Threat Actors Use Commodity Loader in Targeted Email Attacks
Security researchers have uncovered a highly sophisticated malware campaign that leverages a commodity loader, observing its distribution across multiple threat actor groups. The operation targets...
Security researchers have uncovered a highly sophisticated malware campaign that leverages a commodity loader, observing its distribution across multiple threat actor groups.
The operation targets manufacturing and government organizations across Italy, Finland, and Saudi Arabia with precision-engineered attacks designed to extract industrial data and compromise sensitive administrative credentials.
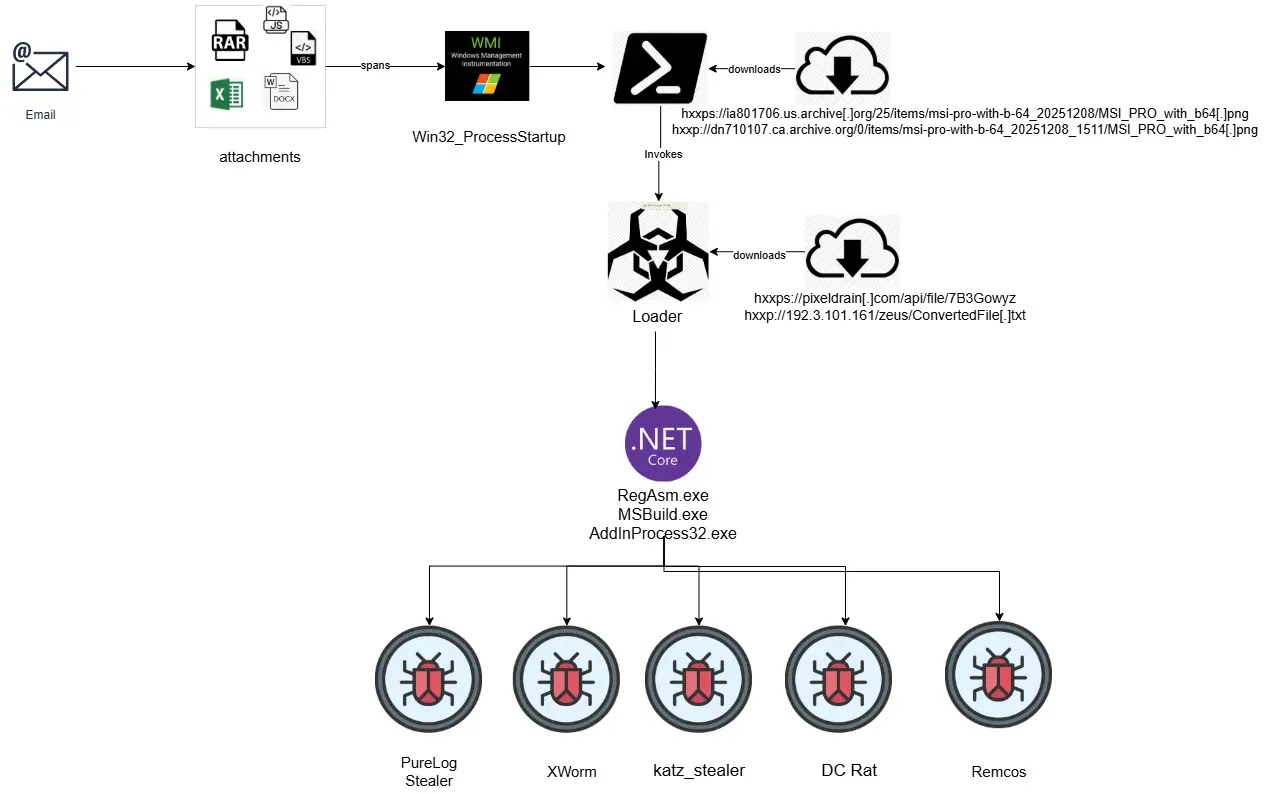
The campaign demonstrates advanced tradecraft through diverse infection vectors including weaponized Office documents exploiting CVE-2017-11882, malicious SVG files, and ZIP archives containing LNK shortcuts.
Each delivery method converges on a unified commodity loader that serves as the foundation for distributing Remote Access Trojans and information-stealing malware.
What sets this operation apart is its sophisticated multi-layered defense evasion approach, combining steganography, trojanized open-source libraries, and a custom four-stage evasion pipeline designed to minimize forensic footprints.
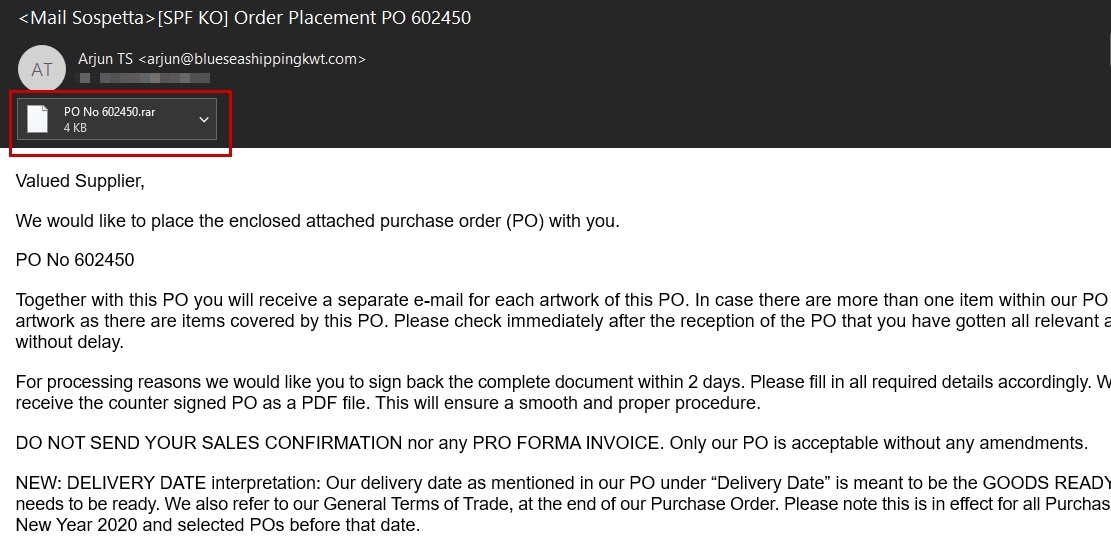
The phishing emails masquerade as legitimate Purchase Order communications from trusted business partners, creating a deceptively simple initial infection vector that belies the technical complexity lurking underneath.
