IDE Flaws: Cursor, Windsurf, Google Antigravity IDEs
Millions of developers could unknowingly install malicious software extensions due to a critical security flaw identified in popular AI-powered development environments. The Cursor, Windsurf, and
Millions of developers could unknowingly install malicious software extensions due to a critical security flaw identified in popular AI-powered development environments.
The Cursor, Windsurf, and Google Antigravity IDEs, with over a million users combined, were found recommending extensions that don’t exist in their respective marketplaces.
These tools, all forked from VSCode, inherited configuration files pointing to Microsoft’s extension marketplace, which they cannot legally use.
Instead, they rely on OpenVSX, an open-source alternative. The vulnerability stems from two types of automatic recommendations.
Overview: Supply-Chain Threats in Developer Tools
File-based recommendations trigger when opening specific files, for example, launching azure-pipelines.yaml prompts an Azure Pipelines extension suggestion.
Software-based recommendations are triggered when applications such as PostgreSQL are detected on a user’s machine.
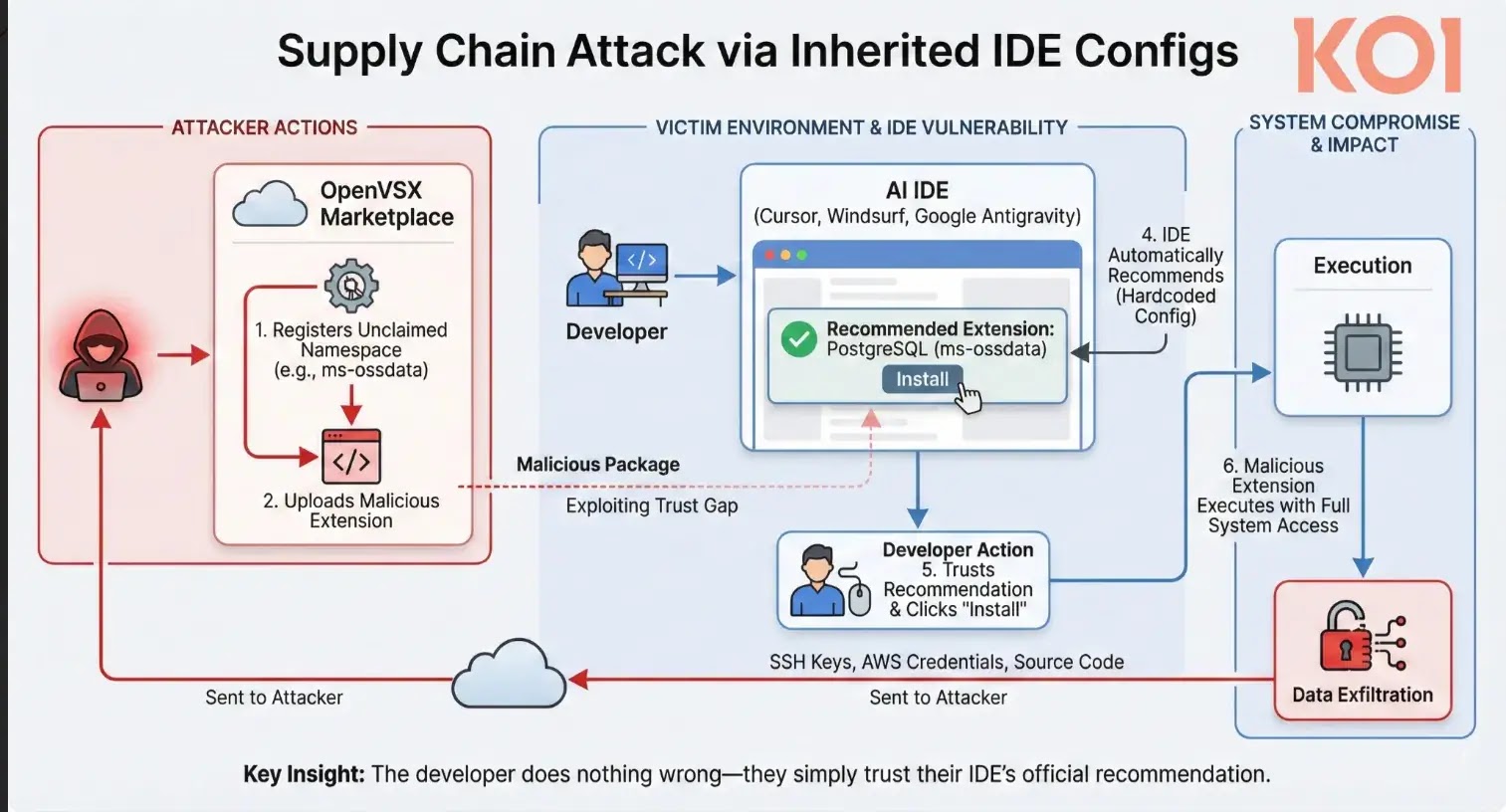
Researchers discovered these recommended extensions didn’t exist on OpenVSX, leaving their namespaces unclaimed.
Any attacker could register these namespaces and upload malicious extensions that would appear as official IDE recommendations.
To demonstrate the risk, security researchers first claimed the vulnerable namespaces, uploading placeholder extensions with clear warnings that they contained no functionality.
Despite this, over 1,000 developers installed these extensions simply because their IDE recommended them, proving the dangerous level of trust users place in automated suggestions.
The claimed namespaces included ms-ossdata. vscode-postgresql, ms-azure-devops. Azure Pipelines, and several others, are tied to common development workflows.
These placeholders received more than 500 installations despite lacking icons and explicitly stating their purpose.
The disclosure timeline reveals mixed vendor responses. Reported on November 23-24, 2025, Cursor acknowledged and fixed the issue by December 1.
Google initially closed the report as “Won’t Fix” twice before accepting the vulnerability and shipping a partial fix on December 26. Windsurf never responded to the disclosure.
The Eclipse Foundation, which operates OpenVSX, collaborated with Koi researchers to verify remaining namespaces and implement additional security measures across the registry.
This vulnerability highlights extension marketplaces as an emerging attack vector in the software supply chain.
The Koi research demonstrates how easily trust in development tools can be exploited, potentially granting attackers access to SSH keys, AWS credentials, and source code without traditional phishing or social engineering.
Security experts warn that as AI IDEs continue to gain adoption, rigorous validation of extension recommendations becomes critical to prevent widespread compromise of development environments.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.