AuraStealer Obfuscation, Anti- Researches Detailed
AuraStealer has emerged as a dangerous malware-as-a-service, actively targeting Windows systems from Windows 7 through Windows 11. This infostealer spreads primarily through Scam-Yourself campaigns...
AuraStealer has emerged as a dangerous malware-as-a-service, actively targeting Windows systems from Windows 7 through Windows 11.
This infostealer spreads primarily through Scam-Yourself campaigns on platforms like TikTok, where victims encounter tutorial videos promoting free activation of paid software.
The malware is developed in C++ with a build size between 500 to 700 KB and claims to steal data from more than 110 browsers, 70 applications including wallets and two-factor authentication tools, and over 250 browser extensions through its customizable configuration system.
The threat operates through multiple delivery methods including cracked games, malicious software downloads, and multi-stage execution flows involving custom loaders and DLL sideloading techniques.
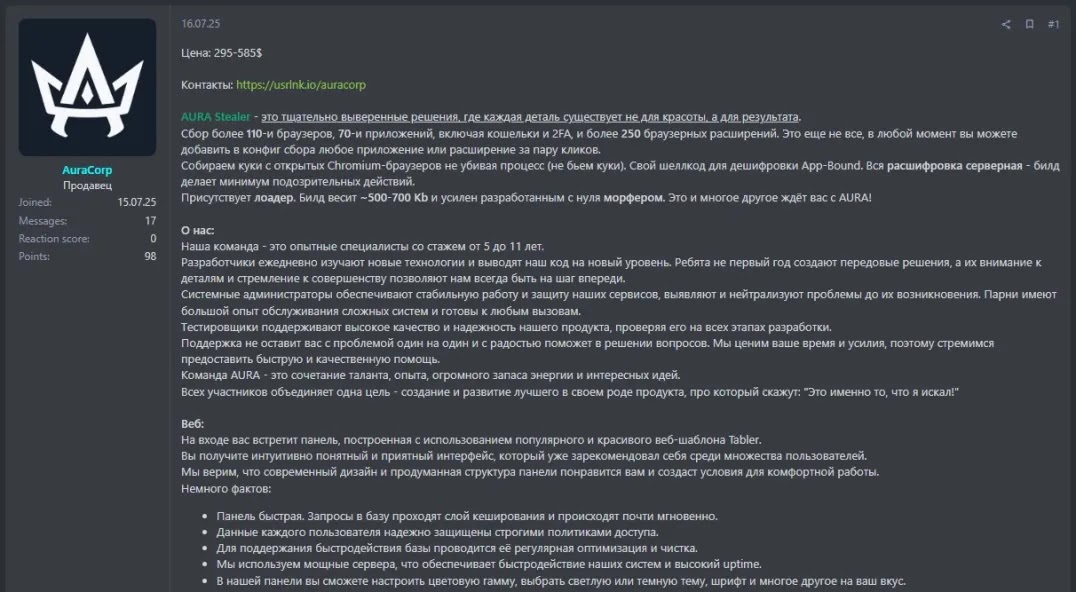
Offered through a tiered subscription model with prices ranging from $295 to $585 per month, AuraStealer provides cybercriminals with a dedicated web panel for managing stolen data.
The malware originally supported Russian only but has since been updated to include English language support, suggesting developers operate within Russian-speaking cybercriminal communities.
Despite its sophisticated design, the stealer contains several flaws that create detection opportunities for security defenders.
Gendigital researchers identified that AuraStealer uses advanced evasion tactics to avoid detection and analysis. The malware performs extensive checks before executing, including geolocation verification to avoid running in CIS countries and Baltic states.
It evaluates system characteristics like memory capacity and processor count to detect virtual machines, expecting at least four processors or 200 running processes to proceed with execution.
The stealer also displays a dialog box requiring users to enter a randomly generated code when running without protective layers, effectively halting automated sandbox analysis while forcing distributors to package the malware with additional protective layers.
Indirect Control Flow Obfuscation and String Encryption Techniques
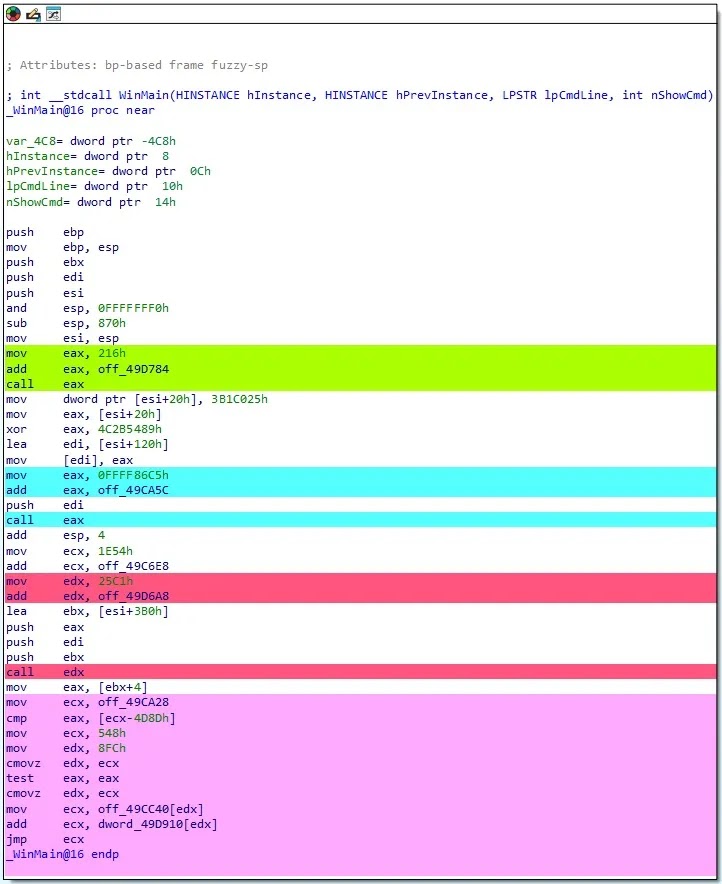
The malware implements indirect control flow obfuscation by systematically replacing direct jumps and calls with indirect ones where target addresses are computed only at runtime.
