for unauthorized forwarding entries — especially those named “SystemProtect” or “SystemHealthChek” — and block all connections to C2 IP address 203.161.50.145 and the domain zhblz.com.
Applying the patch for Roundcube CVE-2023-43770 and monitoring webmail infrastructure for signs of XSS injection remain the most critical defensive steps any affected organization can take right now.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.