Malicious Chrome GhostPoster Extensions Steal User Data
Seventeen malicious browser extensions, deployed by cybercriminals across Chrome, Firefox, and Edge platforms, have collectively seen over 840,000 downloads, compromising user security for years. The...
Seventeen malicious browser extensions, deployed by cybercriminals across Chrome, Firefox, and Edge platforms, have collectively seen over 840,000 downloads, compromising user security for years.
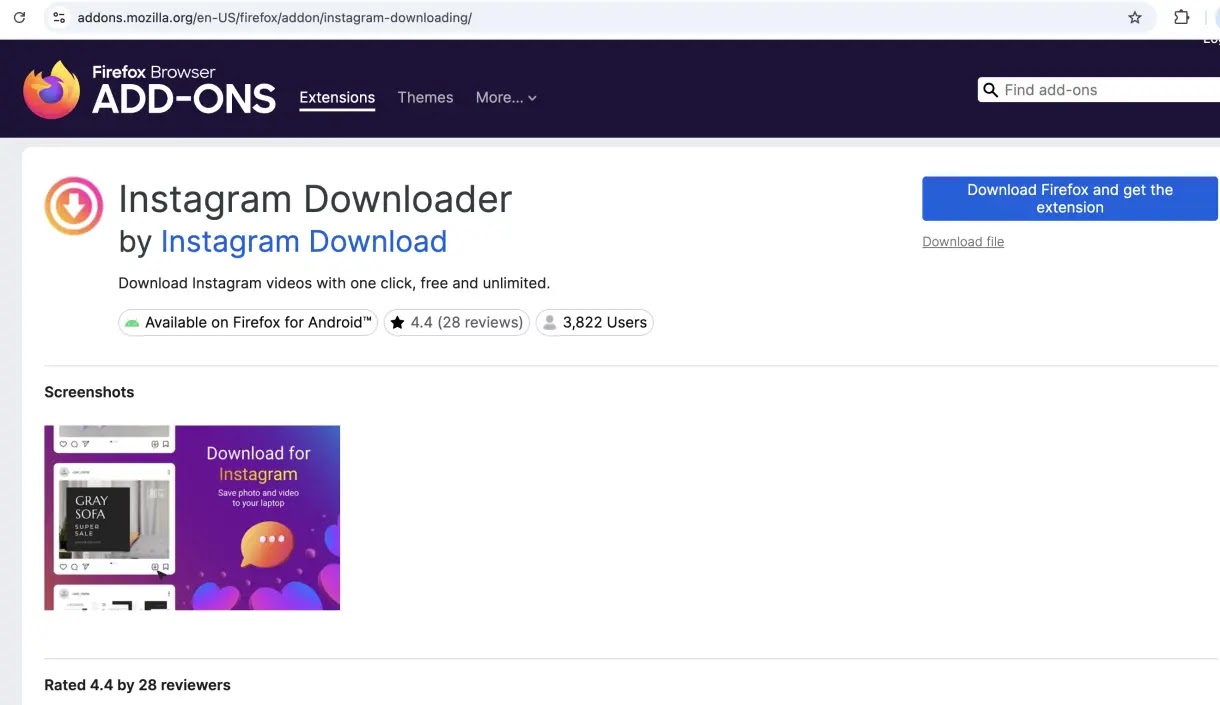
The GhostPoster campaign, which emerged as early as 2020, used deceptive extension names like “Google Translate in Right Click,” “Youtube Download,” and “Ads Block Ultimate” to appear legitimate while quietly stealing sensitive user information.
These extensions successfully bypassed security reviews from major browser stores, remaining active for up to five years before being discovered.
The sheer scale of installations demonstrates the effectiveness of this attack and the difficulty users face distinguishing trustworthy extensions from dangerous imposters.
The attack exploits a fundamental weakness in browser security: users trust extensions that appear in official stores.
The malicious extensions used steganography to hide malicious code inside PNG image files, a technique that conceals data in plain sight.
Once installed, the extensions extract the hidden payload and establish communication with attacker-controlled servers to download additional malicious scripts.
The malware then performs several harmful actions including hijacking affiliate links for financial gain, injecting scripts to track user behavior, manipulating HTTP headers to disable security protections, and stealing credentials and personal data.
