Ransomware Gangs Expand Use of EDR Killers Beyond Vulnerable
Endpoint Detection and Response (EDR) killers have become a standard, potent weapon in modern ransomware intrusions. Before launching file-encrypting malware, cybercriminals routinely deploy...
Endpoint Detection and Response (EDR) killers have become a standard, potent weapon in modern ransomware intrusions. Before launching file-encrypting malware, cybercriminals routinely deploy specialized tools to bypass security software.
According to a comprehensive new report by ESET Research, the threat landscape has grown far beyond the well-known Bring Your Own Vulnerable Driver (BYOVD) technique.
Attackers are now heavily using driverless methods, custom command-line scripts, and legitimate anti-rootkit utilities to turn off security defenses.
Why Attackers Prefer EDR Killers
Instead of constantly rewriting and updating ransomware encryptors to avoid security detection, threat actors find it much easier to turn off the security software first.
EDR killers provide a highly reliable, low-cost solution that gives attackers a predictable window to run their inherently noisy encryption payloads.
Interestingly, ESET notes that ransomware affiliates, rather than the core ransomware-as-a-service operators, usually choose which EDR-killer to deploy in an attack.
This dynamic creates massive tooling diversity in the wild, as different affiliates mix and match various EDR killers to suit their specific intrusion needs and skill levels.
While exploiting vulnerable kernel drivers through BYOVD remains the dominant method, the technology behind EDR killers is rapidly expanding.
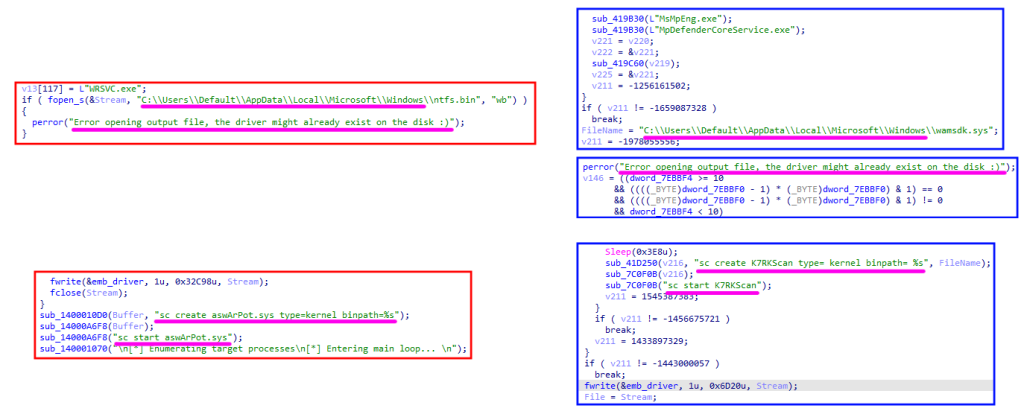
ESET researchers are currently tracking almost 90 EDR killers actively used in the wild, 54 of which rely on BYOVD to exploit 35 different vulnerable drivers.
Some low-skilled attackers rely on basic command scripts or rebooting the system into Windows Safe Mode to bypass security measures. More sophisticated affiliates weaponize legitimate anti-rootkit programs, such as GMER and PC Hunter.

These tools were originally built to remove deep-kernel malware, but their elevated privileges make them ideal weapons for terminating active security processes.
A growing and dangerous trend is the use of driverless EDR killers. Tools like EDRSilencer and EDR-Freeze do not need to interact with the system kernel at all.
Instead, they block network communication between the endpoint and the security backend, or they force the EDR software to freeze in place. Because these methods do not rely on traditional driver vulnerabilities, they are much harder for network defenders to detect.
The ESET investigation categorized the developers of these tools into three main groups. First, closed groups, such as Embargo, DeadLock, and Warlock, develop their own proprietary EDR killers from scratch.
Researchers strongly suspect that groups like Warlock are using Artificial Intelligence to assist with writing and updating their EDR killer code.
Second, many attackers modify publicly available proof-of-concept (PoC) code. Open repositories offer ready-to-use templates that attackers easily tweak by changing the programming language or adding simple code obfuscation.
Finally, a booming underground market now offers “EDR killer as a service”. Commercial tools are actively sold on dark web forums to affiliates of major ransomware gangs, complete with customer support.
Because these tools are heavily traded and shared, cybersecurity defenders face a major challenge. Analyzing a specific vulnerable driver is no longer enough to identify a specific ransomware gang.
Completely unrelated tools might abuse the same driver, and a single threat group might switch between multiple drivers in different attacks.
As the EDR killer market continues to mature and commercialize, organizations must focus on detecting the behavioral signs of security tampering rather than just tracking specific vulnerable drivers.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.