Hackers Earned $516,500 for 37 Unique 0-day Vulnerabilities –
On its first day, Pwn2Own Automotive 2026 awarded $516,500 USD for the disclosure of 37 zero-day vulnerabilities. This brings the event’s cumulative total to $955,750 USD across 66 unique...
On its first day, Pwn2Own Automotive 2026 awarded $516,500 USD for the disclosure of 37 zero-day vulnerabilities. This brings the event’s cumulative total to $955,750 USD across 66 unique vulnerabilities, underscoring the automotive sector’s substantial attack surface.
The competition showcased exploits targeting multiple vehicle subsystems, including in-vehicle infotainment (IVI) systems, EV charging stations, and embedded Linux environments.
Researchers successfully demonstrated command injection flaws, buffer overflows, authentication bypasses, and privilege escalation vulnerabilities across devices manufactured by Alpine, Kenwood, Phoenix Contact, Alpitronic, and Autel.
Fuzzware.io emerged as a commanding leader in the Master of Pwn standings, demonstrating technical sophistication through complex vulnerability chains.
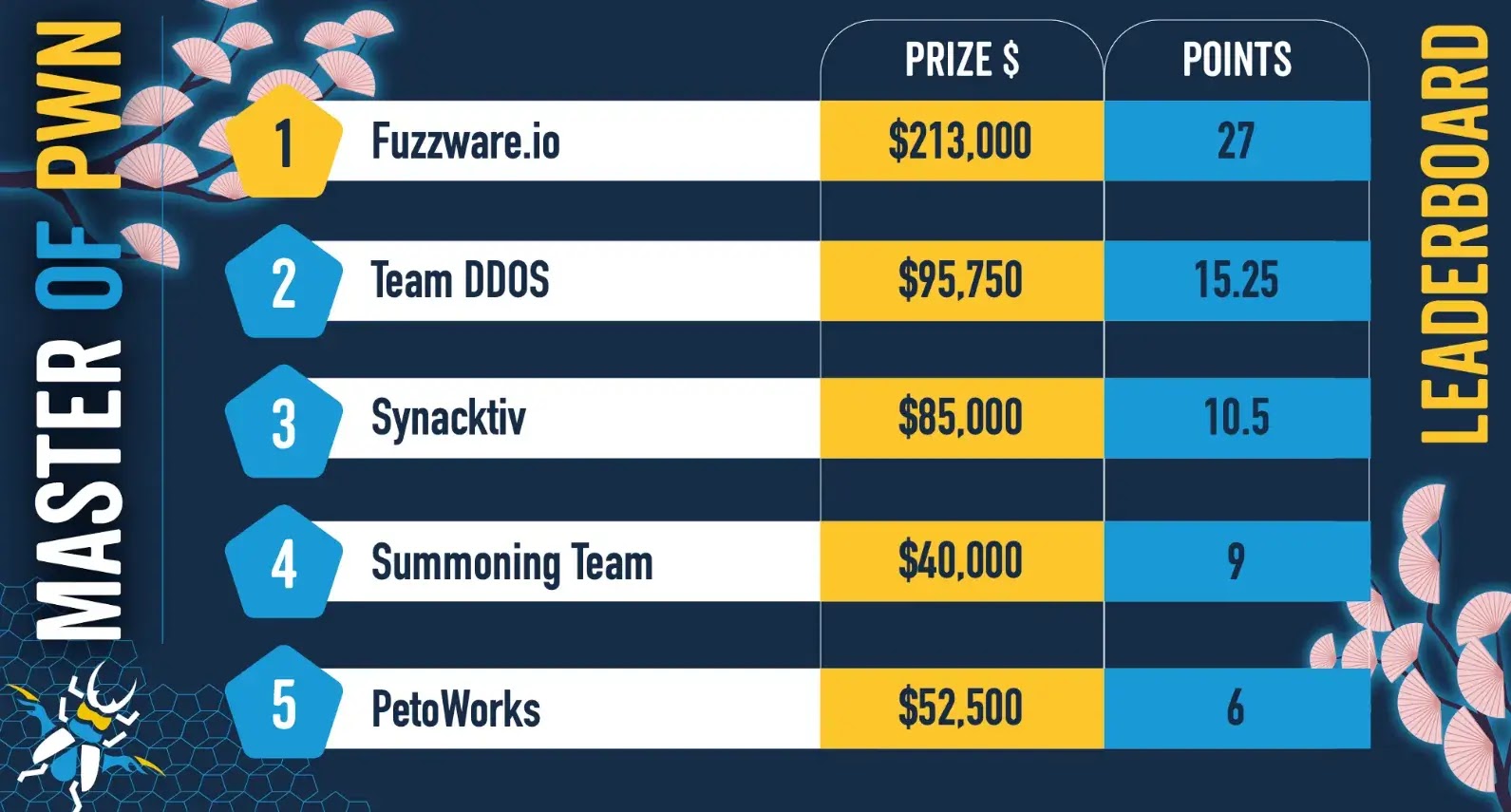
Combining command injection vulnerabilities with protocol manipulation add-ons to maximize points.
The team exploited multiple bugs in the Phoenix Contact CHARX SEC-3150 and ChargePoint Home Flex (CPH50-K) systems.