The sophistication of these tactics shows this is not opportunistic malware but rather a well-planned operation targeting financial gain and sustained access to user devices.
LayerX Security analysts identified the full scope of the campaign after Koi Security initially discovered one malicious Firefox extension.
Their investigation uncovered the interconnected infrastructure linking all 17 extensions, revealing that these were not isolated incidents but part of a coordinated effort.
Techniques used
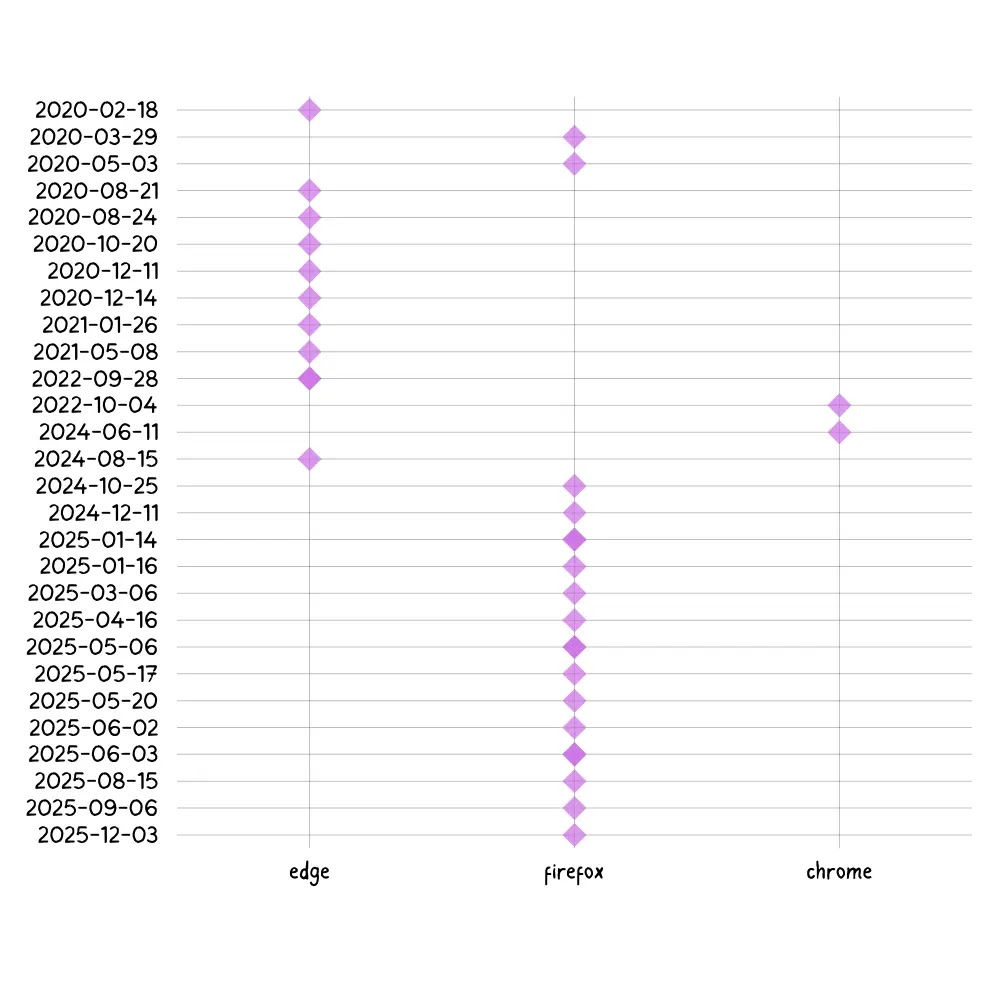
The research exposed how the threat actor systematically expanded from Microsoft Edge to Firefox and then to Chrome, adapting their techniques to fit each platform’s security requirements.
The malware’s sophisticated infection mechanism relies on delayed execution to evade detection.
