Hackers Use Kernel Patch Protection to Hide Processes from
A newly identified technique, discovered in 2026, allows attackers to manipulate Windows kernel structures, effectively concealing running processes from detection systems. This occurs even as modern...
A newly identified technique, discovered in 2026, allows attackers to manipulate Windows kernel structures, effectively concealing running processes from detection systems. This occurs even as modern security layers like PatchGuard remain active and protect the system.
Outflank analysts identified a method that exploits the timing of system validation checks to hide malicious activity from plain sight.
The discovery highlights a critical gap in how Windows manages process visibility during termination.
While processes remain operational, they operate invisibly to monitoring tools like Task Manager and Process Hacker, making this approach ideal for maintaining persistence without immediate discovery.
The attack works by manipulating the internal data structures that Windows uses to track all active processes running on a system.
Outflank researchers noted that the malware’s emergence demonstrates how attackers continue to find creative ways around even sophisticated protection mechanisms.
Microsoft designed multiple layers of defense including PatchGuard, which performs integrity checks on kernel structures, and hypervisor-backed protections that prevent direct modification of code pages.
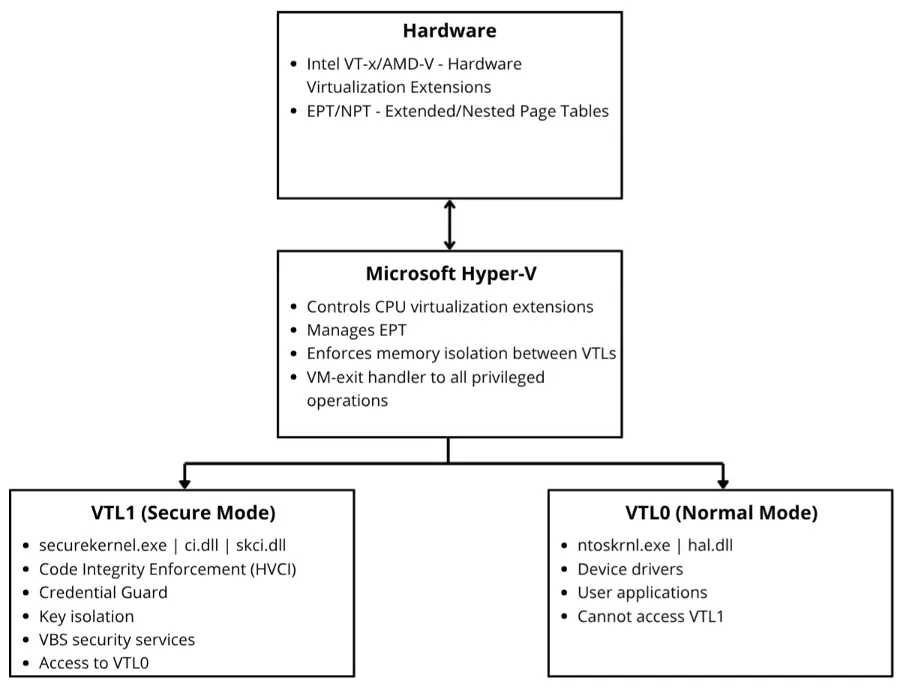
Despite these defenses, the newly documented approach navigates around these protections by operating on data rather than code.
The technique’s effectiveness depends on precise timing and deep knowledge of Windows internals. Attackers do not need to disable the security mechanisms directly.
Instead, they work within the constraints these protections impose, exploiting specific moments in the process termination sequence.
Process List Manipulation and the Termination Problem
Windows maintains all running processes in a doubly-linked list called ActiveProcessLinks, embedded within each process’s EPROCESS structure.
