Hackers Google Tasks Notifications in New Phishing Attack
Alright, so here’s something you need to know: Hackers Abuse Google Tasks notifications – yeah, those little reminders – to target a massive number of businesses. We’re talking over 3,000 organizations worldwide, primarily in the manufacturing sector.
The December 2025 attacks signal a dangerous shift in email-based threats, in which attackers abuse legitimate Google infrastructure rather than spoofing domains or forging email headers.
The phishing emails originated from a legitimate Google address [email protected] and successfully passed all major email authentication protocols, including SPF, DKIM, DMARC, and CompAuth.
This allowed malicious messages to bypass traditional email security gateways that rely on sender reputation and domain trust, RavenMail told Cybersecurity News.
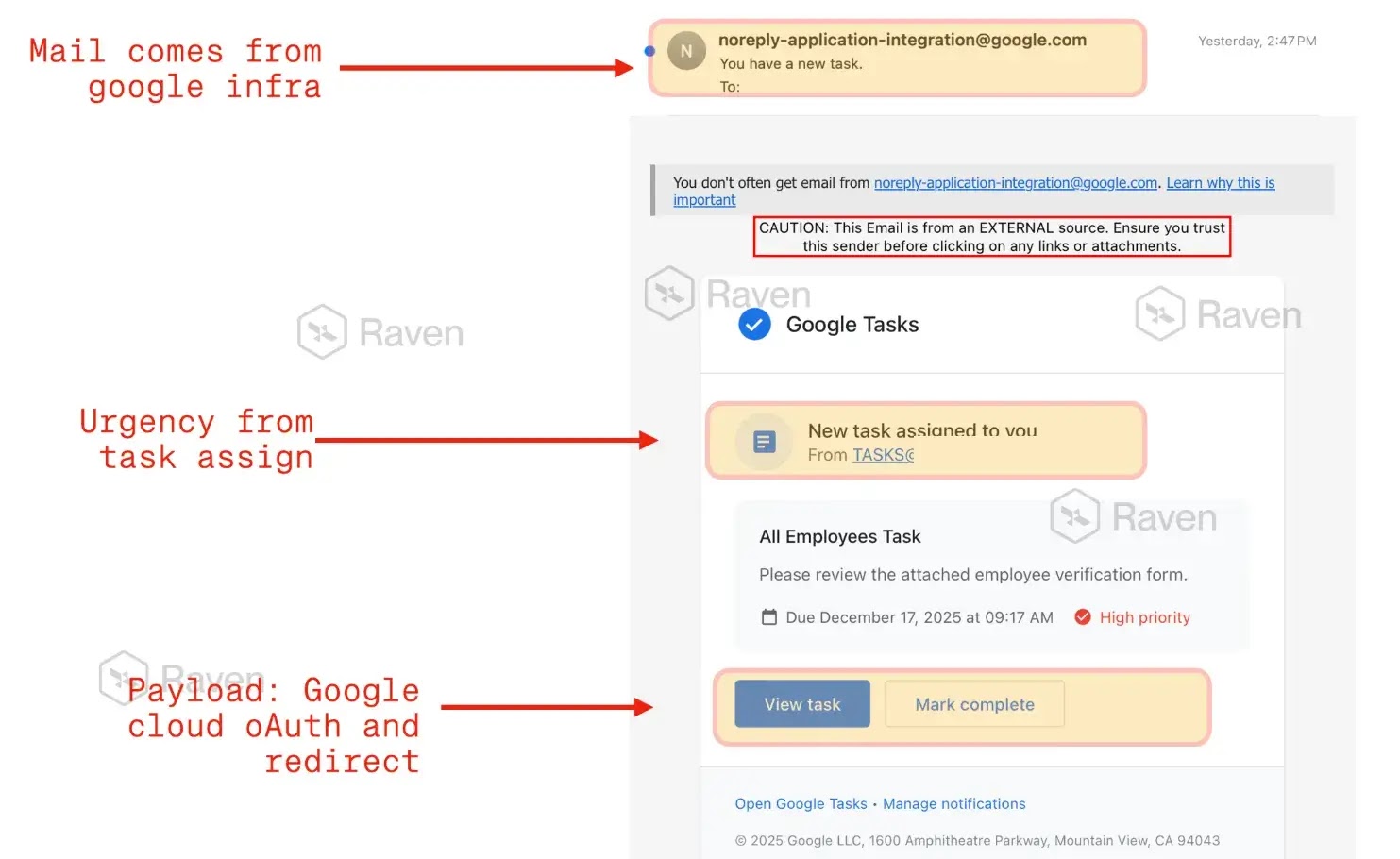
The emails impersonated Google Tasks notifications, presenting what appeared to be an “All Employees Task” requesting urgent employee verification.
Recipients were prompted to click buttons labeled “View task” or “Mark complete,” which redirected them to a malicious page hosted on Google Cloud Storage.
