ClearFake Uses Proxy Execution to Run PowerShell Commands
ClearFake has entered a significantly more dangerous phase. What was once a familiar fake CAPTCHA scam now functions as a highly evasive malware delivery chain. Across hundreds of hacked websites,...
ClearFake has entered a significantly more dangerous phase. What was once a familiar fake CAPTCHA scam now functions as a highly evasive malware delivery chain.
Across hundreds of hacked websites, visitors now see what looks like a routine verification challenge, but behind the scenes the page is preparing to launch hidden code.
Victims only need to follow simple keyboard steps, such as pressing Win + R and paste, for the attack to begin.
This ClearFake wave matters because it blends social engineering with so‑called living off the land tactics, abusing tools already built into Windows as a trusted Windows feature instead of dropping obvious malware files.
By shifting its infrastructure onto blockchain smart contracts and a popular content delivery network, the operation also avoids many domain and IP blocklists that defenders rely on.
Expel analysts and researchers identified this latest evolution while tracking ClearFake’s JavaScript framework across compromised sites and examining the new loader stages.
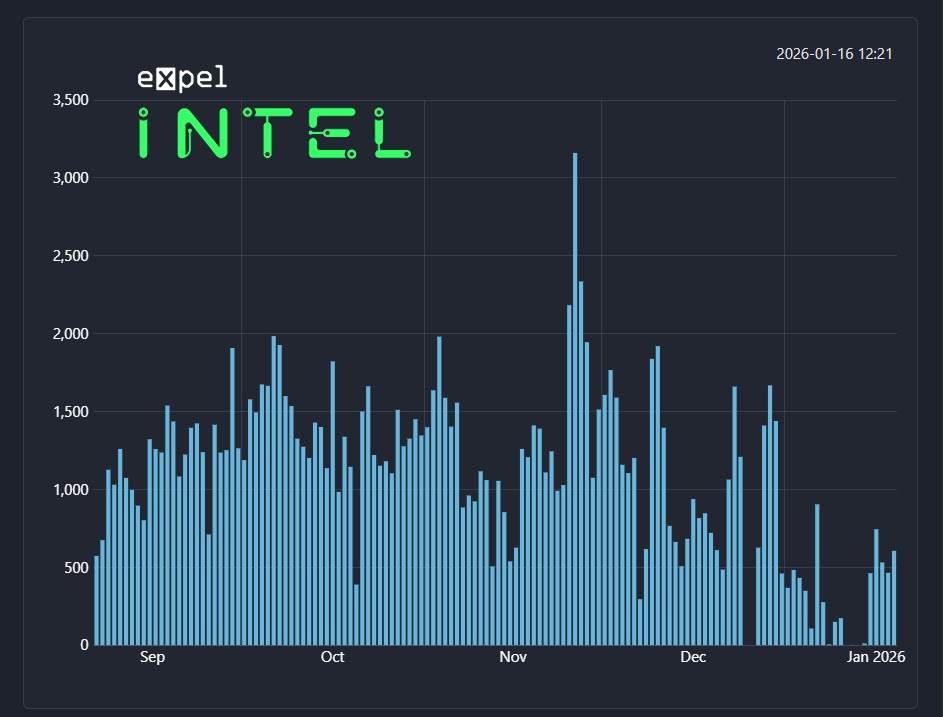
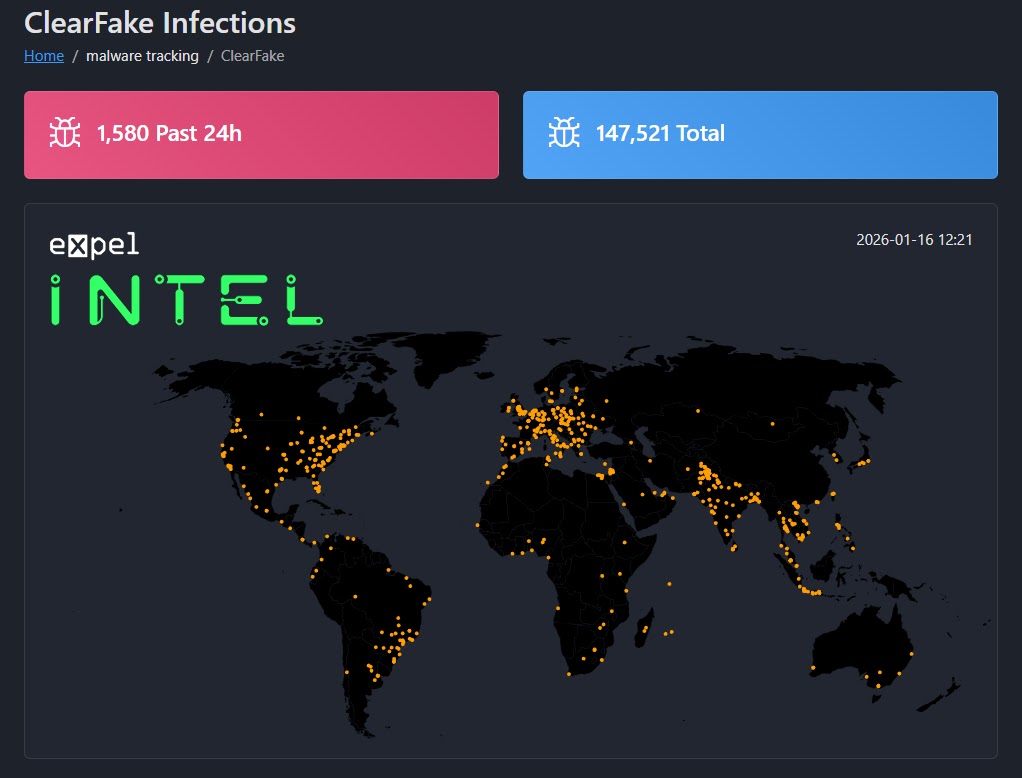
