LeakNet Ransomware Scales with ClickFix Lures Operations Stealthy
The LeakNet ransomware group is evolving a more dangerous attack strategy. Previously averaging three victims monthly, the group is now rapidly scaling its operations. It’s incorporating new...
The LeakNet ransomware group is evolving a more dangerous attack strategy. Previously averaging three victims monthly, the group is now rapidly scaling its operations. It’s incorporating new tools designed to evade detection by most security defenses.
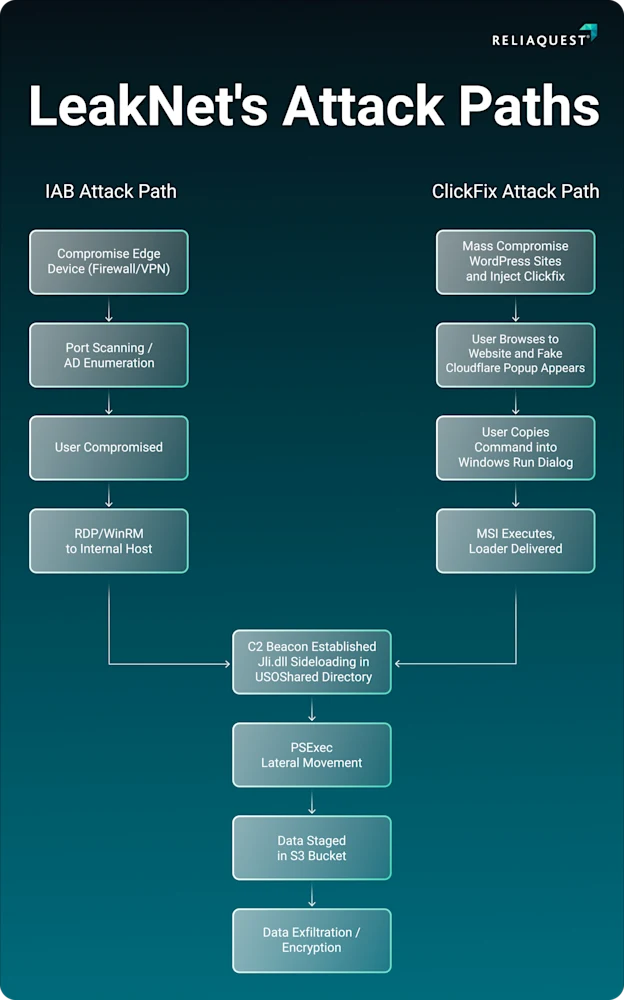
LeakNet has introduced two notable additions: a social engineering trick called ClickFix and a stealthy, memory-based loader built on the Deno JavaScript runtime.
ClickFix is not a brand-new technique in the threat landscape, but LeakNet’s move toward using it marks a significant change in how the group finds its victims.
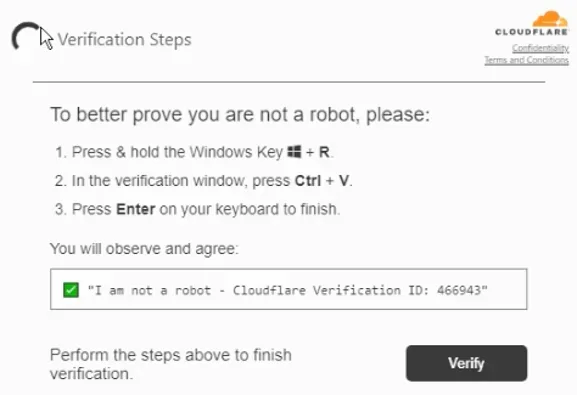
Instead of purchasing stolen access credentials from initial access brokers (IABs) on underground markets, LeakNet now plants fake verification pages on compromised but otherwise legitimate websites.
When an unsuspecting user lands on one of these pages, they are shown what looks like a standard Cloudflare Turnstile check and are prompted to manually run a command.
There is no specific victim profile here — the group simply casts a wide net and counts on a portion of users to take the bait.
ReliaQuest analysts identified the activity across multiple recent incidents, attributing it to LeakNet with high confidence based on overlapping infrastructure and consistent tactics, techniques, and procedures (TTPs).
The shift away from IABs is deliberate: it removes a dependency that slowed the group down and broadens the pool of potential victims considerably. ClickFix has become a preferred delivery method across the threat landscape, facilitating the distribution of 59% of the top malware families tracked in 2025.
This shift puts any web-browsing employee at risk. Because the lures are hosted on real websites rather than attacker-owned domains, standard network-layer defenses generate far fewer alerts.
The red flag only appears after the user has already run the malicious command, which puts more weight on behavioral monitoring — particularly for suspicious msiexec commands and unexpected outbound connections — rather than domain-based blocking alone.
What makes LeakNet’s current campaign particularly concerning is how both entry paths — ClickFix and Microsoft Teams phishing — feed into the same post-exploitation chain every time.
The group moves through execution, lateral movement, and payload staging with the same tools regardless of how it got in.
That consistency is a useful signal for defenders: knowing the steps means there are clear points where the attack can be detected and cut short.
The Stealthy Deno-Based Loader
One of the most technically dangerous parts of LeakNet’s updated toolkit is a previously unreported loader built on Deno, a legitimate JavaScript and TypeScript runtime used daily by developers.
LeakNet uses a bring-your-own-runtime (BYOR) approach — instead of deploying a custom malicious binary that might trigger security tools, the attackers install the real, trusted Deno executable on the victim’s machine and use it to run harmful code.
The loader is activated through PowerShell and Visual Basic Script files, notably named Romeo*.ps1 and Juliet*.vbs.
Rather than writing a JavaScript file to disk where it could be scanned, LeakNet feeds the payload to Deno as a base64-encoded data URL, which Deno decodes and runs entirely in memory.
No standard file ever touches the endpoint, making the entire process nearly invisible to signature-based security tools.
Once the loader runs, it collects basic system details — username, hostname, memory size, and OS version — then creates a unique victim fingerprint.
It connects to attacker-controlled infrastructure to retrieve a victim-specific second-stage payload, prevents duplicate instances by binding to a local port, and then enters a looping cycle of fetching and executing further code in memory.
To reduce exposure, organizations should block newly registered domains, since LeakNet’s command-and-control servers are typically only weeks old.
Regular users should be restricted from running Win-R commands on their workstations, and PsExec should be limited to authorized administrators through Group Policy Objects (GPOs).
Security teams should watch for jli.dll sideloading in the C:ProgramDataUSOShared directory, unusual PsExec activity, and unexpected outbound connections to S3 buckets.
Isolating a compromised host the moment post-exploitation behavior is confirmed is the most direct way to break the chain before ransomware reaches deployment.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.