Mirai Botnets Evolve: Massive DDoS Mirai-Based Into
The internet has experienced a sharp rise in botnet-driven threats over the past year, with much of this activity stemming from Mirai. This malware family, considered one of the most influential in...
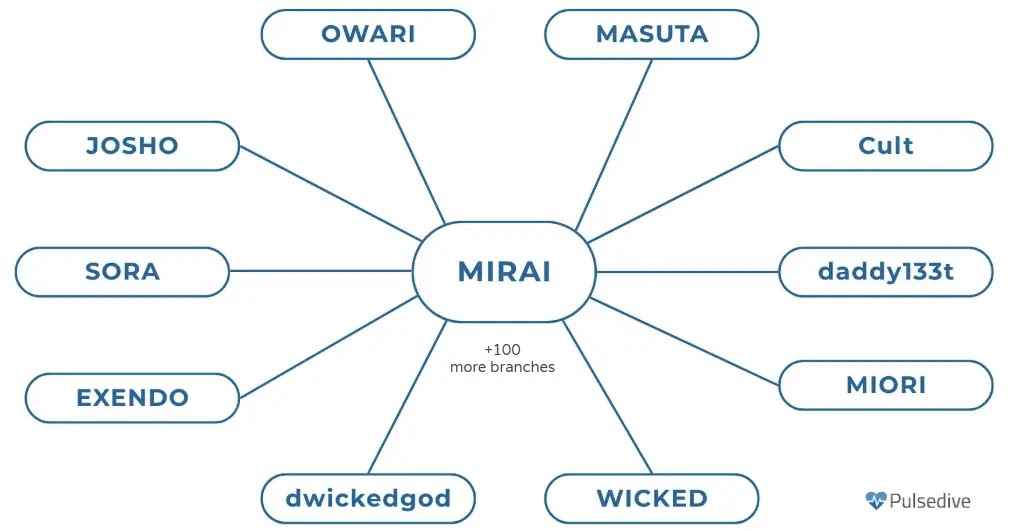
The internet has experienced a sharp rise in botnet-driven threats over the past year, with much of this activity stemming from Mirai. This malware family, considered one of the most influential in modern history, continues to evolve significantly. A
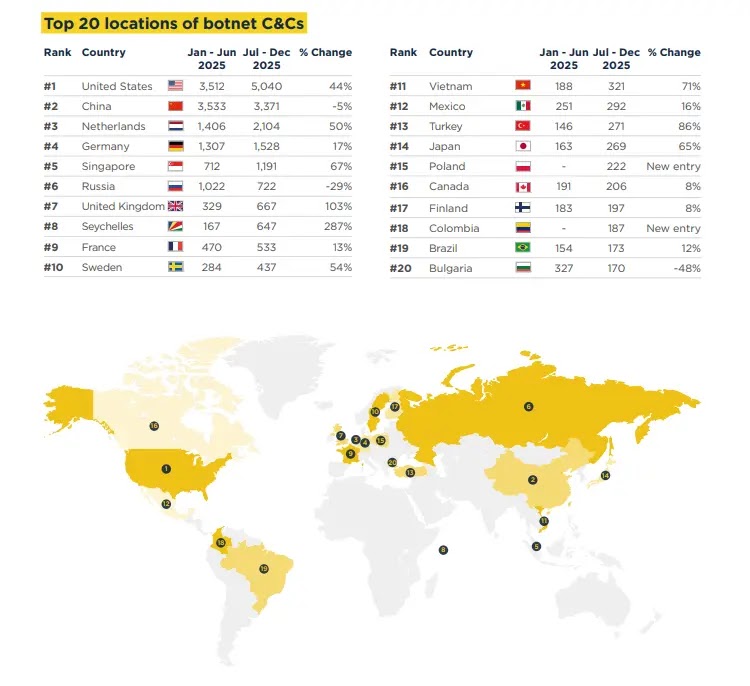
Pulsedive researchers identified and tracked several active Mirai-based botnets, with Aisuru and Kimwolf emerging as the most destructive.
Together, these two variants — often referred to as Aisuru-Kimwolf — have compromised between one and four million hosts around the world.
