ClickFix Campaign Hijacks Facebook Sessions via Fake Pages
Dubbed ClickFix, a widespread campaign has emerged, designed to steal Facebook account credentials by tricking users into surrendering their session tokens. Rather than using complex malware or...
Dubbed ClickFix, a widespread campaign has emerged, designed to steal Facebook account credentials by tricking users into surrendering their session tokens.
Rather than using complex malware or software exploits, the attack relies on social engineering to guide victims through a fake verification process.
This campaign has grown significantly since early 2025 and continues to target content creators and business page owners who seek Facebook verification badges.
The ClickFix attack works by combining trust and urgency. Victims receive messages about free verified badges or urgent account reviews. When they click the link, they land on a page that looks exactly like Facebook’s official help center or verification portal.
The page explains that the user has been selected for verification or that their account has been flagged for policy violations. This creates pressure to act quickly.
Once on the fake page, victims are guided through a multi-stage process that appears legitimate but is designed to extract their authentication tokens.
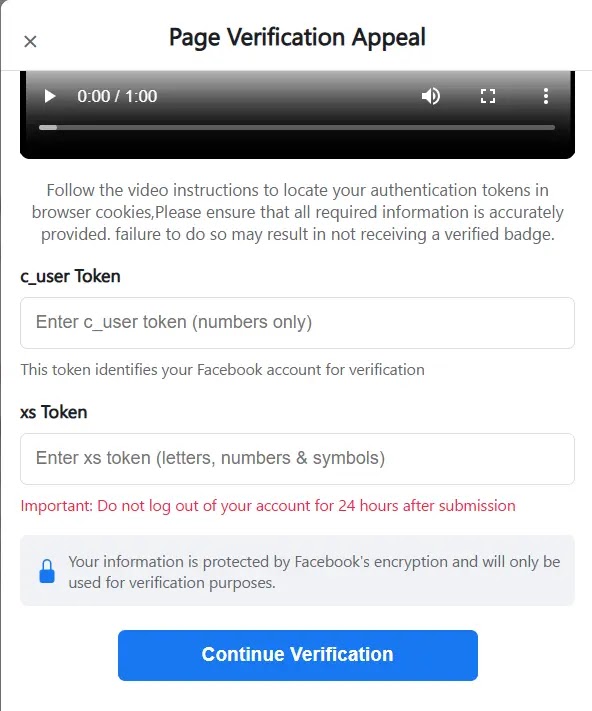
The attackers show instructional videos that teach users how to access their browser’s developer tools and copy their Facebook session tokens, specifically the values labeled c_user and xs. Users are told this is a normal verification step and necessary to confirm their identity.
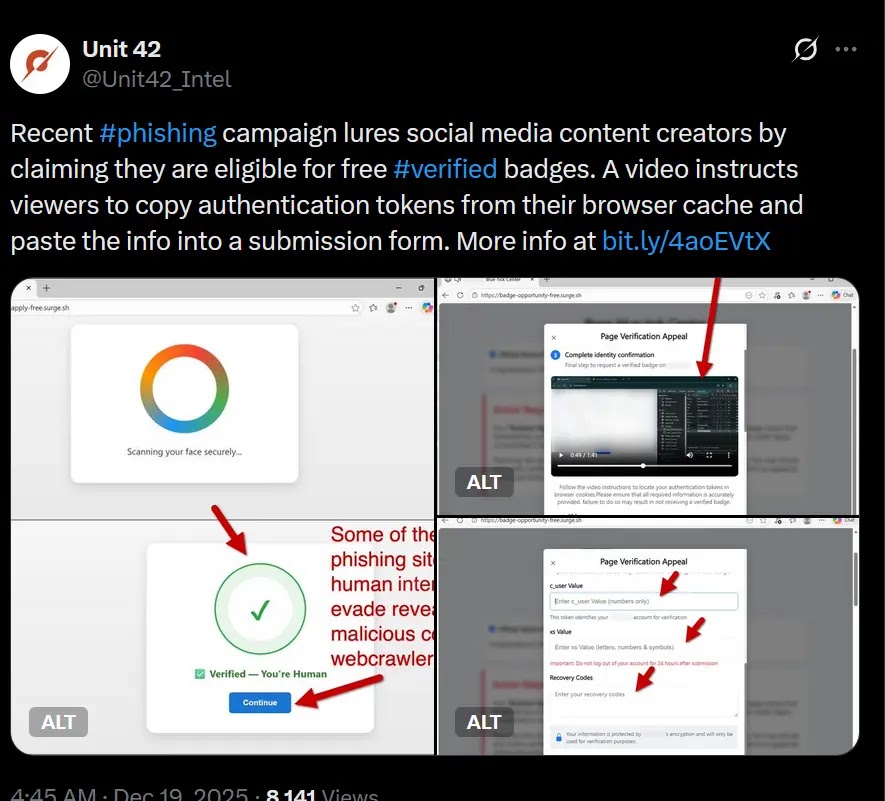
Hunt.io analysts and researchers identified this campaign after Unit42 Threat Intelligence first reported it in December 2025. The investigation revealed that attackers have created at least 115 distinct phishing pages and eight data collection endpoints.