The team linked the campaign to a traffic distribution system that has likely pushed malware to close to 150,000 systems, based on unique IDs stored in a public smart contract visible on the BNB Smart Chain test network.
ClearFake’s operators use the Ethereum‑style contract as a resilient command center, updating encoded JavaScript that infected pages fetch through public Web3 endpoints.
Abusing a Trusted Windows Script for Proxy Execution
This design, combined with hosting later‑stage payloads on jsDelivr, a widely used CDN, means every external touchpoint in the chain sits on services defenders are reluctant to block.
The business impact is clear: a user completing what appears to be a harmless CAPTCHA can unknowingly grant attackers code execution on a trusted corporate endpoint, with little or no trace left on disk.
From there, follow‑on payloads can steal data, deploy additional malware, or provide remote access, all while hiding behind normal‑looking network traffic and legitimate Windows components.
At the heart of the new technique is SyncAppvPublishingServer.vbs, a legitimate script in the Windows System32 folder that ships as part of App‑V management.
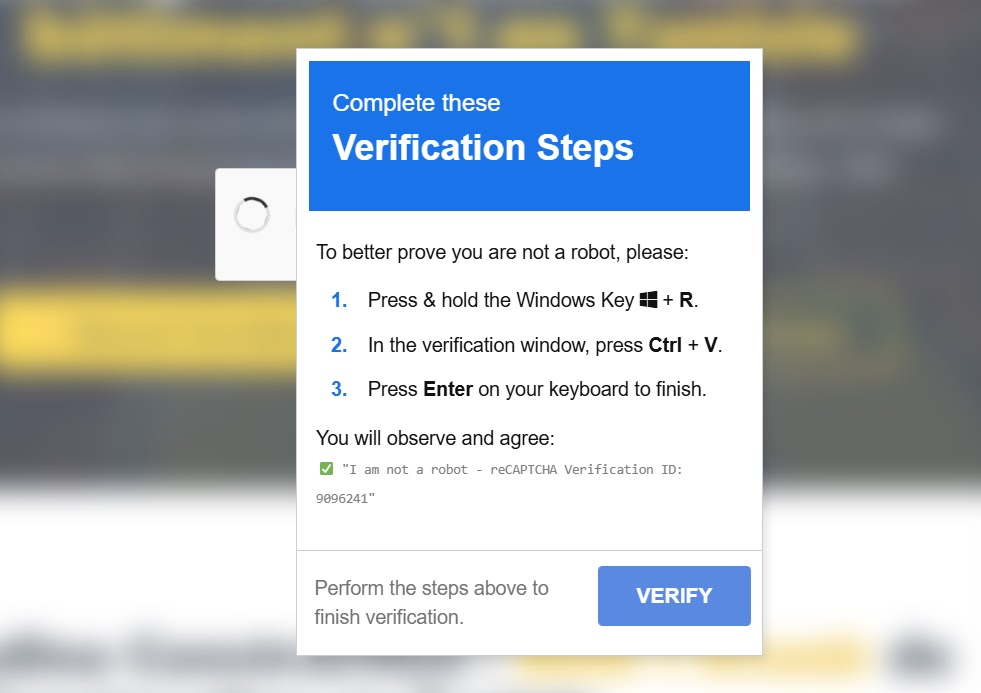
ClearFake’s fake CAPTCHA instructs users to open the Run dialog, where the clipboard holds a carefully crafted command that passes a malicious argument into this script.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.