Critical Vivotek Flaw Allows Remote Code Injection Expl
A critical remote code injection vulnerability has been identified within Vivotek legacy firmware. This severe flaw enables unauthenticated attackers to execute arbitrary commands with root...
A critical remote code injection vulnerability has been identified within Vivotek legacy firmware. This severe flaw enables unauthenticated attackers to execute arbitrary commands with root privileges, posing a significant threat to affected systems.
The vulnerability, tracked as CVE-2026-22755, affects dozens of camera models and poses significant risks to organizations relying on legacy surveillance infrastructure.
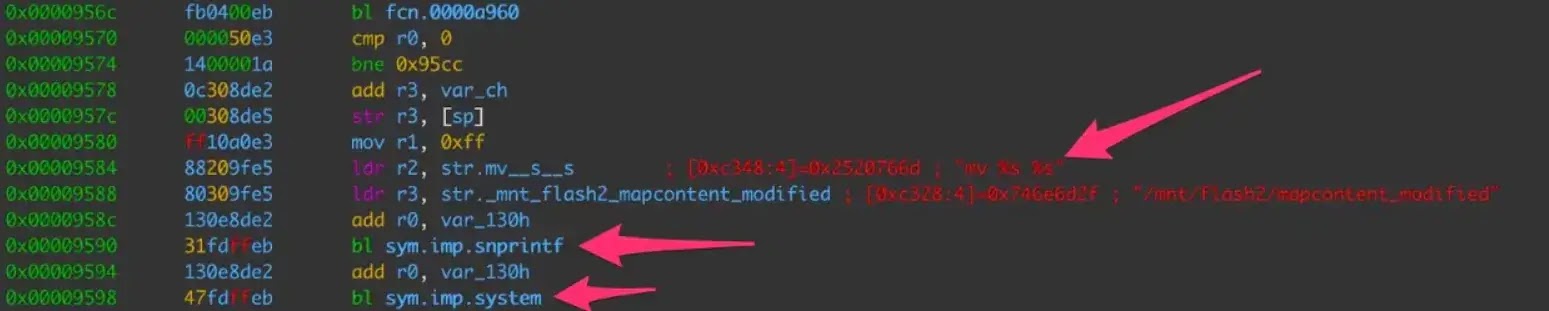
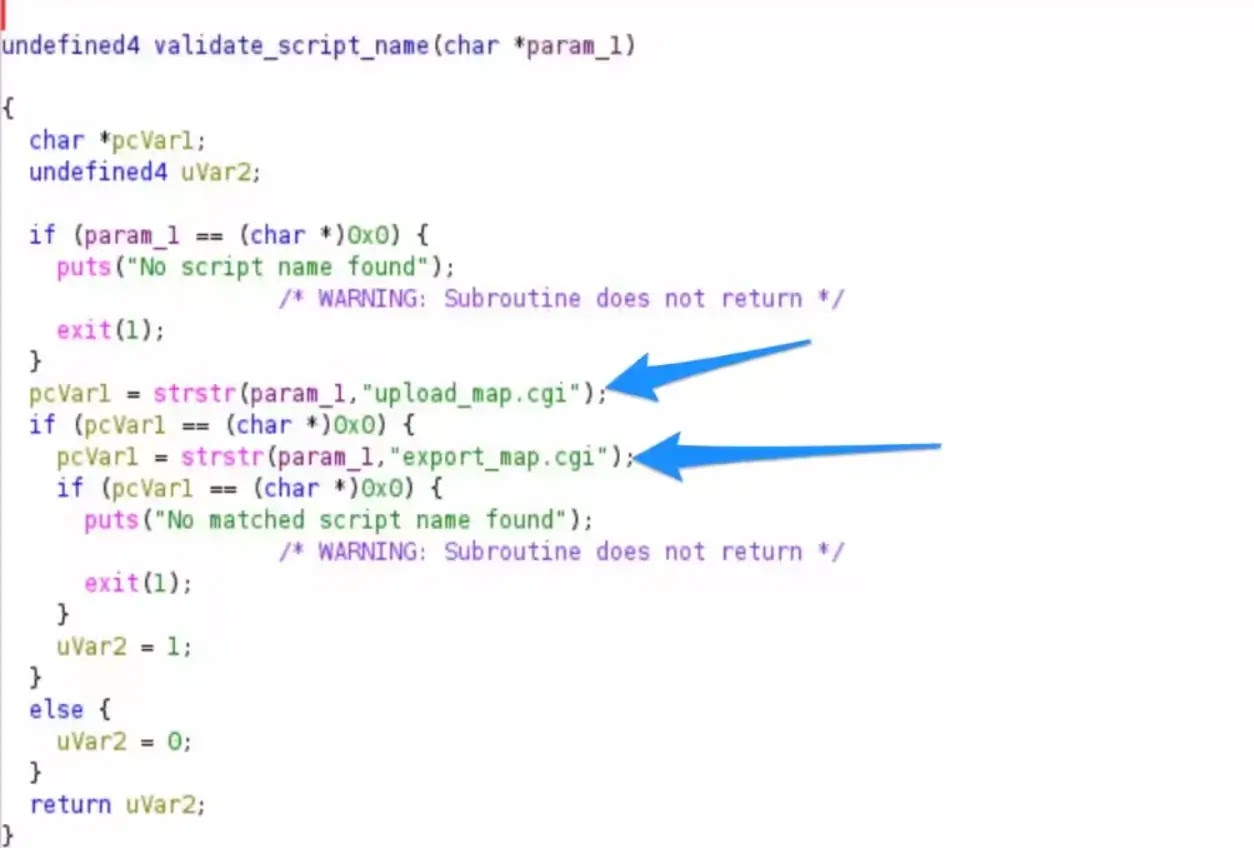
The vulnerability exists in the upload_map.cgi script, where user-supplied filenames are processed through an unsanitized snprintf() function before being passed to the system() call.
This allows attackers to inject shell commands via specially crafted filenames that contain metacharacters, such as semicolons.
Vivotek Vulnerability
Akamai researchers discovered that Vivotek legacy cameras lack password protection by default, eliminating authentication barriers.
The exploit requires five specific conditions: file size under 5MB, firmware verification bypass, and an intact /usr/sbin/confclient binary.
Non-standard web server environment variables, and access through upload_map.cgi rather than file_manager.cgi.
Researchers created a bash script that generates valid firmware images with proper magic bytes (FF V FF FF header and FF K FF FF footer) to bypass validation checks.
By setting environment variables, including POST_FILE_NAME=”test_firmware.bin; id;”, attackers trigger command execution as the root user, as evidenced by proof-of-concept demonstrations in which the id command showed a uid of 0 (root).
