Google Secures Chrome Sessions to Prevent Cookie Theft
Google announced the public rollout of Device Bound Session Credentials (DBSC) for Windows users on Chrome 146. According to the Google Account Security and Chrome teams, this major security update...
Google announced the public rollout of Device Bound Session Credentials (DBSC) for Windows users on Chrome 146.
According to the Google Account Security and Chrome teams, this major security update aims to eliminate session hijacking, a primary method for attackers to compromise user accounts.
The feature will also expand to macOS in an upcoming release, marking a critical industry shift from reactive threat detection to proactive prevention.
The Threat of Cookie Exfiltration
Session theft typically happens when a user accidentally downloads infostealing malware, such as the LummaC2 family. Once inside a system, the malware hunts for existing session cookies stored in the browser’s local files.
Because authentication cookies often stay valid for long periods, threat actors can steal them to bypass passwords entirely. Historically, stopping malware from reading browser memory using only software was nearly impossible, forcing security teams to rely on complex detection methods after a breach had already occurred.
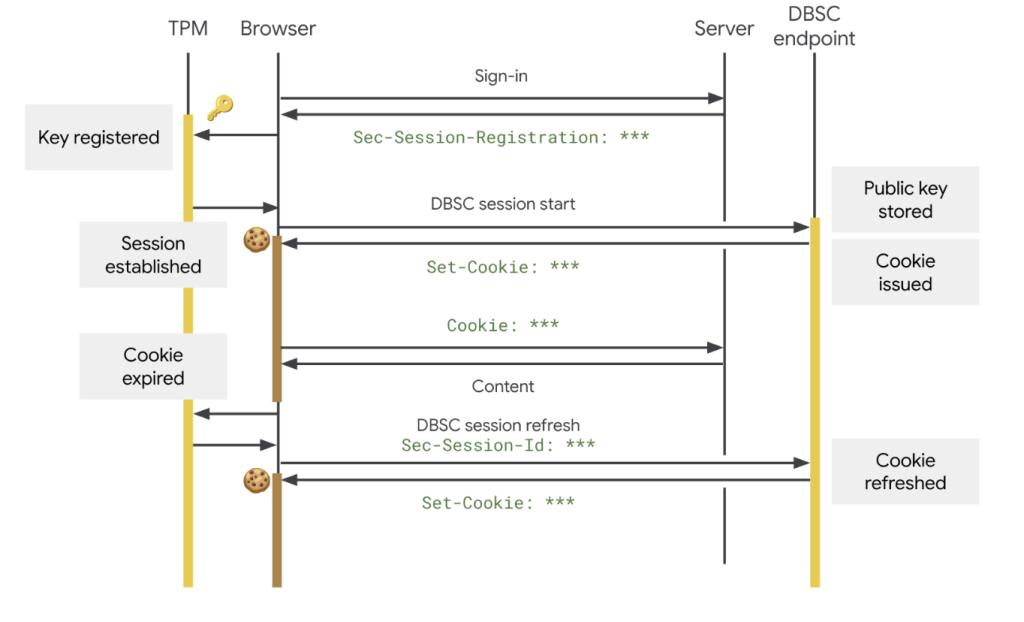
DBSC fundamentally changes web security by tying an authentication session to a user’s physical device. The protocol relies on hardware-backed security modules, like the Trusted Platform Module (TPM) on Windows or the Secure Enclave on Apple devices.
When a user logs in, the hardware generates a unique public-private key pair. Crucially, the private key can never be exported from the machine. Websites that upgrade their backends to support DBSC issue short-lived cookies, and Chrome must constantly prove it holds the private key to refresh them.
If a hacker steals the session cookies, the credentials quickly expire and become useless because the attacker lacks the victim’s physical hardware key. Web developers can implement this seamlessly, as the browser handles the complex cryptography in the background.
Despite its strict device-binding capabilities, DBSC was built with rigorous privacy controls. The protocol uses a completely separate key for every session.
This ensures websites cannot use the technology to track users across different sites or correlate browsing activities. Furthermore, it only shares the minimum data required to prove possession, preventing the tool from being abused for device fingerprinting.
Google developed DBSC as an open web standard alongside the W3C Web Application Security Working Group, partnering closely with Microsoft and conducting trials on platforms such as Okta. Looking ahead, Google plans to expand DBSC capabilities to secure federated identity and Single Sign-On (SSO) environments for enterprises.
The team is also developing advanced registration options to bind sessions to existing hardware security keys, and exploring software-based key support to protect devices that lack physical security hardware.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.








No Comment! Be the first one.