Critical Chainlit AI Flaws Expose Cloud Environments
Cybersecurity researchers have identified two critical security flaws in Chainlit, a prominent open-source AI framework that records over 700,000 monthly downloads. The vulnerabilities allow...
Cybersecurity researchers have identified two critical security flaws in Chainlit, a prominent open-source AI framework that records over 700,000 monthly downloads.
Table Of Content
The vulnerabilities allow attackers to steal sensitive cloud credentials, leak database files, and take control of enterprise AI environments without user interaction.
Zafran Labs identified these flaws affecting internet-facing deployments across enterprises. Both vulnerabilities have been confirmed in real-world applications.
| CVE ID | Vulnerability Type | CVSS Score | Impact |
|---|---|---|---|
| CVE-2026-22218 | Arbitrary File Read | Critical | Leak cloud API keys, steal sensitive files |
| CVE-2026-22219 | Server-Side Request Forgery (SSRF) | High | Attack internal servers, access cloud metadata |
The Security Flaws
CVE-2026-22218: Arbitrary File Read
Chainlit’s element handling mechanism contains input validation flaws. Attackers can manipulate the /project/element endpoint to read any file accessible to the server by controlling the element’s path property.
This allows theft of environment variables containing AWS secret keys, database credentials, and authentication secrets.
In multi-tenant deployments using LangChain cache, attackers can read. chainlit/.langchain.db to access all users’ prompts and responses, enabling cross-tenant data leakage.
CVE-2026-22219: Server-Side Request Forgery
