New AI-Android Malware Auto Clicks Ads on Infected Devices
A dangerous new Android malware campaign has surfaced, specifically targeting users through compromised mobile games and modified pirated streaming applications. The threat, known as Android.Phantom,...
A dangerous new Android malware campaign has surfaced, specifically targeting users through compromised mobile games and modified pirated streaming applications.
The threat, known as Android.Phantom, employs machine learning technology to perform automated ad-click fraud on infected smartphones.
Over 155,000 downloads of compromised games have been recorded, with additional infections spreading through modified versions of Spotify, YouTube, Netflix, and Deezer across unofficial platforms.

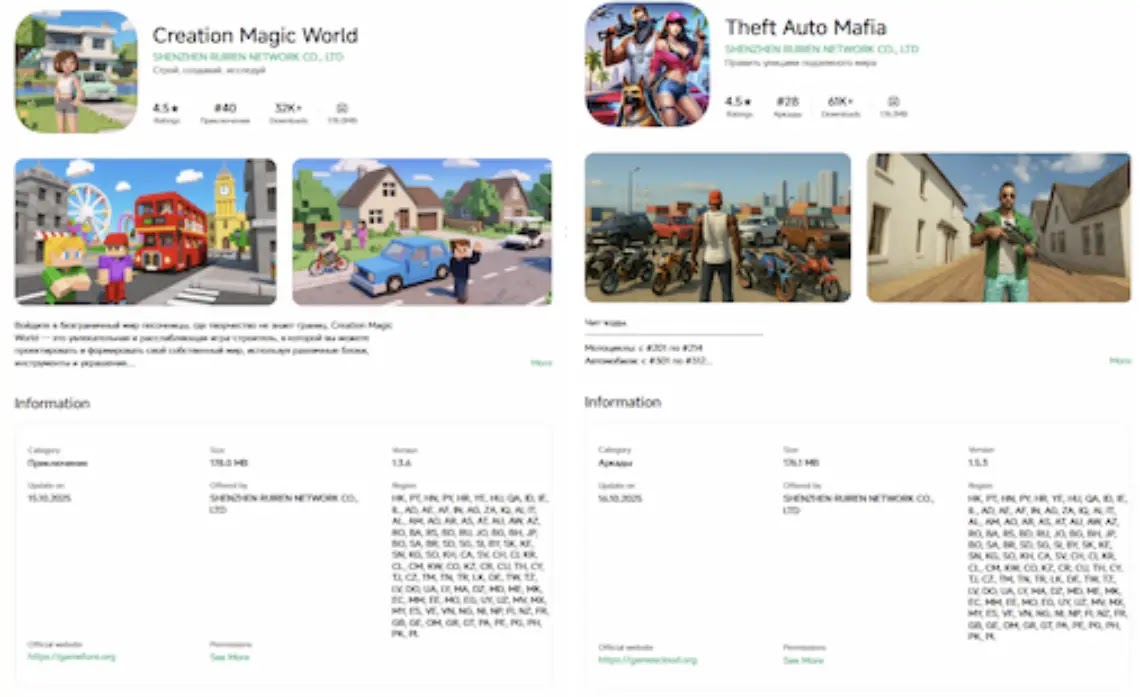
The malware propagates through several channels, including the official GetApps store for Xiaomi devices, where six infected games from developer SHENZHEN RUIREN NETWORK CO., LTD. were discovered.
These apps initially launched without malicious code, but updates released in late September introduced the Android.Phantom trojan.
Distribution extends beyond official stores to dedicated modding websites, Telegram channels attracting tens of thousands of subscribers, and Discord servers where administrators actively promote infected downloads.
Dr.Web researchers noted that Android.Phantom operates using two distinct modes called phantom and signaling. The malware connects to attacker-controlled command servers that dictate its behavior patterns.
Its sophisticated design incorporates TensorFlowJS, a machine learning framework that enables intelligent identification and automated clicking of advertising elements displayed within hidden browsers running on infected devices.
The threat consists of multiple interconnected components. Android.Phantom.2.origin serves as the primary variant, later enhanced by Android.Phantom.5, which functions as a dropper delivering remote code loaders.
These loaders retrieve additional click-fraud modules designed for specific advertising platforms.
How the Machine Learning Attack Works
The phantom mode represents the malware’s most advanced capability, utilizing artificial intelligence for fraudulent ad interactions.
Android.Phantom.2.origin deploys a hidden browser based on WebView widget technology, loading target websites as directed by command servers.
The malware then injects JavaScript automation scripts alongside the TensorFlowJS framework.
An AI model downloaded from external servers analyzes webpage screenshots captured from a virtual screen, identifying clickable advertisement components.
This intelligent approach mimics genuine user behavior, making fraudulent clicks harder for advertising networks to detect compared to basic automated scripts.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.