Dragon Boss Supply Chain Attack Exposes 25,0 Endpoints Exposed
A sophisticated supply chain attack, now associated with the name “Dragon Boss,” has led to the exposure of 25,000 endpoints. This significant compromise stemmed from a breach within the...
A sophisticated supply chain attack, now associated with the name “Dragon Boss,” has led to the exposure of 25,000 endpoints. This significant compromise stemmed from a breach within the Dragon Boss Solutions Update Domain and was first detected following a series of routine adware alerts that quickly escalated into a far more serious incident. Cybersecurity researchers have published a
Dragon Boss Solutions LLC presents itself as a company engaged in “search monetization research.” Its signed software, however, had a much darker purpose.
Running with full SYSTEM privileges, these executables silently fetched and deployed payloads capable of disabling security products across infected machines.
The antivirus-killing behavior was first observed in late March 2025, though the underlying loaders and updaters had been present on victim systems since late 2024.
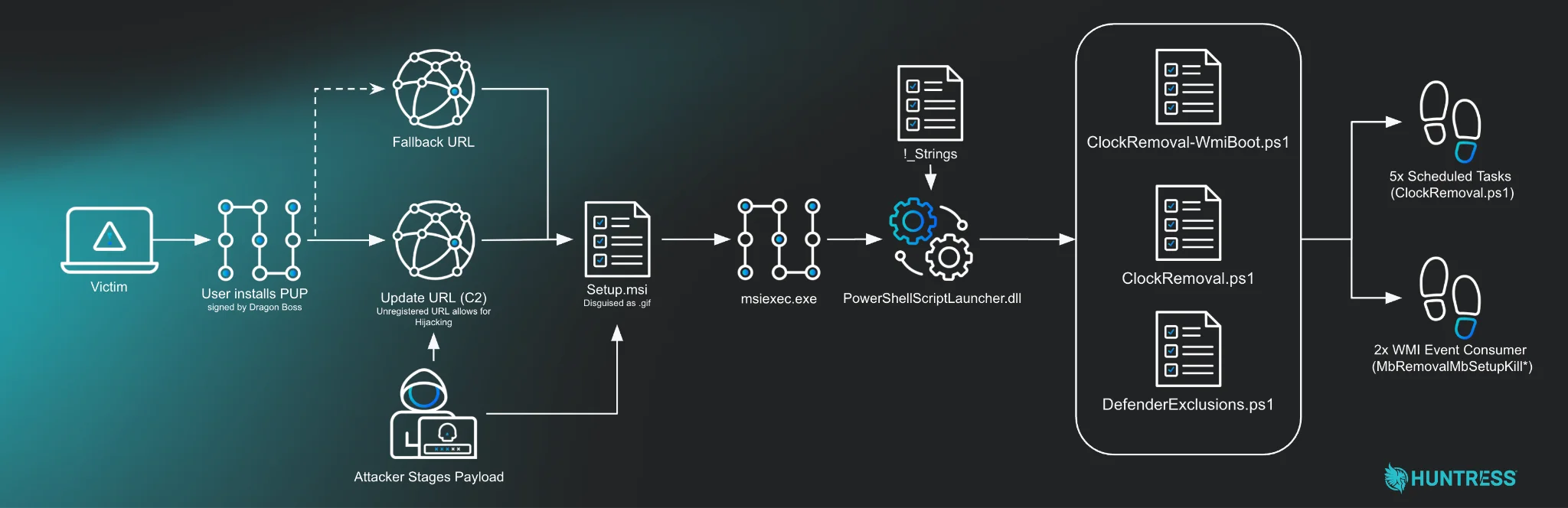
The operation used Advanced Installer, a legitimate off-the-shelf update tool, to deliver MSI and PowerShell-based payloads while hiding behind a layer of apparent legitimacy.
Huntress researchers James Northey and Ryan Dowd identified the threat after WMI persistence signals began triggering across managed environments.
Tracing the activity back, they discovered a signed executable named RaceCarTwo.exe as the origin of the entire infection chain.
From there, the attack deployed Setup.msi, which in turn executed a PowerShell script called ClockRemoval.ps1 — a powerful AV killer that not only shut down security processes but actively blocked any attempt to reinstall them.
What made the situation especially alarming was a critical flaw baked right into the update configuration.
The primary update domain, chromsterabrowser[.]com, was completely unregistered, meaning anyone willing to spend roughly $10 to register it would instantly gain the ability to push any payload to every infected endpoint running that software variant.
Huntress registered the domain first, pointed it to a sinkhole, and within hours, tens of thousands of infected systems began reaching out looking for instructions — ransomware, an infostealer, or anything else entirely.
Over a 24-hour monitoring window, 23,565 unique IP addresses connected to the sinkhole, confirming the true scale of live infections worldwide.
