Chrome Extensions Hijacked 500K VKontakte Infected Users
Over half a million VKontakte users have fallen victim to a sophisticated malware campaign. This operation silently hijacks accounts, exploiting seemingly harmless Chrome extensions as its primary...
Over half a million VKontakte users have fallen victim to a sophisticated malware campaign. This operation silently hijacks accounts, exploiting seemingly harmless Chrome extensions as its primary vector.
The malicious extensions, disguised as VK customization tools, automatically subscribe users to attacker-controlled groups, reset account settings every 30 days, and manipulate security tokens to maintain persistent control.
What appeared as simple theme customization software turned out to be a multi-stage account takeover operation targeting Russia’s largest social network.
The campaign centers around five Chrome extensions sharing the same malicious infrastructure, with the primary extension “VK Styles” alone accumulating 400,000 installations before removal.
The malware operates through a clever two-stage delivery system that evades traditional security scanning.
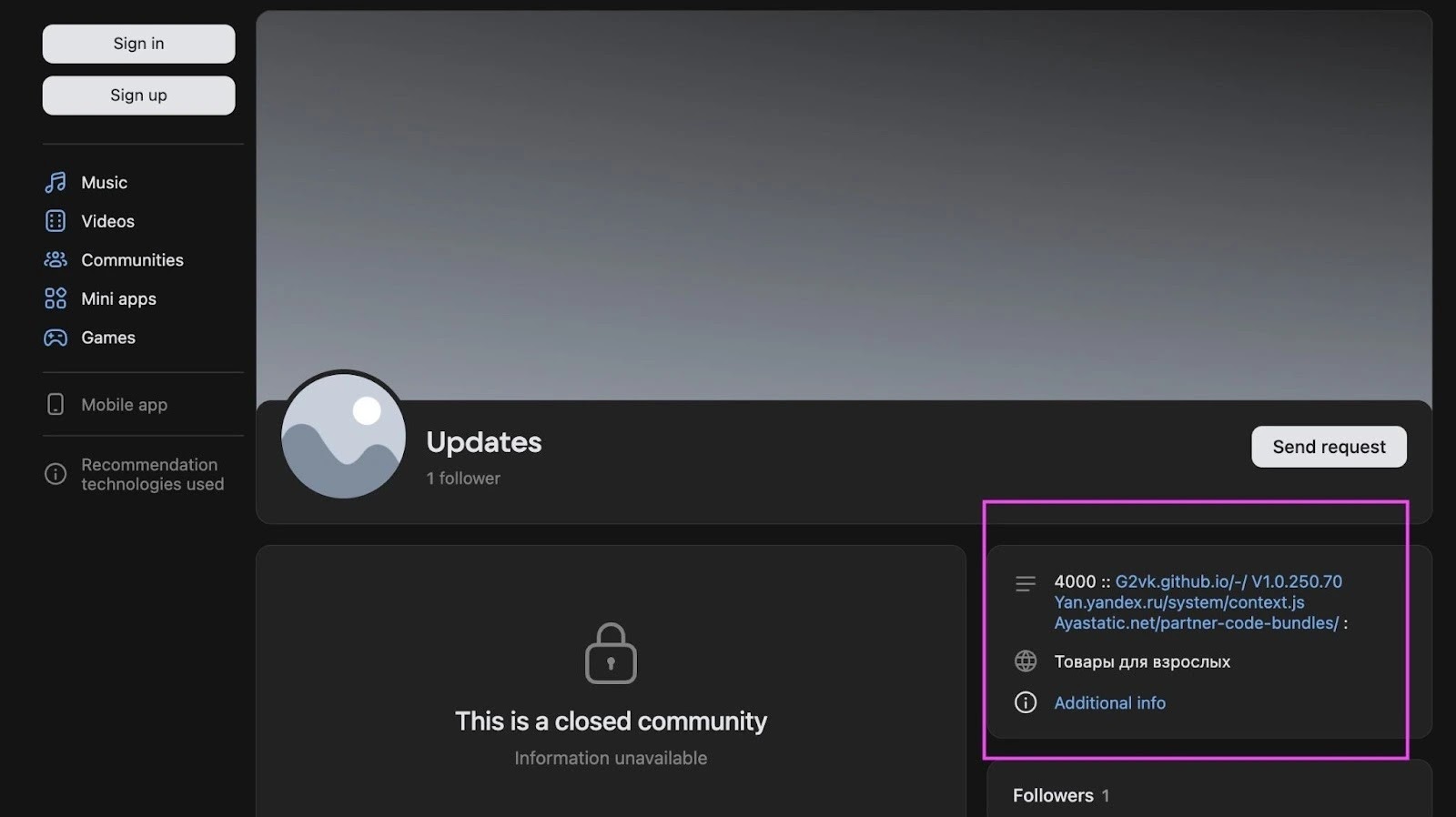
Rather than embedding malicious code directly in the extension, the attackers use a VKontakte profile as command-and-control infrastructure, hiding payload URLs within HTML metadata tags that extensions fetch and execute.