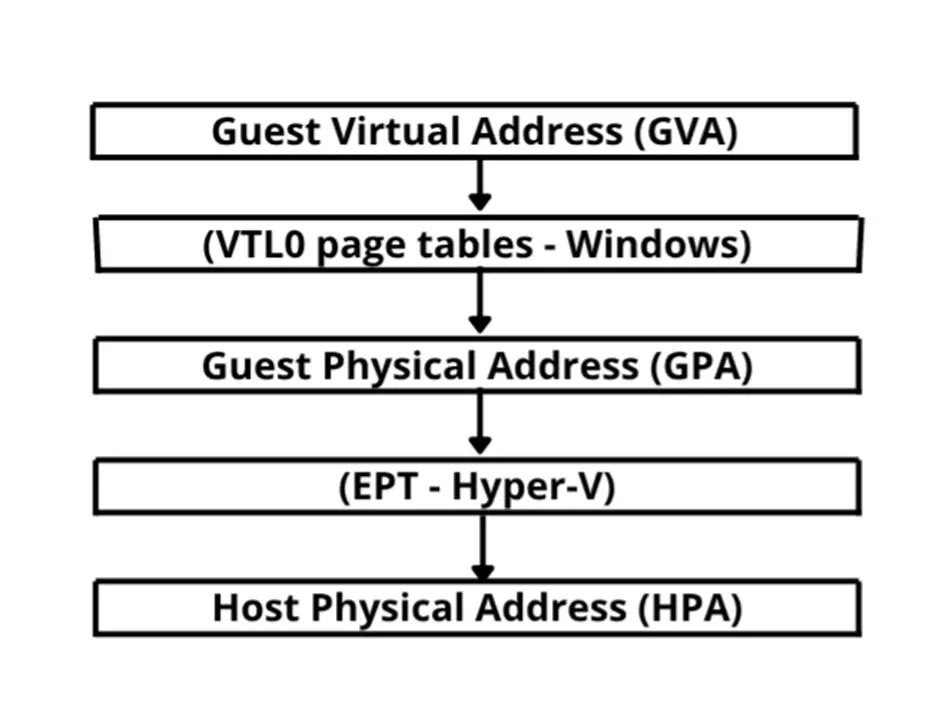
This structure contains forward and backward pointers that chain together every active process. To hide a process, attackers simply unlink it from this chain—Process One points directly to Process Three, skipping Process Two entirely.
The critical challenge emerges when the hidden process terminates. The Windows kernel function PspProcessDelete performs integrity validation on these LIST_ENTRY structures before cleanup.
This validation confirms bidirectional consistency: the forward link’s backward pointer must reference the original process entry, and the backward link’s forward pointer must do the same.
If corruption is detected during termination, the system triggers a 0x139 KERNEL_SECURITY_CHECK_FAILURE, causing an immediate blue screen.
The solution involves Microsoft’s documented PsSetCreateProcessNotifyRoutineEx callback function. This API allows drivers to receive notifications when processes create or terminate.
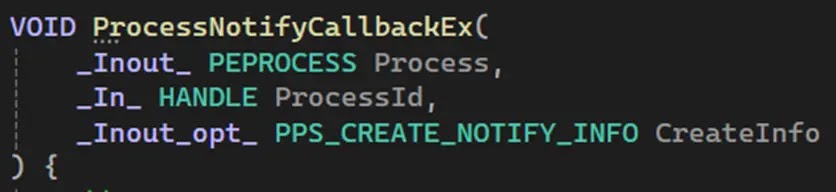
By registering such a callback, malicious drivers receive the EPROCESS structure at termination time, but before PspProcessDelete’s validation executes.
The driver then performs targeted repairs to the LIST_ENTRY structure, restoring consistency to the forward and backward pointers just microseconds before validation checks run.
Here lies the elegant bypass: the process was genuinely hidden throughout its execution lifetime, invisible to any scanning tool. Yet at the moment of termination, before PspProcessDelete examines the structures, the links are “unhidden” and repaired.
The integrity checks find nothing wrong. The process terminates cleanly. The malware execution remains hidden until the very end.
This approach works within HVCI’s hardware-enforced protections because the attack targets writable data structures, not protected code pages.
Extended Page Tables prevent modification of kernel code itself, but data remains accessible. The technique requires kernel-level execution privileges and a valid driver signature, which represents the primary practical barrier to exploitation.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.