Fake VS Code Security Alerts on GitHub Push Malware
Software developers on GitHub are the target of a widespread phishing campaign leveraging fake Visual Studio Code security alerts. These alerts, appearing in GitHub Discussions, aim to trick users...
Software developers on GitHub are the target of a widespread phishing campaign leveraging fake Visual Studio Code security alerts. These alerts, appearing in GitHub Discussions, aim to trick users into downloading malicious software.
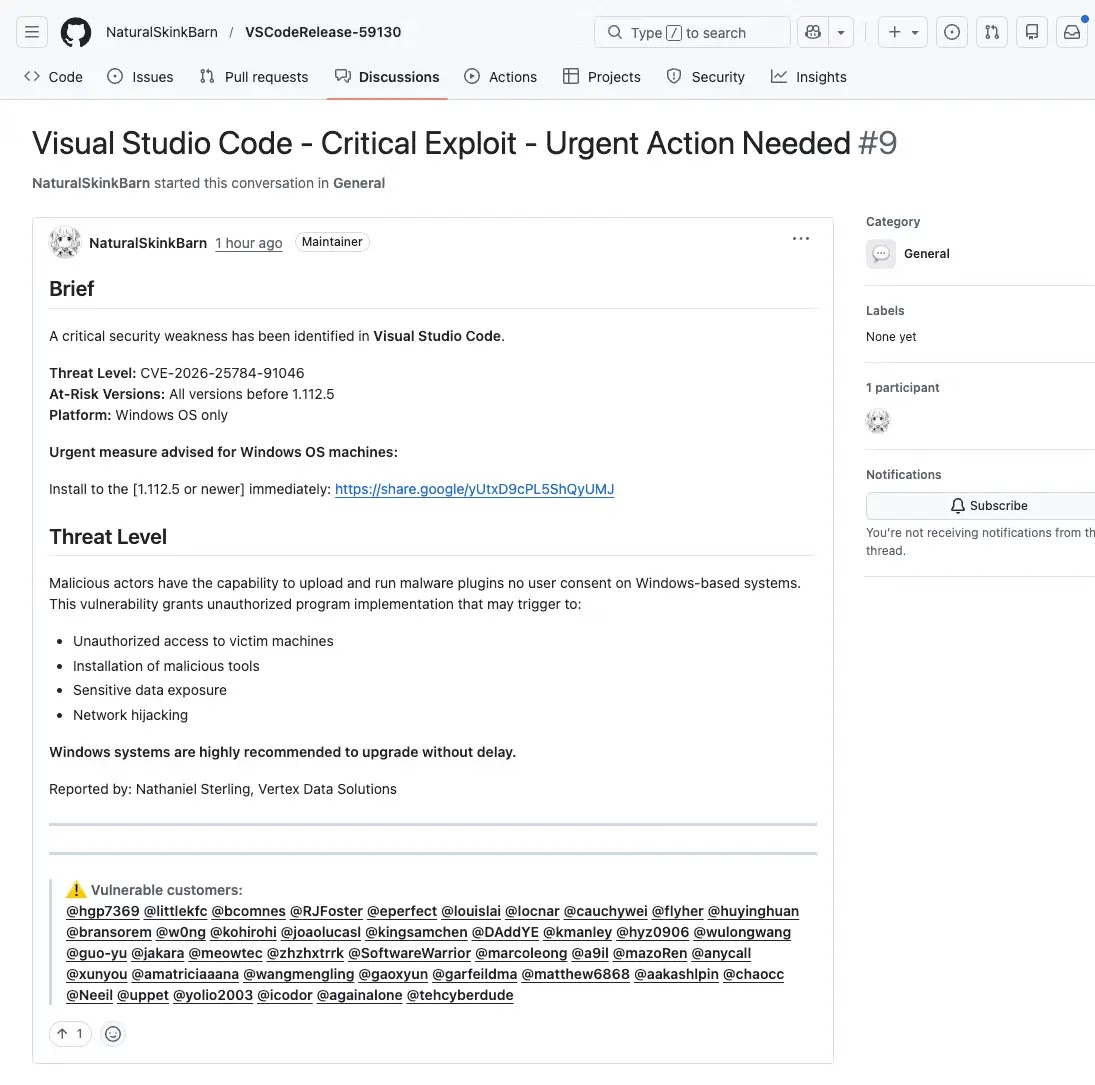
The attacks are designed to look like legitimate security advisories, warning developers of critical vulnerabilities in VS Code and urging them to install a so-called “patched” version through an external link.
The campaign surfaced through thousands of near-identical posts flooding GitHub repositories within minutes of each other.
Each post mimics an official security advisory, carrying alarming titles such as “Visual Studio Code – Severe Vulnerability – Immediate Update Required,” “Critical Exploit – Urgent Action Needed,” and “Severe Threat – Update Immediately.”
The posts often reference fabricated CVEs and fake version ranges to make the warnings appear credible.
Since GitHub Discussions automatically trigger email notifications to repository participants and watchers, these fake alerts are also delivered directly to developers’ inboxes, extending the campaign’s reach far beyond the platform itself.
Socket.dev analysts identified the campaign as a coordinated spam operation, noting that posts were being created by newly created or low-activity accounts, tagging large numbers of developers across unrelated repositories for maximum exposure.
The researchers found that the campaign abuses GitHub’s own notification system to make fake alerts appear both urgent and legitimate — a tactic that reduces a developer’s natural skepticism when reading what looks like a trusted platform warning.
Each fake Discussion includes a link to download the supposed updated version of VS Code, but these links point to file-sharing services rather than official distribution channels.
Legitimate VS Code updates are never distributed this way, yet the urgency built into these posts is enough to push developers into clicking without hesitation.
The attack blends smoothly into GitHub’s collaborative environment, turning a developer’s everyday workspace into a delivery channel for malware.
The scale of the campaign makes it particularly alarming. Hundreds to thousands of these posts appeared across GitHub search results in rapid succession, pointing to a heavily automated operation.
The fact that developers are being targeted inside a platform they trust daily, rather than through traditional phishing emails, marks a notable shift in how attackers approach developer-focused threats.
Multi-Step Redirection and Browser Fingerprinting
Socket.dev analysts traced one of the payloads linked in the fake Discussions and uncovered a carefully built multi-step redirection chain. Clicking the link first routes the victim through a Google share endpoint.
From there, the path splits based on whether the user’s browser carries a valid Google cookie. Users with a cookie are automatically sent via a 301 redirect to the attacker-controlled domain, drnatashachinn[.]com, which functions as the campaign’s command-and-control server.
Users without a cookie are served a fingerprinting page directly from the Google endpoint, likely as a fallback to filter out bots and automated security scanners.
Once a real user lands on the attacker’s infrastructure, an obfuscated JavaScript payload executes immediately.
The script gathers browser fingerprint data, including timezone, locale, platform, user agent, and automation signals like navigator.webdriver, used to identify whether the visitor is a real person or a bot.
A hidden iframe further cross-checks the user agent to detect spoofed environments. All collected data is then silently submitted to the attacker’s endpoint via an automatic POST request, requiring no interaction from the victim.
This profiling stage acts as a filtering layer, sorting real users from scanners before routing confirmed targets to a follow-on payload, such as a phishing page or exploit kit.
Developers should treat all unsolicited security alerts in GitHub Discussions with caution, especially when posts include external download links, unverifiable CVE references, urgent install instructions, mass tagging of unrelated users, or content from recently created accounts.
Security updates for VS Code should always be verified through official Microsoft channels only, and any suspicious Discussion should be reported directly to GitHub for review.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.