Cloudflare documented that Aisuru-Kimwolf is behind some of the largest DDoS attacks ever recorded, including a 31.4 terabit-per-second flood and a 14.1 billion packet-per-second assault.
These numbers go well beyond anything earlier Mirai variants could produce and highlight just how dangerous the next generation of these botnets has become.
The operators behind Aisuru-Kimwolf have turned their infrastructure into a criminal business, selling access to compromised devices through platforms like Discord and Telegram.
On March 19, 2026, the U.S. Department of Justice announced court-authorized disruption actions against the C2 servers supporting Aisuru, KimWolf, JackSkid, and Mossad botnets, with enforcement operations spanning Canada and Germany.
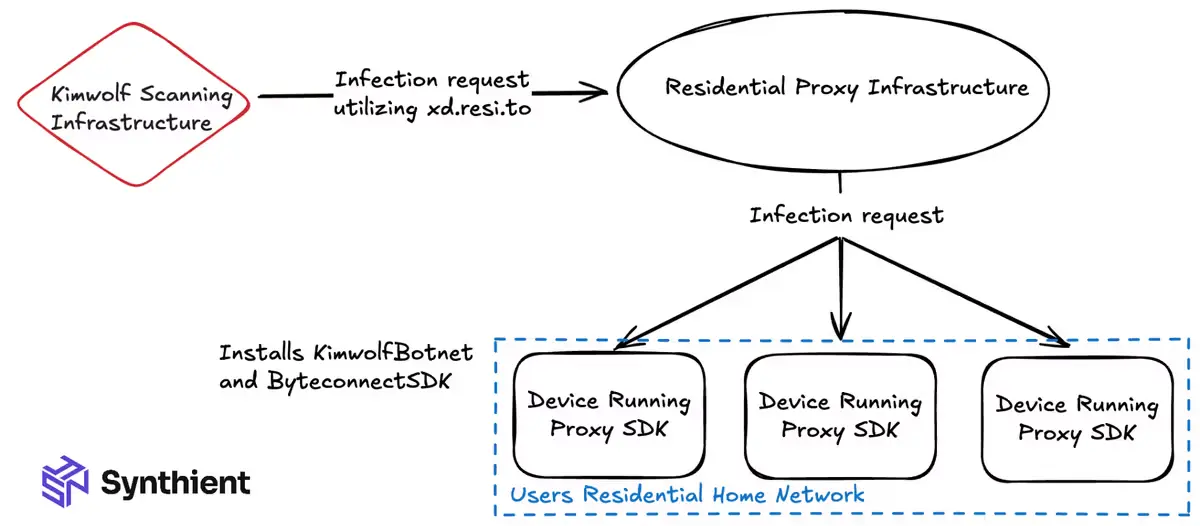
Beyond DDoS attacks, the botnets have been used to abuse residential proxy networks, routing attack traffic through IP addresses belonging to ordinary homeowners, making the activity far harder to trace. Despite the takedown efforts, these botnets continue to adapt and find new ways to stay operational.