The geographic spread of the campaign was significant. The United States had the highest infection count with 12,697 hosts (53.9%), followed by France at 2,803 (11.9%), Canada at 2,380 (10.1%), the United Kingdom at 2,223 (9.4%), and Germany at 2,045 (8.7%).
Among all infections, 324 were traced to high-value networks, including 221 universities and colleges, 41 operational technology networks tied to electric utilities and critical infrastructure, 35 government entities, 24 primary and secondary schools, and 3 healthcare organizations. Multiple Fortune 500 company networks were also among those affected.
Inside the AV-Killing Payload
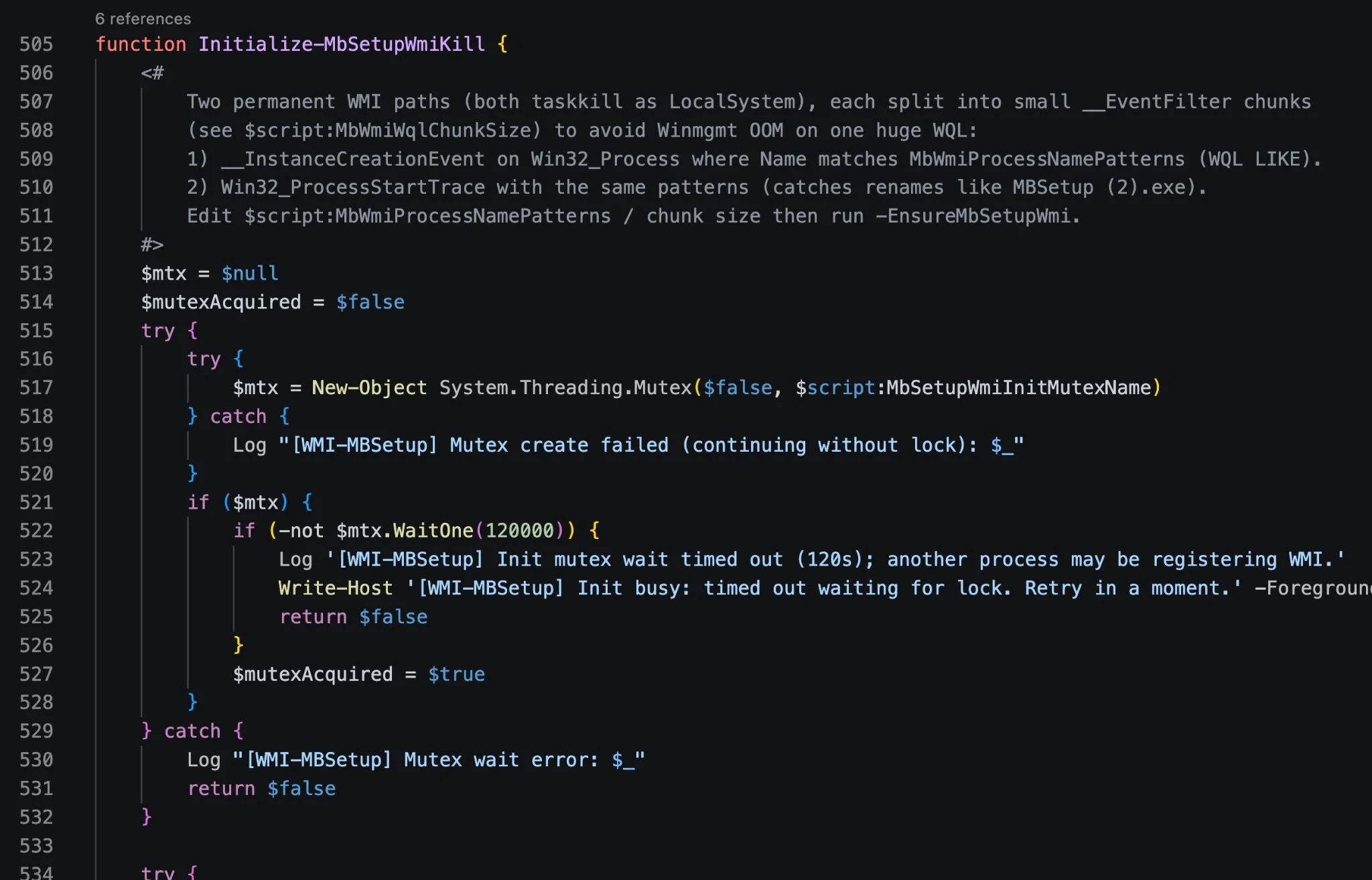
The ClockRemoval.ps1 script was the core of the attack’s destructive capability. Once deployed through the MSI update package, it ran a thorough sweep of the infected system — killing antivirus processes, stripping their services through registry manipulation, and creating five scheduled tasks running as SYSTEM.