Phishing Campaign Exploits Trusted Google Service
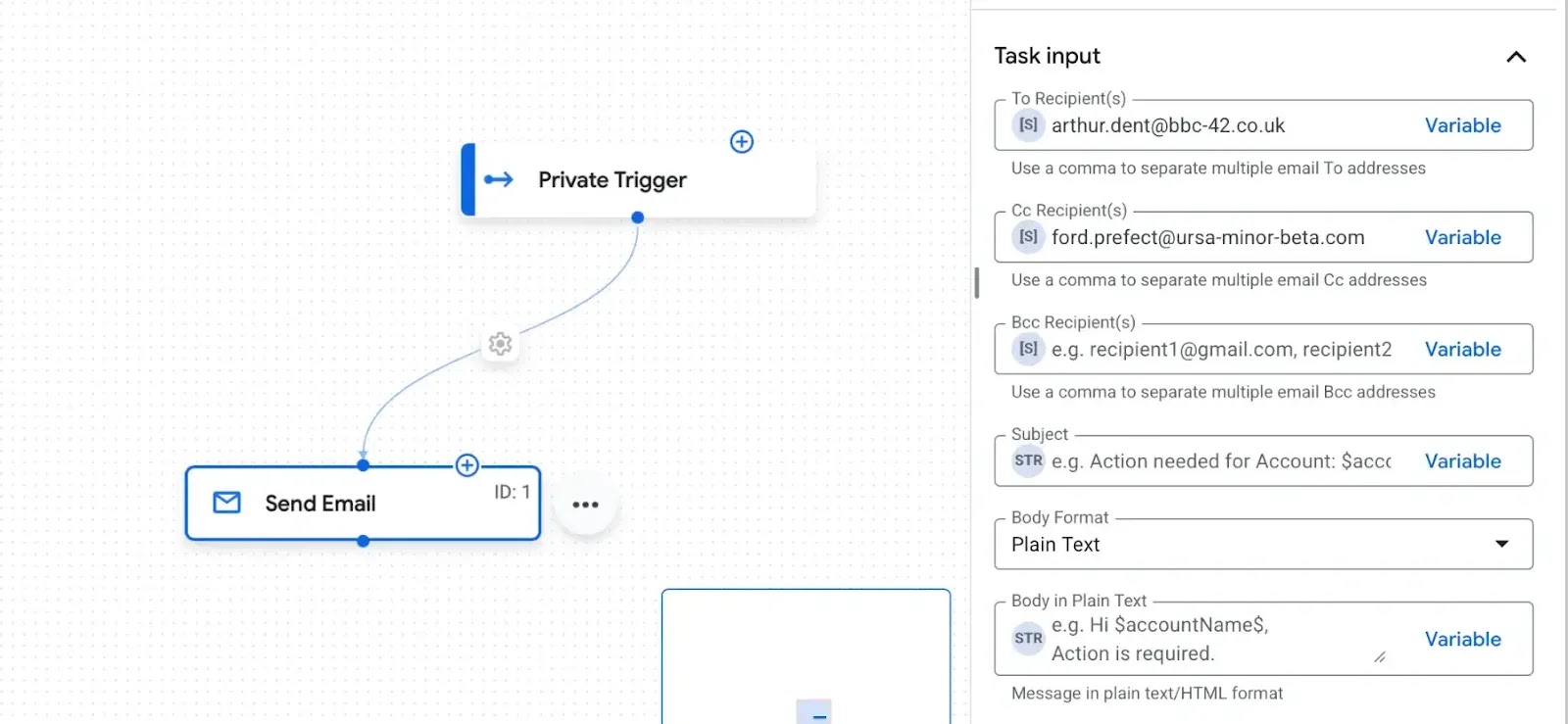
Attackers exploited Google’s Application Integration service to send emails from legitimate Google infrastructure, inheriting Google’s high sender reputation and universal allowlisting.
The phishing page replicated Google Tasks branding with high accuracy, including familiar UI elements, legitimate footer text, and authentic-looking call-to-action buttons.
The attack redirected victims to URLs hosted on Google Cloud Storage (storage.cloud.google.com), rendering traditional URL-reputation-based detection ineffective.
The messages used psychological triggers, including authority framing, urgency indicators, and minimal explanation, to encourage immediate action without scrutiny. This attack represents a fundamental challenge to email security.
Since the sender was Google, authentication checks passed, domains were trusted, and no suspicious attachments were present, conventional security tools found nothing to block.
Threat researchers have documented similar campaigns that abuse Google Classroom, Google Forms, and AppSheet to harvest credentials.
RavenMail detected the campaign by analyzing contextual mismatches rather than relying on domain reputation.
The security platform identified that Google Tasks was being used for HR verification as anomalous and that Cloud Storage URLs were inconsistent with legitimate Google Tasks workflows. Security experts warn that this is not isolated to Google.
Attackers are increasingly abusing trusted platforms, including Salesforce and Amazon SES, to deliver phishing attacks within legitimate systems.
The shift from infrastructure-level spoofing to workflow abuse requires organizations to rethink email security beyond traditional authentication signals.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.