Once recipients open the attachments, a carefully orchestrated infection chain unfolds.
Cyble analysts identified the malware after the second stage of execution, allowing researchers to map the complete attack workflow and understand its operational mechanics.
Steganography and Fileless Execution: The Core Attack Mechanism
The infection chain begins with JavaScript files contained in RAR archives, which execute heavily obfuscated code designed to evade detection systems.
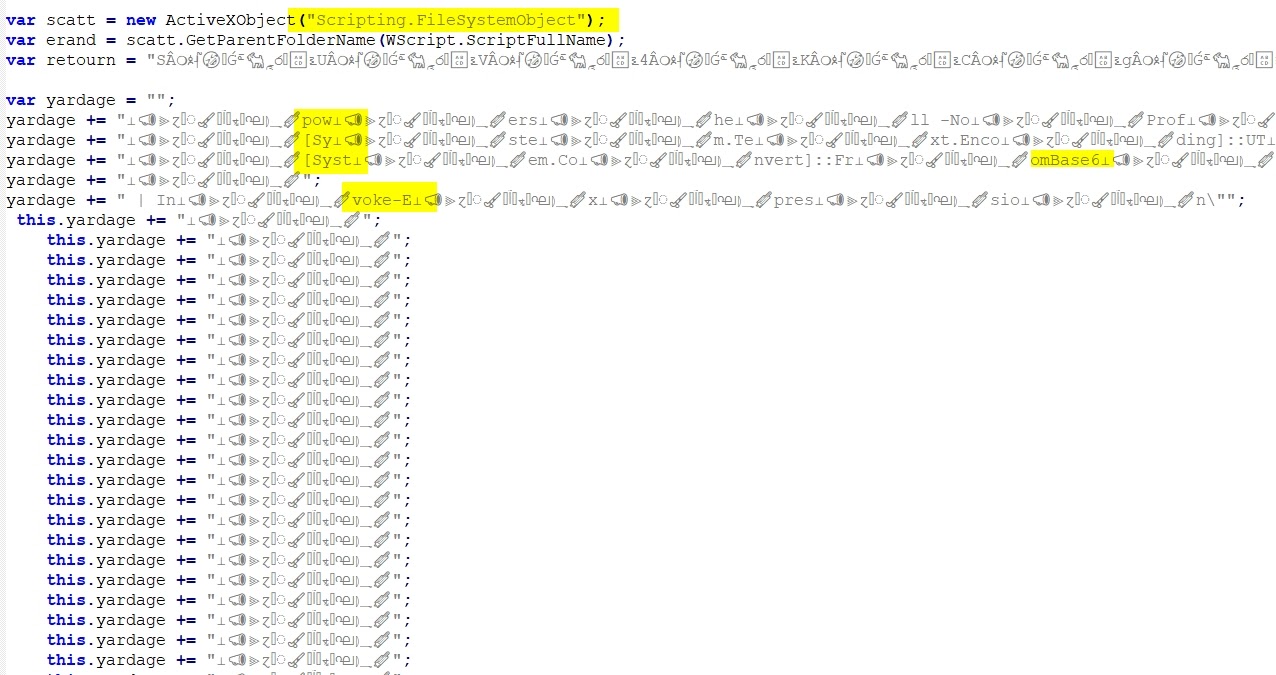
The JavaScript spawns hidden PowerShell processes using Windows Management Instrumentation (WMI), employing multiple obfuscation layers including base64 encoding and string manipulation techniques alongside a deliberate five-second sleep delay to circumvent automated sandbox analysis.
The second stage involves downloading PNG image files from Archive.org, which contain steganographically embedded payloads. PowerShell uses regular expression pattern matching to extract the hidden base64-encoded .NET assembly using specific delimiters.
The assembly then loads reflectively into memory via Reflection.Assembly::Load, ensuring the final payload executes without touching the disk.
This fileless execution technique represents a critical advantage for threat actors, significantly reducing detection probability and complicating forensic investigations.
The third stage leverages a trojanized version of the legitimate open-source TaskScheduler library from GitHub.
Threat actors appended malicious functions to the original source code and recompiled it, creating an assembly that retains authentic appearance and functionality while embedding hidden capabilities.
The loader creates suspended processes using RegAsm.exe, performs process injection, and executes the decoded payload. The final delivered malware is PureLog Stealer, extracted using Triple DES decryption in CBC mode with PKCS7 padding and GZip decompression.
The consistent use of steganography, string reversal, base64 encoding, and process hollowing across campaigns suggests this loader represents a shared delivery framework among multiple threat actors, indicating potential commoditization of this sophisticated attack infrastructure.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.