JanaWare Ransomware Targets Turkish Users via Through Customized
A new ransomware family, JanaWare, has begun actively targeting computer users in Turkey. This emerging threat leverages a customized version of the Adwind remote access trojan (RAT) to establish an...
A new ransomware family, JanaWare, has begun actively targeting computer users in Turkey. This emerging threat leverages a customized version of the Adwind remote access trojan (RAT) to establish an initial foothold on victims’ systems, as detailed in a recent security analysis.
This campaign stands out because it combines a known cross‑platform RAT with fresh ransomware logic and a distribution model tailored to local users, making the threat both familiar and uniquely dangerous for Turkish victims.
According to the investigation, the operation appears focused on personal users and small businesses, where security controls are often weaker and email‑based attacks are more likely to succeed.
The attack chain typically starts with phishing or socially engineered messages that push victims to open malicious attachments or links, often disguised as routine documents or business‑related files in Turkish.
When the victim interacts with these lures, the customized Adwind RAT is silently installed, giving the attacker remote control over the machine and enabling the next stage of the attack.
At this point in the campaign, files are not yet encrypted; instead, the RAT is used to survey the system, profile the victim, and download the JanaWare payload only when the target looks profitable or interesting.
Acronis threat analysts first identified this JanaWare activity while monitoring a series of Adwind‑based intrusions that showed unusual behavioral patterns on Turkish endpoints.
Their telemetry and sandbox analysis revealed that the Adwind samples in this campaign carried additional modules and post‑exploitation scripts that did not match previously documented versions of the RAT.
By correlating network traffic, command‑and‑control (C2) instructions, and the final encryption routine, the researchers confirmed that a new ransomware strain was being delivered on top of the customized Adwind infrastructure rather than through a standalone binary.
Once JanaWare is deployed, its impact becomes immediately visible to victims, as critical documents, archives, images, and databases are encrypted and renamed with a specific extension associated with the campaign.
The ransomware then drops a ransom note that explains the situation in direct language, warns that files cannot be restored without the attacker’s key, and instructs victims to make contact using the channels provided in the message.
In some observed cases, the note also references local‑language instructions and pricing that appear tuned to the Turkish market, indicating that the operators have done basic regional research to maximize payment chances.
This combination of targeted language, selective deployment, and robust encryption means successful attacks can cause major disruption for individuals and small organizations that lack mature backup and recovery processes.
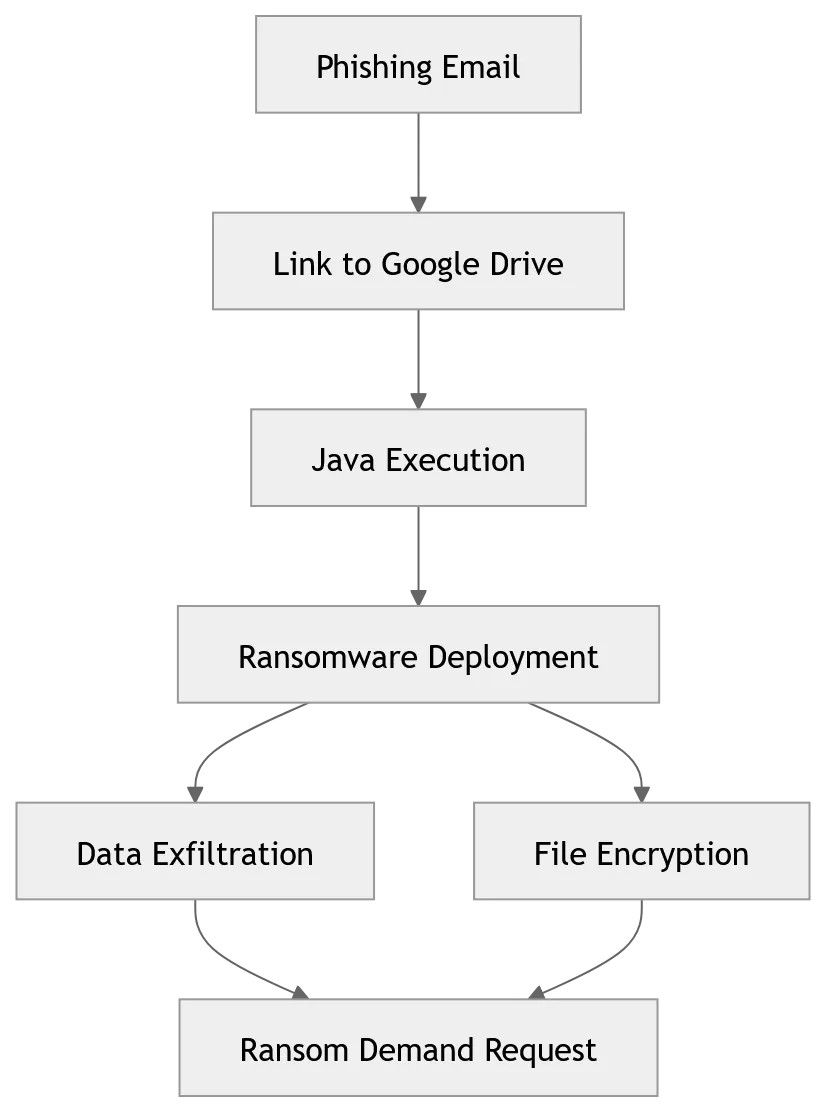
The end‑to‑end attack flow observed in the Acronis analysis, from the initial phishing email to RAT installation, pre‑ransomware reconnaissance, and final file encryption.