The campaign has been active since January 2025 and primarily targets content creators, monetized pages, and businesses seeking verification status.
A single stolen session token gives attackers complete account control, enabling them to change passwords, steal payment information, and impersonate the victim.
The infrastructure behind this campaign is deliberately scattered across multiple hosting platforms to avoid detection.
Phishing pages are hosted on Netlify, Vercel, Wasmer, GitHub Pages, Surge, and other abuse-friendly services. When a page gets taken down, the attacker simply deploys a new one within minutes.
The stolen session tokens are sent to separate data collection endpoints backed by services like Formspark and submit-form.com, which are decoupled from the phishing pages themselves.
How the Attack Flow Works
The infection mechanism starts with a redirect chain designed to feel seamless. Users might click a link from social media promising a free blue badge or claiming their page has been flagged.
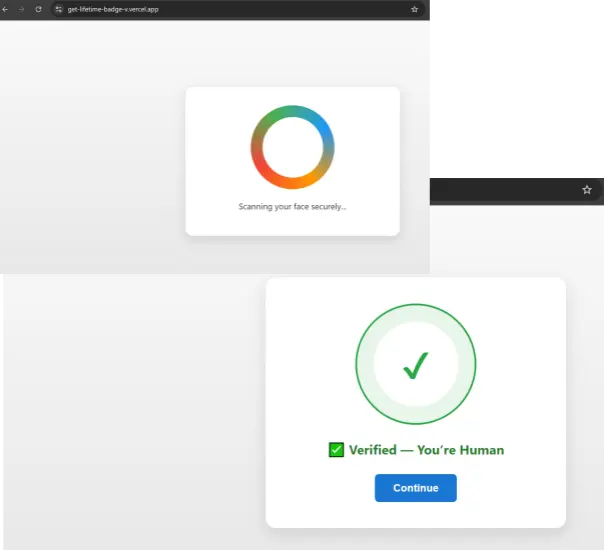
This initial page displays an animated verification screen with sound effects and timed animations to build credibility.
Once the animation completes, the victim is automatically redirected to a second page that fully impersonates Facebook’s branding, including logos, colors, and official-looking language.
At this stage, prominent red warnings and urgent messaging push the user to continue.
The page displays something like “Action Required” buttons and countdown timers to trigger immediate responses.
The victim is presented with an embedded instructional video that explicitly walks through the manual extraction process. The video shows how to open browser developer tools, navigate to the Storage or Application tab, and copy the exact session cookie values.
This is the critical step where victims voluntarily hand over their authentication tokens.
Once the user enters their c_user and xs values into a form field, the JavaScript code validates the tokens in real time to ensure they match legitimate Facebook session patterns.
This filtering reduces noise on the attacker’s backend and ensures only valid, reusable sessions are captured.
The script includes instructions telling victims not to log out for 24 hours, which keeps the harvested cookies valid long enough for immediate account takeover.
If the initial token theft succeeds, the attacker gains instant access to the account and can begin making changes.
However, if the stolen session fails to work later, the attack has fallback options. The fake verification page introduces additional harvesting stages where victims are asked to provide backup or recovery codes.
After these codes are collected, a pop-up appears claiming that additional password verification is needed.
This final request tricks users into surrendering their actual Facebook password, completing a full credential harvesting chain that gives attackers multiple ways to regain access even if the session token becomes invalid.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.