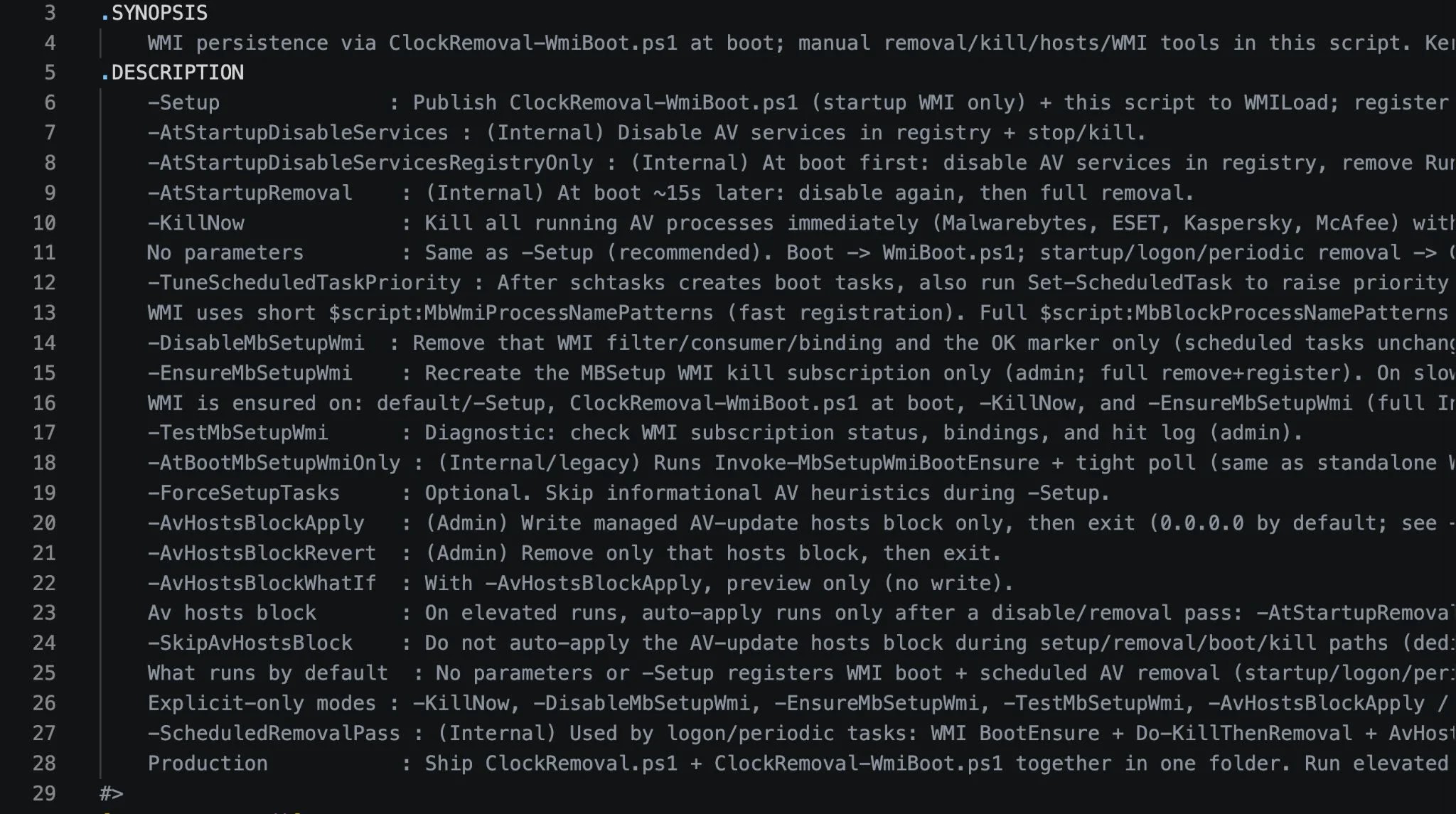
These tasks — ClockSetupWmiAtBoot, DisableClockServicesFirst, DisableClockAtStartup, RemoveClockAtLogon, and RemoveClockPeriodic — ensured that security tools were removed on every boot, startup, and every 30 minutes.
The script also modified the Windows hosts file to redirect AV vendor update domains, including those for Malwarebytes and Kaspersky, to 0.0.0.0, cutting off all reinstallation routes.
It added Windows Defender exclusions for paths like DGoogle, EMicrosoft, and DDapps — believed to be staging directories for future payloads.
Dragon Boss Solutions-signed Chrome binaries were also observed running with the flag --simulate-outdated-no-au="01 Jan 2199", permanently disabling Chrome’s auto-update feature.
Security teams should hunt for WMI event subscriptions containing “MbRemoval” or “MbSetup” in the consumer name, monitor scheduled tasks pointing to WMILoad directories or ClockRemoval scripts, flag any processes signed by Dragon Boss Solutions LLC, inspect the hosts file for blocked AV vendor domains, and check Windows Defender exclusion paths for suspicious entries such as DGoogle, EMicrosoft, or DDapps.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.