The figure highlights how the operators rely on Adwind to maintain long‑term access, using its cross‑platform capabilities to move across different operating systems when needed before triggering the JanaWare component.
This layered strategy allows the attackers to adjust their actions based on each victim, deciding whether to deploy ransomware, steal data, or perform both depending on the value of the compromised system.
Infection Mechanism and Customized Adwind Use
The infection mechanism behind JanaWare heavily depends on Adwind, but the version used in these attacks includes notable customizations that extend its role beyond simple remote access.
After the victim opens the initial malicious attachment, the Adwind loader uses obfuscated scripts and multi‑stage deployment to avoid easy detection by antivirus tools, unpacking the RAT into memory and establishing persistence through registry entries, scheduled tasks, or user‑level startup entries.
Acronis researchers observed that this customized variant periodically checks in with its C2 server to request updated configuration data, including instructions on whether and when to drop the JanaWare ransomware module.
The infection chain shows how the malicious document hands off execution to a script loader, which then pulls the Adwind payload and sets up the communication channel back to the attackers.
This design lets the operators separate the phishing infrastructure from the core malware, enabling them to rotate lures quickly while reusing the same RAT and ransomware components in the background.
It also means defenders who only focus on blocking suspicious attachments may miss later‑stage traffic or payload delivery that happens through Adwind’s C2 channel.
Once Adwind is active, it collects system information such as hostname, operating system version, installed software, and a list of user files and folders, sending this inventory back to the attacker for review.
Based on this profile, the operators can selectively deploy JanaWare by instructing the RAT to download and execute the ransomware from a remote server, often using encrypted or encoded channels to evade inspection.
Before encryption begins, the ransomware process may attempt to disable local security tools, terminate backup‑related services, and delete shadow copies to reduce the chance of recovery without paying.
Throughout this stage, both the RAT and the ransomware use simple but effective detection‑evasion tactics such as common process names, basic anti‑analysis checks, and environment awareness to limit their exposure to automated analysis systems.
To reduce the risk from JanaWare and similar RAT‑based ransomware operations, organizations and users in Turkey should prioritize email filtering, user awareness training, and strict controls on running unknown scripts and attachments, especially those delivered in local language and business‑themed formats.
Endpoint protection solutions that can detect RAT behavior, suspicious C2 traffic, and sudden file‑encryption patterns are also critical, as they provide multiple chances to interrupt the attack chain before JanaWare executes.
Maintaining regular, offline backups; keeping operating systems and applications patched; and closely monitoring remote‑access tools can significantly limit the damage if a system is compromised, even when attackers attempt to hide behind customized Adwind components.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.