Their strategy of chaining multiple vulnerabilities reflects advanced exploitation techniques required in modern automotive security research.
Among Day Two’s standout achievements, Rob Blakely of Technical Debt Collectors successfully chained three bugs: an out-of-bounds read, memory exhaustion, and a heap overflow against Automotive Grade Linux, earning $40,000 USD.
This exploit chain demonstrated the criticality of defending open-source automotive platforms used across the industry.
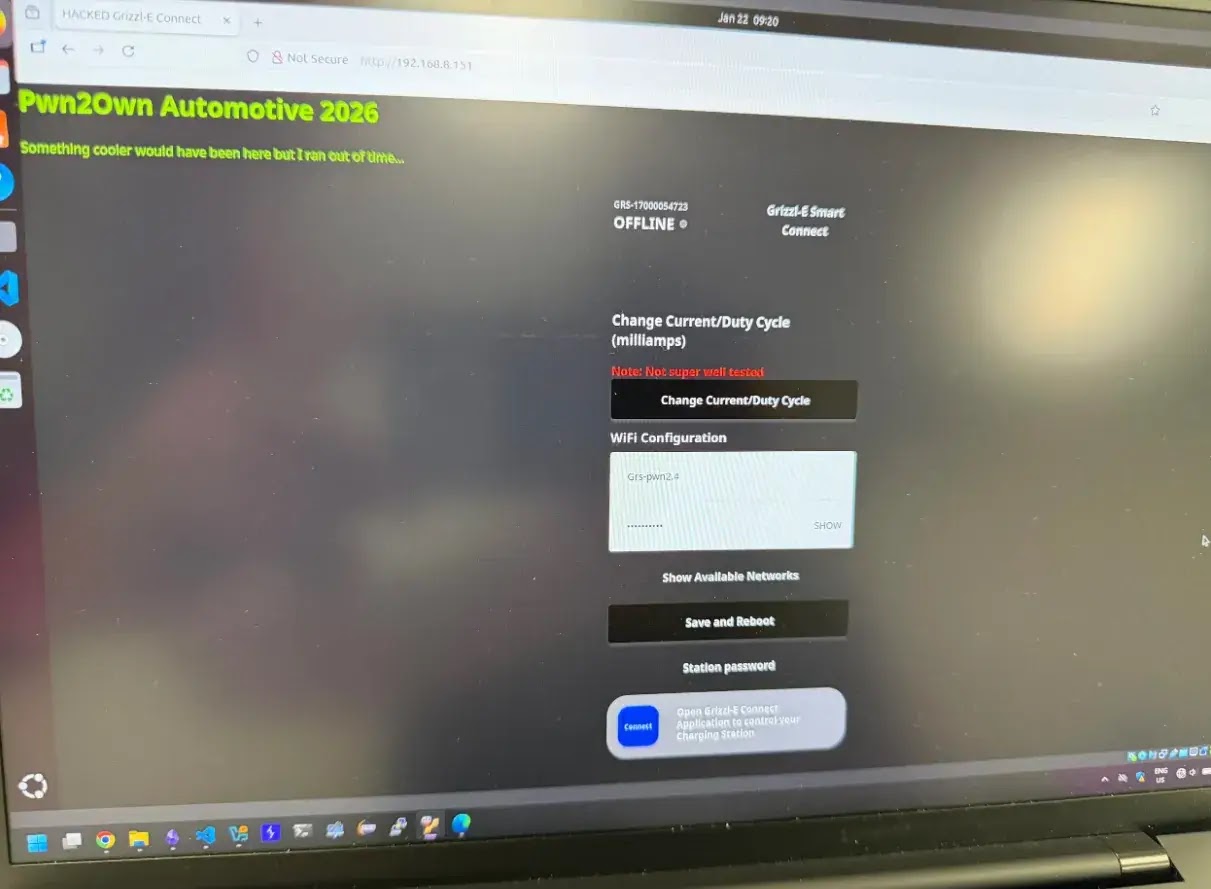
EV Charging Infrastructure Vulnerabilities Exposed
Charging infrastructure emerged as a prominent vulnerability vector, with multiple teams successfully bypassing security on EV charging stations.
Synacktiv exploited a stack-based buffer overflow in the Autel MaxiCharger AC Elite Home 40A. At the same time, the Summoning Team demonstrated command-injection flaws in ChargePoint Home Flex systems.

These attacks underscore the security implications of rapidly expanding EV charging networks.
The event also documented collision exploits in which multiple teams independently discovered the same vulnerabilities.
Fifteen collision submissions occurred across Day Two, reducing overall prize payouts but validating that specific security flaws are discoverable through multiple research approaches.
Fuzzware.io’s commanding lead suggests the final day may determine the Master of Pwn title, with technical execution and vulnerability discovery speed becoming decisive factors.
According to zerodayinitiative, the cumulative vulnerability count of 66 zero-days across two days highlights the breadth of automotive attack surfaces, from infotainment and charging protocols to embedded operating systems.
Day Three will likely bring additional discoveries as the competition concludes.
The vulnerabilities disclosed at Pwn2Own inform vendor security roadmaps and contribute to industry-wide hardening efforts across connected vehicle platforms.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.