Windows BitLocker 0-Day Allows Vulnerability Enables
Two newly discovered, unpatched Windows BitLocker zero-day vulnerabilities pose a significant threat to Microsoft’s ecosystem. These exploits include YellowKey, a critical BitLocker encryption...
Two newly discovered, unpatched Windows BitLocker zero-day vulnerabilities pose a significant threat to Microsoft’s ecosystem. These exploits include YellowKey, a critical BitLocker encryption bypass, and GreenPlasma, a privilege escalation flaw.
The most critical of these flaws, dubbed “YellowKey,” enables a total bypass of BitLocker encryption, granting attackers completely unrestricted access to locked system drives.
Following Microsoft’s recent Patch Tuesday, a frustrated researcher escalated an ongoing dispute by dropping two severe zero-day exploits.
The researcher expressed extreme dissatisfaction with Microsoft’s handling of previous disclosures, threatening further disruption and releasing the code as a direct retaliation. This unexpected release leaves millions of enterprise and government devices vulnerable.
He further claims these vulnerabilities are intentionally placed backdoors, actively crediting internal Microsoft threat groups like MSTIC and GHOST in a highly unusual public flex.
YellowKey BitLocker Bypass
YellowKey is a critical exploit that allows threat actors with physical access to entirely bypass BitLocker full-disk encryption in minutes. The vulnerability resides within the Windows Recovery Environment (WinRE) and exclusively impacts Windows 11, Windows Server 2022, and Windows Server 2025.
Windows 10 remains unaffected due to structural differences in its recovery architecture. Attackers only need to copy a specifically named FsTx folder onto a compatible USB stick and plug it into the target machine.
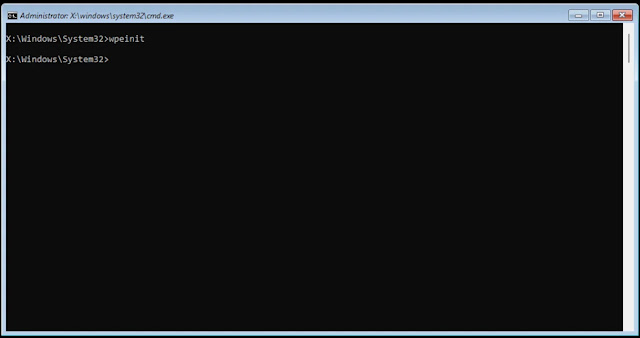
Alternatively, attackers can physically extract the target drive, copy the exploit files directly into the EFI partition, and remount the drive to achieve the exact same result.
By rebooting the system into the recovery agent using specific key combinations, the exploit leverages WinRE components to spawn a shell with unrestricted access to the protected volume.
GreenPlasma Privilege Escalation
Alongside the encryption bypass, the hacker released partial proof-of-concept code for GreenPlasma, a severe local privilege escalation vulnerability. This specific flaw exploits the Windows CTFMON service through arbitrary memory section creation.
An unprivileged attacker can create these memory-section objects within directory structures that are normally writable only by the administrative SYSTEM account. Consequently, malicious actors can manipulate trusted Windows services and kernel-mode drivers into executing unauthorized commands.
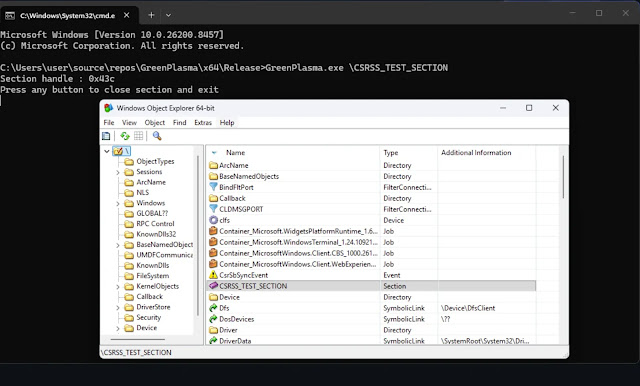
While the current public code triggers a User Account Control prompt and requires additional weaponization to achieve a completely silent attack, it poses a substantial challenge for security defenders.
If fully chained with initial access vectors, this could allow persistent, full access to the core of the operating system.
| Threat Component | Vulnerability Type | Affected Systems | Key Artifacts |
|---|---|---|---|
| YellowKey | Encryption Bypass | Windows 11, Server 2022/2025 | System Volume InformationFsTx directory |
| YellowKey | WinRE Exploit | Windows 11, Server 2022/2025 | bootmgfw.efi manipulation |
| GreenPlasma | Privilege Escalation | Windows 11, Server 2022/2025 | CTFMON Arbitrary Section Creation |
| GreenPlasma | Memory Manipulation | Windows 11, Server 2022/2025 | SYSTEM-writable directory objects |
Microsoft has not yet issued an official patch for these freshly dropped zero-day exploits. Independent security researchers analyzing the YellowKey threat strongly recommend implementing a custom BitLocker PIN and a robust BIOS password as immediate defensive mitigations.
While Nightmare-Eclipse claims the core vulnerability bypasses TPM and PIN configurations, the public proof-of-concept currently lacks that execution capability.
Security teams should actively monitor physical access to hardware endpoints and restrict unauthorized WinRE modifications until Microsoft officially resolves the situation.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.







No Comment! Be the first one.