This method disrupts static analysis tools like IDA Pro by leaving disassemblers with seemingly unrelated basic blocks.
The obfuscation mechanism uses various patterns ranging from simple arithmetic sums to complex conditional instructions like cmovz where target addresses depend on return values of multiple preceding function calls.
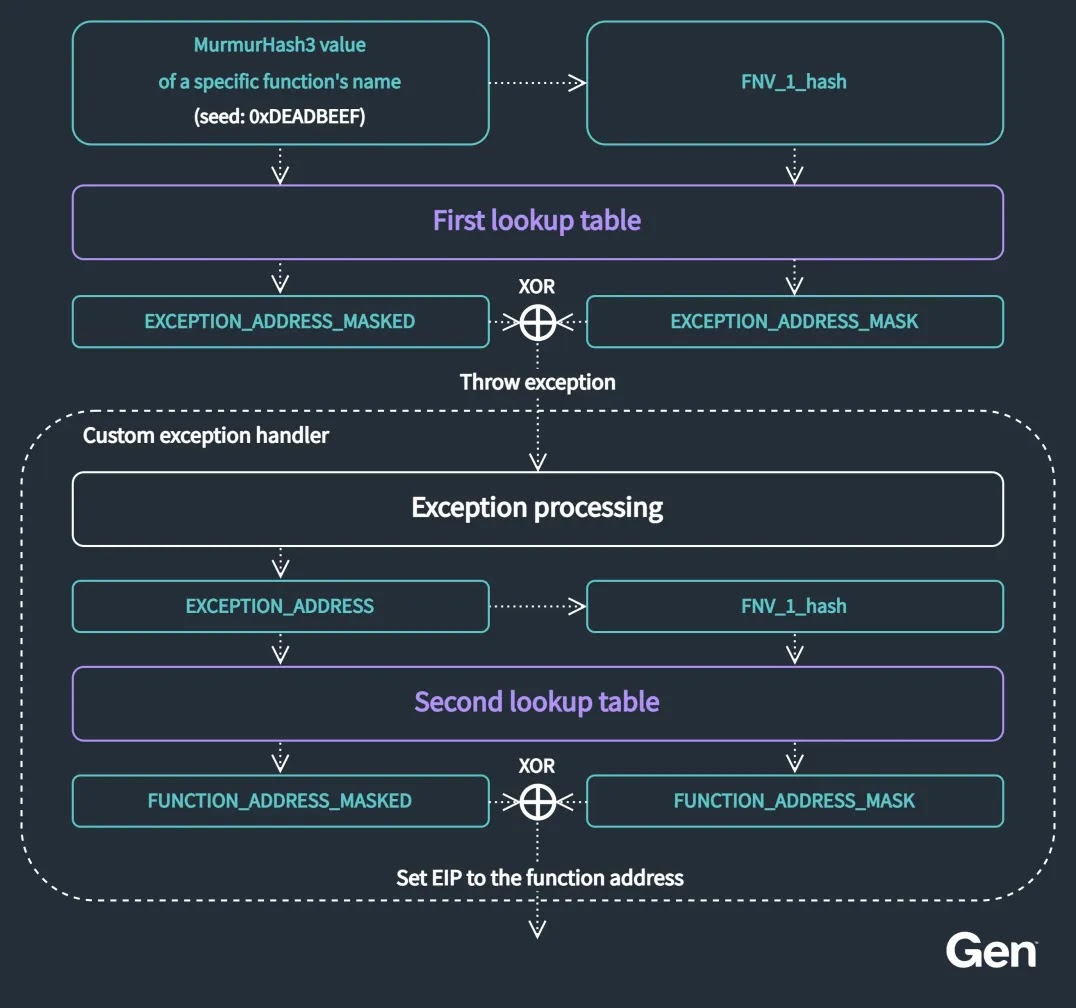
To hide its functionality, AuraStealer employs exception-driven API hashing through a custom exception handler that deliberately triggers access violations, intercepting them to dispatch appropriate function addresses from precomputed lookup tables.
String obfuscation uses stack-based XOR encryption where encrypted strings and corresponding XOR keys are concatenated in memory from constant values before being decrypted.
The malware performs anti-tampering checks using MapFileAndCheckSumw function to verify file checksums against values stored in the PE header, terminating execution if modifications are detected.
AuraStealer installs custom exception handlers during initialization routines before reaching WinMain, making detection easily overlooked.
The stealer targets sensitive data from Chromium and Gecko-based browsers, cryptocurrency wallets, active session tokens from Discord, Telegram and Steam, two-factor authentication tokens, password manager databases including KeePass and Bitwarden, VPN configurations, clipboard contents, and screenshots while allowing custom configuration modules for wildcard-based file searches.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.