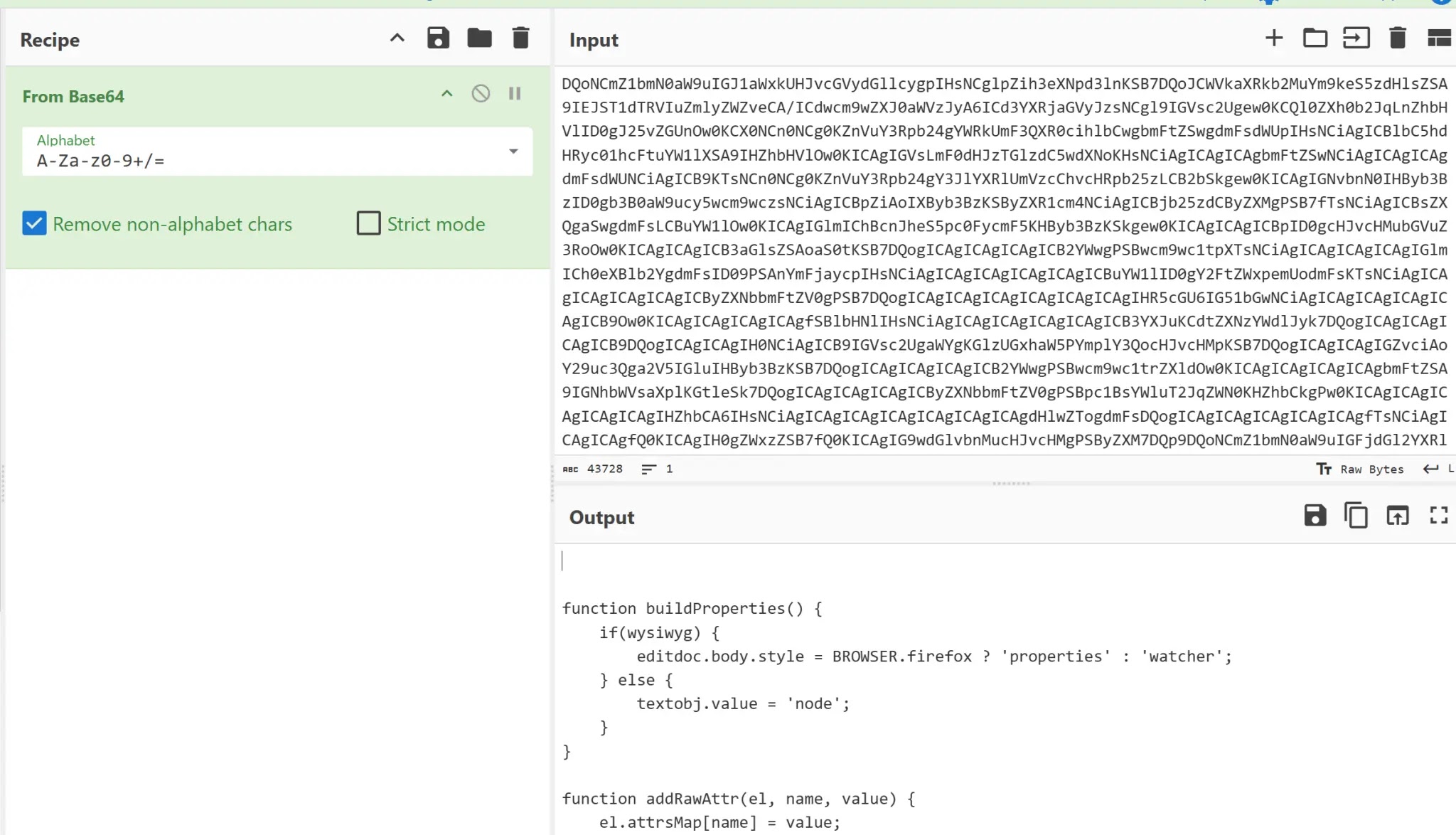
When installed, the extension waits 48 hours or longer before activating, allowing it to slip past security scanning during initial review.
More advanced variants wait up to five days before connecting to remote servers, creating a window where the malware operates while detection tools remain inactive.
The malicious code remains embedded inside the extension’s background script and uses encrypted payloads that are decoded only at runtime, making static analysis nearly impossible and ensuring the threat remains hidden until fully activated on victim machines.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.