Koi researchers identified this sophisticated threat while investigating extensions injecting Yandex advertising scripts.
Their analysis revealed that the malware calculates metric identifiers dynamically to avoid pattern-matching detection by security tools.
The extensions use obfuscated JavaScript functions to execute arbitrary code fetched from a GitHub repository controlled by the threat actor operating under the username “2vk.”
Multi-Stage Attack Chain Exploits Social Network Infrastructure
The infection mechanism demonstrates advanced evasion techniques. When users install these extensions believing they enhance their VK experience, the malware first establishes persistence by injecting code into every VK page visited.
It then retrieves encoded instructions from the attacker’s VK profile metadata, which directs the extension to download additional payloads from GitHub.
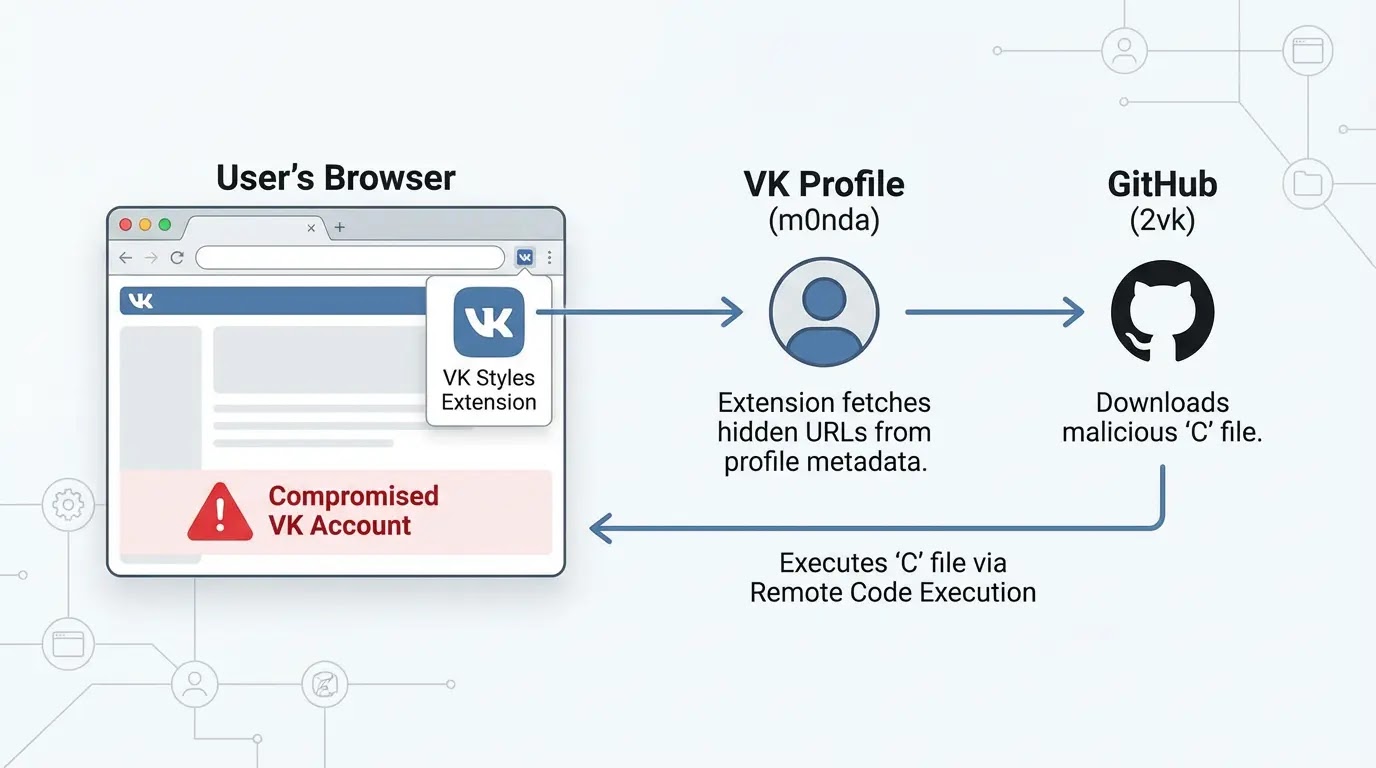
This approach allows the threat actor to update malicious functionality without modifying the extension code itself, bypassing Chrome Web Store security reviews.
The malware manipulates VK’s CSRF protection cookies to bypass security mechanisms designed to prevent unauthorized account actions.
It automatically subscribes victims to the attacker’s VK group with 75% probability on each session, creating a self-propagating distribution network.
Every 30 days, the malware resets account settings to override user preferences and maintain control.
The operation ran continuously from June 2025 through January 2026, with GitHub commit history showing deliberate refinement and feature additions over seven months.
Security teams should audit browser extensions, monitor for unusual VK API activity, and implement extension allowlisting policies.
Users experiencing unexpected group subscriptions or setting changes should immediately remove suspicious VK-related extensions and review their Chrome extension permissions.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.