BodySnatcher Vulnerability Lets Attackers Impersonate ServiceNow
A critical vulnerability in ServiceNow’s Virtual Agent API and the Now Assist AI Agents application enables unauthenticated attackers to impersonate any user and remotely execute privileged AI...
A critical vulnerability in ServiceNow’s Virtual Agent API and the Now Assist AI Agents application enables unauthenticated attackers to impersonate any user and remotely execute privileged AI agents.
Security researcher Aaron Costello from AppOmni disclosed the flaw, tracked as CVE-2025-12420, which combines a hardcoded platform-wide secret with insecure account-linking logic to bypass multi-factor authentication, single sign-on, and other access controls.
The vulnerability affects organizations using ServiceNow’s AI-powered automation features, potentially exposing sensitive customer data, financial records, healthcare information, and intellectual property.
An attacker armed only with a target’s email address can impersonate administrators and weaponize AI agents to create backdoor accounts with full system privileges, granting nearly unlimited access to enterprise resources.
| CVE ID | Affected Application | Affected Versions | Fixed Versions | CVSS Score |
|---|---|---|---|---|
| CVE-2025-12420 | Now Assist AI Agents (sn_aia) | 5.0.24 – 5.1.17, 5.2.0 – 5.2.18 | 5.1.18, 5.2.19 | Critical |
| CVE-2025-12420 | Virtual Agent API (sn_va_as_service) | ≤ 3.15.1, 4.0.0 – 4.0.3 | 3.15.2, 4.0.4 | Critical |
Exploitation Mechanism
The vulnerability exploits two critical design flaws in ServiceNow’s AI agent infrastructure.
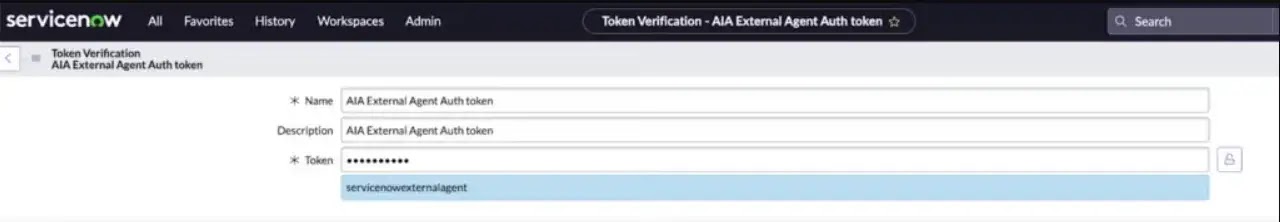
First, AI agent channel providers shipped with identical authentication tokens across all customer instances, creating a universal authentication bypass.
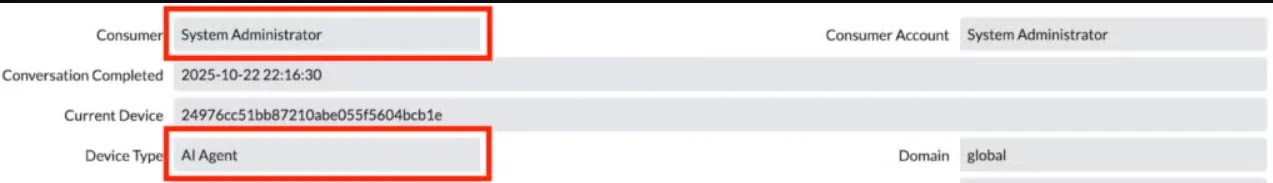
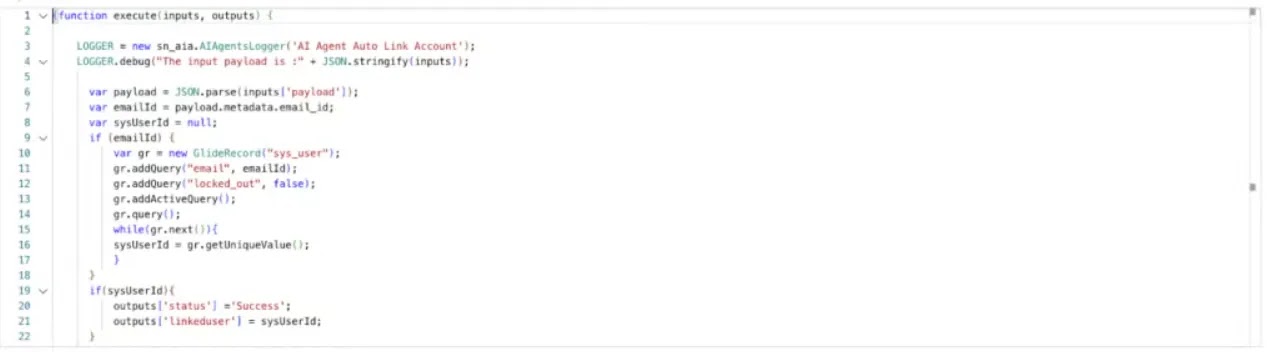
Second, the auto-linking mechanism trusted any requester supplying the shared token along with a valid email address, automatically associating external entities with ServiceNow accounts without requiring multi-factor authentication.
Attackers can chain these weaknesses through the Virtual Agent API to impersonate privileged users and execute the now-removed Record Management AI agent.
In proof-of-concept demonstrations, researchers successfully created administrative accounts, assigned elevated privileges, reset passwords, and achieved full platform access without ever authenticating.
The attack works remotely against any ServiceNow instance running vulnerable application versions, even when affected AI agents remain active. AppOmni reported the vulnerability to ServiceNow on October 23, 2025.
ServiceNow acknowledged the issue immediately and deployed patches by October 30, 2025, rotating provider credentials and removing the powerful Record Management AI agent from customer environments.
The company issued customer notifications and published a knowledge base article, KB2587317, crediting Costello and AppOmni with the discovery.

Security teams should immediately verify that affected applications have been updated to the fixed versions.
Organizations must implement multi-factor authentication for account-linking processes, establish automated review workflows for AI agent deployments, and regularly audit dormant AI agents for deactivation.
ServiceNow administrators can leverage the AI Control Tower application to identify unused agents and enforce approval processes before production deployment.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.