The vulnerability impacts 36 camera models across multiple product lines.
| Model Series | Affected Firmware |
|---|---|
| FD8365, FD9165, FD9371 | 0100a–0125c |
| FE9180, FE9191 | 0100a–0125c |
| IB9365, IP9165, IP9171 | 0100a–0125c |
| MA9321, MS9390, TB9330 | 0100a–0125c |
Attack Scenario
An attacker can remotely upload a malicious firmware file with an embedded command in the filename.
When processed by the vulnerable upload_map.In a CGI script, the shell metacharacter triggers command execution.
The resulting payload executes with root privileges, enabling complete system compromise, lateral network movement, botnet installation, or data exfiltration.
According to Akamai, organizations should implement network-level detection using the following YARA rule to identify exploitation attempts:
rule CVE_2026_22755_Vivotek_upload
{
meta:
description = "Detects upload_map.cgi requests with camid parameter"
strings:
$path = "/cgi-bin/admin/upload_map.cgi"
$param = "camid="
condition:
all of them
}Prioritize firmware updates for affected camera models immediately. Implement network segmentation to isolate legacy camera infrastructure.
Deploy intrusion detection signatures for malicious upload_map.cgi requests. Conduct inventory audits to identify deployed vulnerable devices.
Monitor for suspicious file uploads and POST requests to camera administration interfaces.
This vulnerability represents a critical IoT security risk, particularly for organizations operating legacy surveillance systems in critical infrastructure, healthcare, and enterprise environments.
Unauthenticated remote code execution with root privileges enables complete device compromise and potential network propagation through botnet-based distributed denial-of-service attacks.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.








No Comment! Be the first one.