Ghost SPN Attack Enables Stealthy Kerberoasting by
A sophisticated evolution of Kerberoasting, dubbed the “Ghost SPN” attack, has surfaced. This new method enables adversaries to extract Active Directory credentials while simultaneously erasing all...
A sophisticated evolution of Kerberoasting, dubbed the “Ghost SPN” attack, has surfaced. This new method enables adversaries to extract Active Directory credentials while simultaneously erasing all traces of their activity. As a result, traditional detection models are rendered effectively blind to the intrusion.
The attack revealed by Trellix security researchers utilizes delegated administrative permissions, creating temporary exposure windows.
Kerberoasting is a well-documented post-exploitation technique targeting Active Directory (AD) accounts registered with Service Principal Names (SPNs).
When a Ticket Granting Service (TGS) ticket is requested for an SPN, the Kerberos Key Distribution Center (KDC) encrypts it with the target account’s NTLM hash, which attackers can extract and crack offline to recover plaintext credentials.
The Ghost SPN variant takes this a step further. Rather than enumerating pre-existing service accounts, adversaries exploit delegated directory permissions, such as GenericAll object-level write access, to temporarily assign a fake SPN to an ordinary user account.
This converts a standard user into an ephemeral Kerberoasting target without touching any known service account, generating zero enumeration-based alerts in the process.
The Three-Phase Attack Lifecycle
According to Trelix researchers, the attack unfolds across three deliberate phases:
- SPN Assignment (Out-of-Band): The attacker leverages write access to manually assign an arbitrary SPN (e.g.,
http/webapp) to a target account via PowerShell commandlets. The KDC, seeing a valid service principal, issues a TGS ticket encrypted with RC4-HMAC-MD5 — standard Kerberos behavior with no anomaly visible at the protocol level. - Extraction and Offline Cracking: The TGS ticket is dumped using tools like Mimikatz and exported as a
.kirbifile. Cracking occurs entirely outside the environment using tools such as Hashcat ortgsrepcrack.py, generating no authentication failures or suspicious login attempts within the target infrastructure. - Cleanup and Anti-Forensics: The SPN attribute is immediately cleared, restoring the account to its original state. Without persistent indicators, defenders relying on static directory snapshots or low-fidelity audit logs cannot retroactively link the TGS request to malicious behavior.
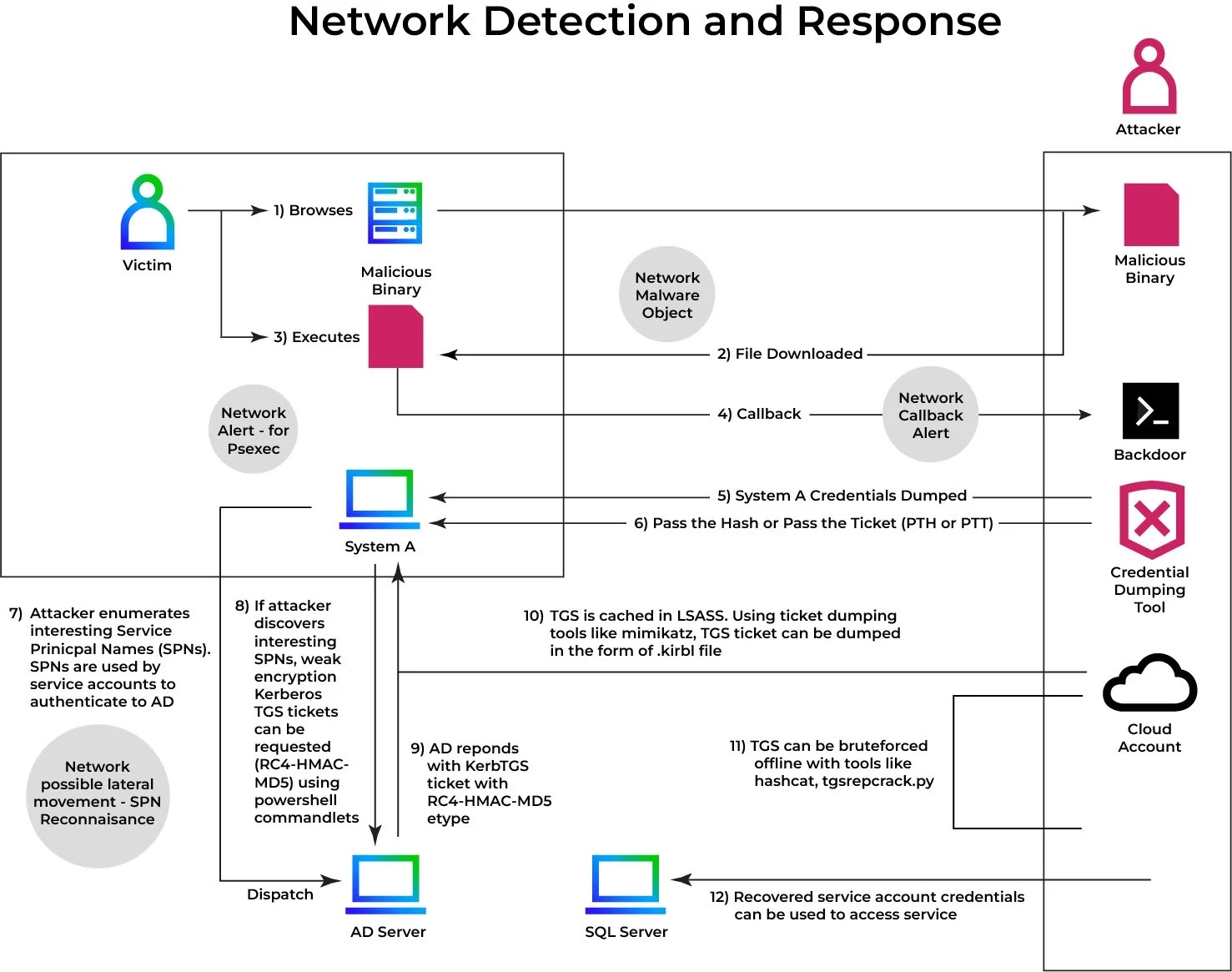
This technique directly undermines detection models built around two flawed assumptions: that Kerberoasting targets are always pre-registered service accounts, and that malicious activity produces high-volume ticket request anomalies.
The targeted account may have never held a service role. The SPN may exist for only seconds. When evaluated in isolation, the activity is indistinguishable from a legitimate administrative action, with a critical visibility gap in SOC stacks relying on fragmented log analysis.
Mitigations
Organizations should take the following immediate steps:
- Audit ACLs aggressively — identify and revoke
GenericAllorWriteSPNpermissions granted to non-administrative accounts - Enable granular AD change logging — correlate
msDS-ServicePrincipalNameattribute modifications with downstream Kerberos ticket requests - Enforce AES-only Kerberos encryption — eliminate RC4-HMAC-MD5, which is significantly more vulnerable to offline cracking
- Reset compromised account passwords — prioritize accounts with historical write-access exposure to privileged objects
- Deploy behavioral NDR tooling — static signature matching and SIEM-only approaches cannot detect ephemeral identity manipulation without cross-domain telemetry
As adversaries increasingly pivot from exploiting software vulnerabilities to abusing legitimate directory permissions, a hallmark of Living-off-the-Land (LotL) tradecraft, defenders must shift focus from access attempt monitoring to continuous surveillance of identity attribute changes, especially those engineered to disappear.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.