The SQLAlchemy data layer fails to validate URLs in custom elements. Attackers can force the server to make GET requests to arbitrary targets, including internal services and AWS metadata endpoints.
In AWS deployments with IMDSv1 enabled, this grants access to IAM role credentials at 169.254.169.254. These vulnerabilities can be combined to compromise cloud environments fully.
Attackers obtain cloud credentials through arbitrary file read, then use SSRF to access metadata services and internal APIs.
Once credentials are obtained, attackers gain access to storage buckets, secret managers, and databases. They can perform lateral movement within the cloud account.
The arbitrary file read also enables source code theft and account takeover by forging authentication tokens using stolen secrets.
Chainlit released version 2.9.4 on December 24, 2025, addressing both vulnerabilities. Organizations must immediately upgrade to this version.
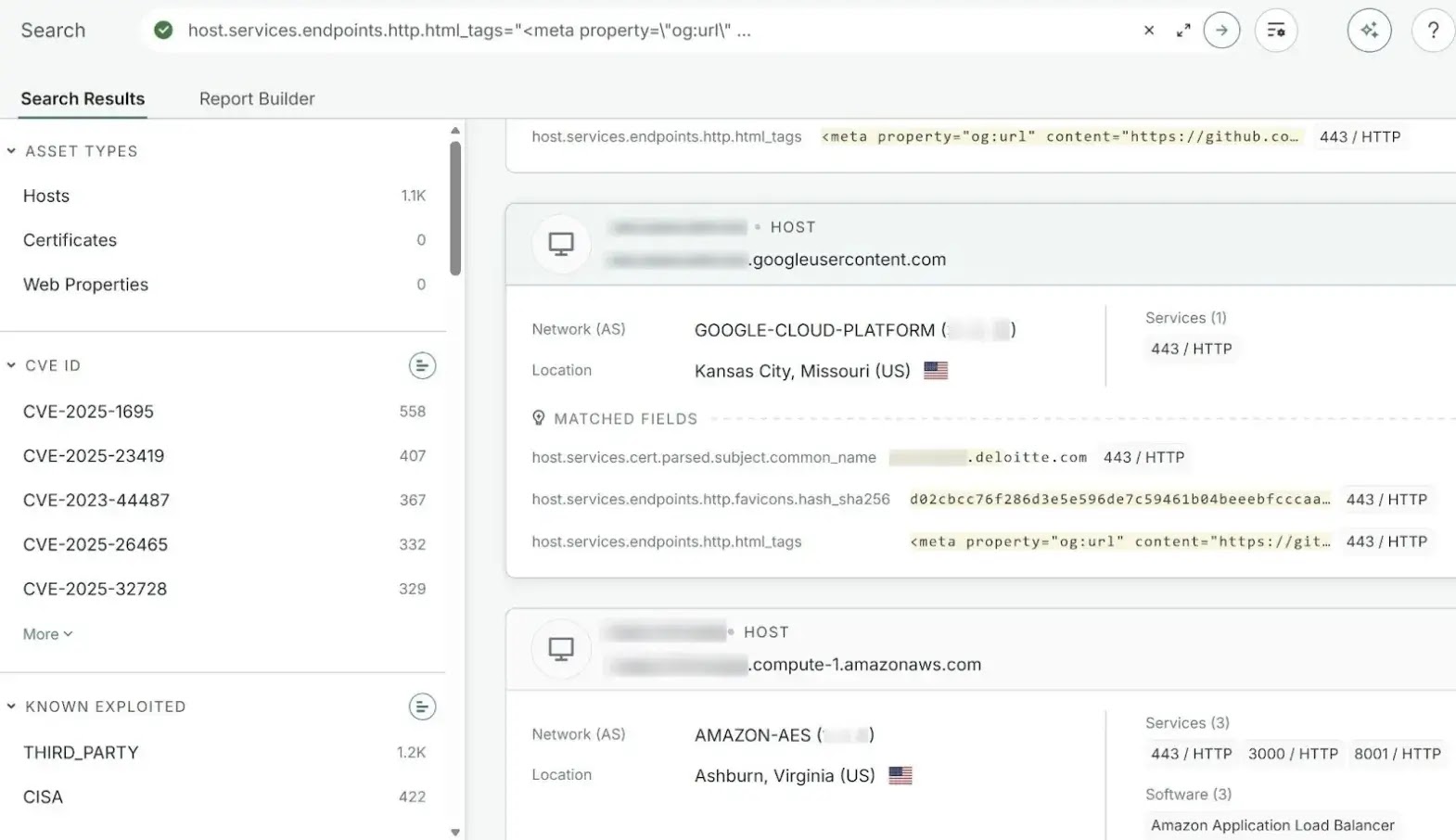
Temporary mitigations include Zafran’s Snort signatures and Cloudflare WAF rules. Enterprises should use asset inventory tools to identify Chainlit instances running versions below 2.9.4.
Zafran disclosed the flaws on November 23, 2025, providing advance notice before public disclosure on January 19, 2026. This discovery launches Project DarkSide, Zafran’s initiative to expose security risks in AI frameworks.
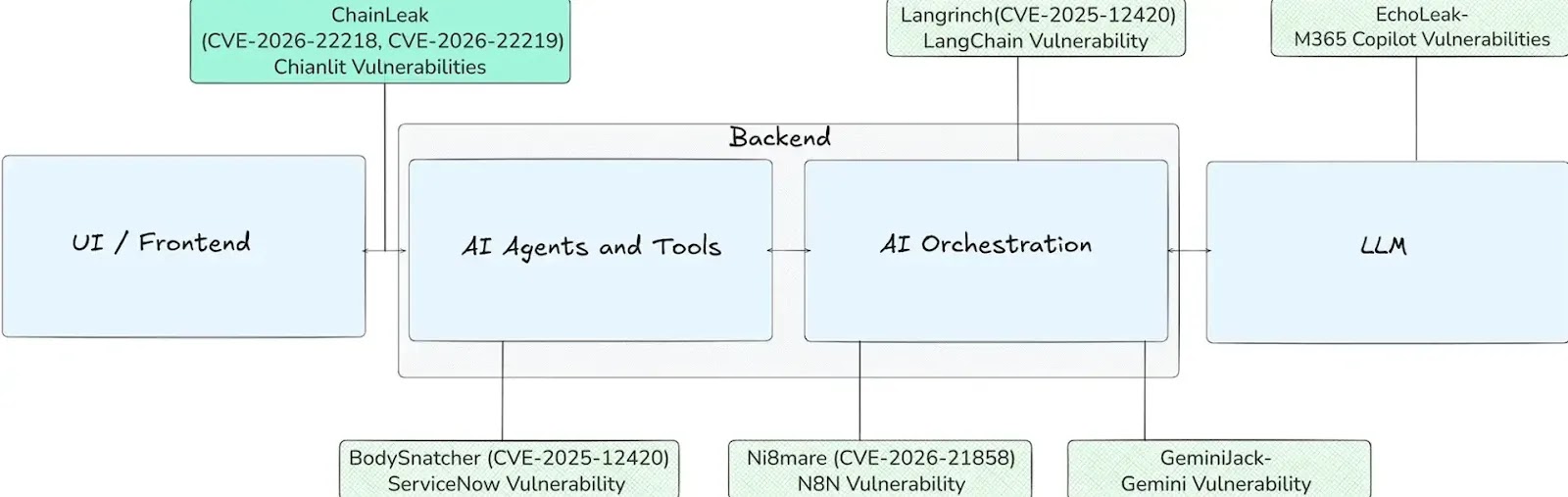
As organizations rapidly adopt AI platforms, traditional vulnerabilities like path traversal and SSRF are being embedded directly into critical infrastructure, expanding the attack surface beyond typical web application security concerns.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.