r1z Initial Access Broker’s Major OPSEC Researchers Detailed
U.S. authorities have exposed “r1z,” an initial access broker who sold illicit access to corporate networks globally. Operating across popular cybercrime forums, he offered stolen VPN...
U.S. authorities have exposed “r1z,” an initial access broker who sold illicit access to corporate networks globally.
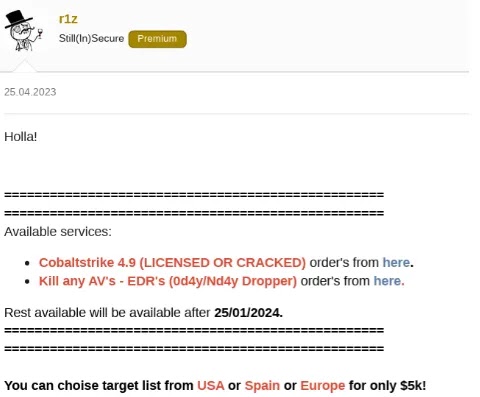
Operating across popular cybercrime forums, he offered stolen VPN credentials, remote access to enterprise environments, and custom tools designed to bypass security controls.
His activity fed the ransomware supply chain by giving other criminals ready-made entry points into victim organizations.
The case shows how a single broker can turn technical skill into a scalable business model. By exploiting firewall and VPN weaknesses and reselling that access, r1z helped lower the bar for launching major intrusions.
Investigators say his offerings included access to companies in the U.S., Europe, Mexico, and other regions, often with remote code execution rights that gave buyers near full control over targeted systems.
This made his listings especially attractive to ransomware crews looking for fast, reliable footholds.
Kela analysts identified r1z as a prolific actor, tying him to around 1,600 posts across XSS, Nulled, Altenen, RaidForums, BlackHatWorld, and other underground communities.
In these spaces, he advertised network access, a powerful EDR-killer tool, and cracked versions of Cobalt Strike, which buyers could use to move laterally and maintain control inside compromised networks.
Kela researchers noted that behind the scenes, law enforcement had already infiltrated his operations.
An undercover FBI agent approached him as a customer, purchasing access and advanced malware that could disable multiple endpoint detection and response products.
That cooperation allowed investigators to observe his tradecraft in real time, map his infrastructure, and connect his offerings to at least one significant ransomware attack.
It also paved the way for linking the “r1z” handle to Jordanian national Feras Albashiti, who later pleaded guilty to selling access to dozens of companies.
OPSEC Failures and OSINT Trail
The turning point in the r1z investigation came not from a single mistake but from years of weak operational security.
Kela analysts noted that he repeatedly reused the same usernames, email addresses, TOX ID, and profile images across forums, Telegram, personal websites, and even professional platforms.
This pattern created a rich OSINT trail that analysts could steadily correlate. A single Gmail account, “gits.systems@gmail[.]com,” surfaced in leaked databases, domain registrations, and social media profiles, all pointing back to Albashiti.
These overlaps turned his attempts at anonymity into a liability. Investigators traced his domain sec-r1z.com, historical WHOIS records, and linked “OrientalSecurity” branding, which revealed phone numbers, locations in Jordan and Georgia, and a LinkedIn presence under variations of his real name.
Each reused detail strengthened attribution, showing how even seasoned threat actors can undermine themselves when OPSEC discipline slips.
For defenders, the r1z case underlines the value of continuous underground monitoring and long-term correlation of identity signals to expose and disrupt access brokers before their offerings translate into the next wave of breaches.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.