Kimwolf’s Infection Mechanism and Infrastructure Evasion
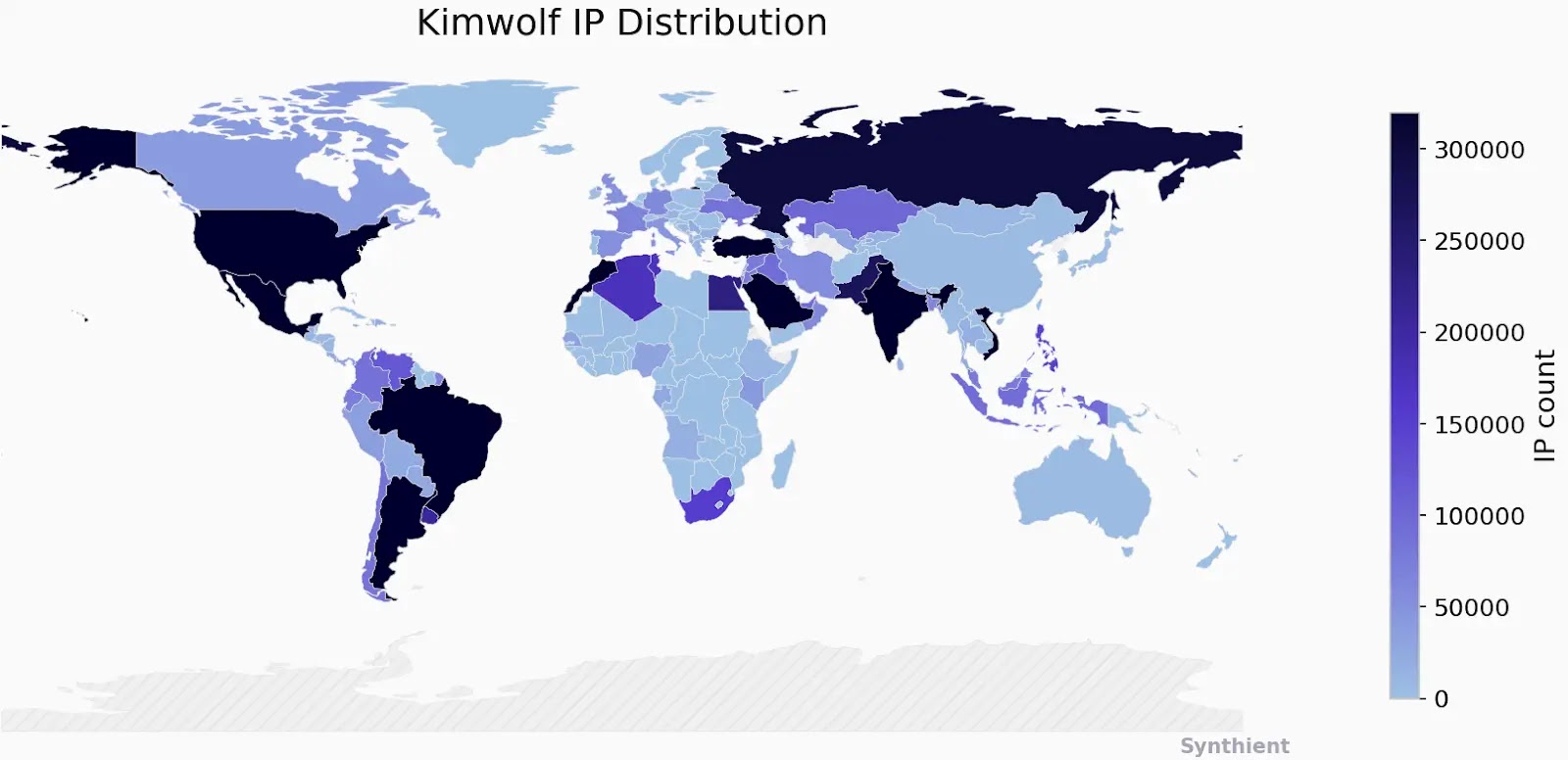
Kimwolf is an Android-focused subvariant of Aisuru built to target mobile devices and Smart TVs.
It has infected approximately two million Android devices globally, leveraging the same DDoS capabilities as Aisuru but modified to work on Android systems.
Once a vulnerable device is reached, Kimwolf runs an install script that downloads .apk files from an attacker-controlled server. The script makes each file executable and runs them in sequence, targeting different CPU architectures to infect as many devices as possible.
After Google and the DOJ disrupted the IPIDEA residential proxy infrastructure tied to Kimwolf, reports surfaced that the botnet had shifted to The Invisible Project (I2P), a decentralized, encrypted communications network designed to anonymize traffic.
This shift was a direct response to takedown pressure — I2P is far harder to monitor or shut down than conventional infrastructure.
The move underlines a clear pattern: these operators watch law enforcement actions closely and quickly reroute their operations the moment any disruption hits.
Network providers often offer DDoS protection solutions that can detect and block bot-driven traffic, and organizations should take full advantage of these.
Protective DNS services can filter suspicious domain queries before they reach internal systems. Publicly accessible network devices, especially routers, should be patched consistently.
Default credentials on all networking equipment must be replaced with strong, unique passwords during initial setup and should never be left unchanged.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.