Google Launches Gmail E2EE for Android and iOS Users
Google has officially launched End-to-End Encryption (E2EE) for its Gmail application across Android and iOS platforms. This crucial enhancement specifically targets users who already leverage...
Google has officially launched End-to-End Encryption (E2EE) for its Gmail application across Android and iOS platforms. This crucial enhancement specifically targets users who already leverage Gmail’s client-side encryption capabilities.
It allows organisations to handle sensitive data confidentially directly from their smartphones or tablets. The feature ensures compliance with strict data sovereignty rules while keeping the workflow entirely mobile.
Users can now compose and read encrypted messages natively within the standard Gmail application. There is no longer a requirement to download third-party applications or log into separate secure email portals.
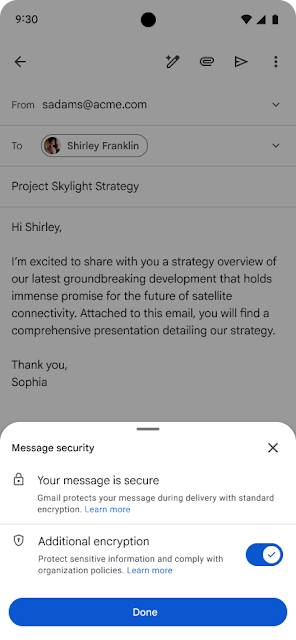
Client-side encryption means the data is scrambled before it ever reaches Google’s servers.
Google holds no keys to decrypt this information, preventing the company from reading your messages under any circumstances. Employees equipped with a proper license can seamlessly send these encrypted communications to anyone.
Seamless Cross-Platform Delivery
Google designed the delivery mechanism to be entirely frictionless for the person receiving the email. If the recipient uses the standard Gmail app, the encrypted message arrives and functions just like a typical email thread.
This creates a highly user-friendly experience that requires no technical knowledge from the receiver. The system also supports external communication, as outgoing encrypted messages are not restricted to Gmail users.
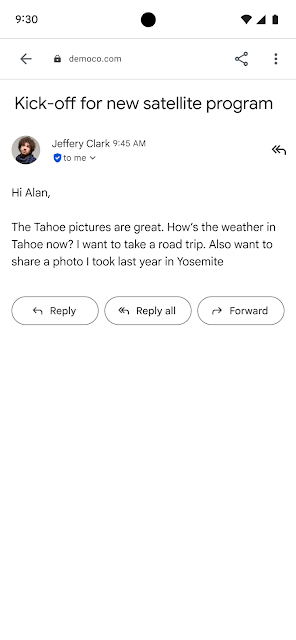
Guest recipients using alternative email services have a straightforward path to access the data. When a non-Gmail user receives the email, they can securely open, read, and reply using their default web browser.
This process authenticates their identity securely without requiring them to create a new account. Once verified, they can view the confidential text and download any encrypted attachments safely.
This eliminates the usual friction associated with sending protected documents to external vendors.
System administrators must take specific actions before employees can utilize these new mobile features. Admins need to log into the Workspace Admin Console and explicitly enable the mobile clients within the encryption interface.
Administrators maintain complete authority over the cryptographic keys and the identity providers used to authenticate users.
Once this backend configuration is complete, the process becomes effortless for end users. To secure a message, a user simply taps the lock icon while drafting an email and selects the additional encryption option.
Rollout and Availability Details
| Requirement Type | Specific Details |
|---|---|
| Current Status | Available now. |
| Release Tracks | Rapid Release and Scheduled Release domains. |
| Required Tier | Enterprise Plus. |
| Required Add-on | Assured Controls or Assured Controls Plus. |
| Supported Platforms | Android and iOS Gmail applications. |
This security update is currently live for eligible organizational accounts requiring the highest levels of data protection. The table below outlines the specific workspace requirements needed to access mobile end-to-end encryption.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.