Attackers Backdoor CODESYS Apps via Chained Applications Chaining
Researchers have uncovered multiple vulnerabilities within the CODESYS Control runtime, one of the world’s most widely adopted software-based programmable logic controller (Soft PLC) platforms....
Researchers have uncovered multiple vulnerabilities within the CODESYS Control runtime, one of the world’s most widely adopted software-based programmable logic controller (Soft PLC) platforms.
According to Nozomi Networks Labs researchers, by chaining these security flaws, an authenticated attacker can replace a legitimate industrial control application with a backdoored version, thereby escalating their privileges to full administrative control of the targeted device.
CODESYS is utilized across diverse industrial sectors, from water treatment facilities and energy grids to automated manufacturing lines.
Because these PLCs directly govern physical processes, an exploited vulnerability can result in halted production, equipment damage, or hazardous operating conditions.
The CODESYS Control runtime manages real-time input/output processing and network communications for automated systems.

The newly discovered vulnerabilities impact how the runtime handles file permissions and backup restorations.
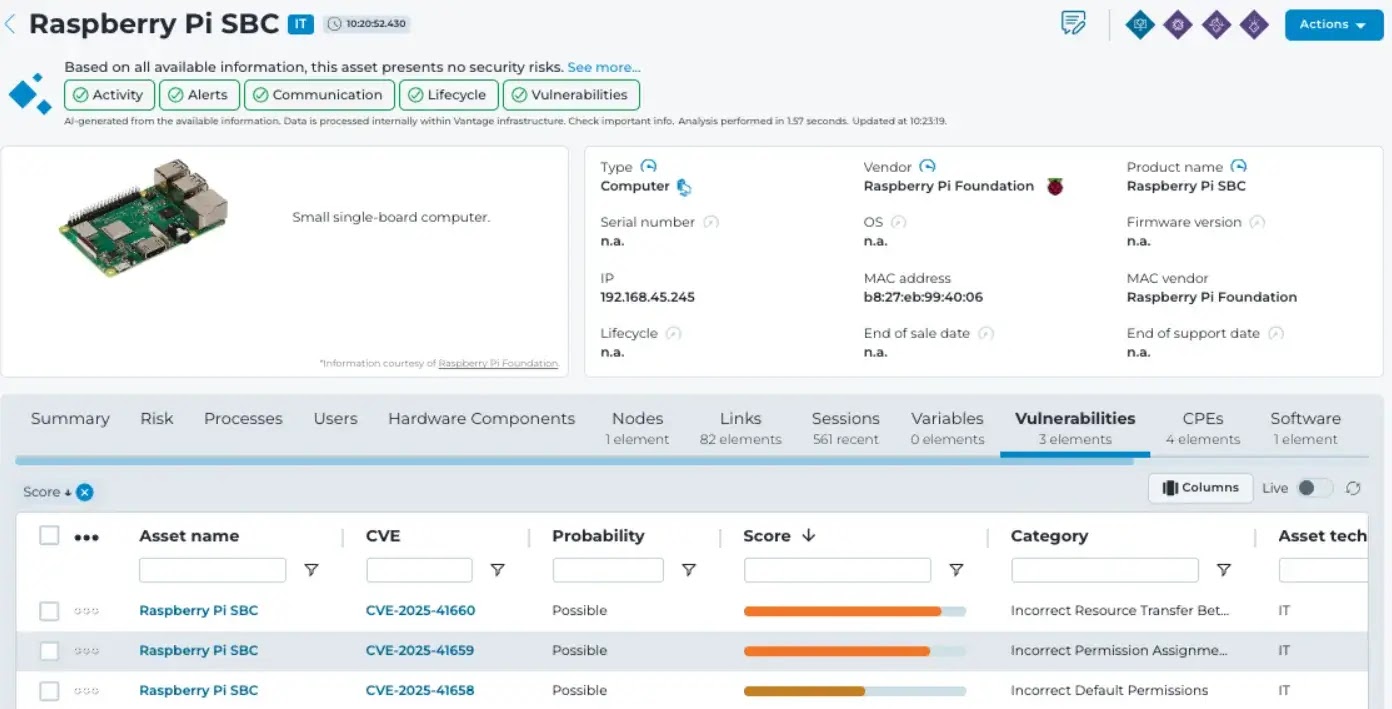
CVE-2025-41658 (5.5, Medium): Incorrect default permissions allow local users to read CODESYS password hashes.
CVE-2025-41659 (8.3, High): Improper permissions allow low-privilege users to access sensitive cryptographic data.
CVE-2025-41660 (8.8, High): Flawed resource transfer allows restoration of a tampered boot application.
The Attack Chain Workflow
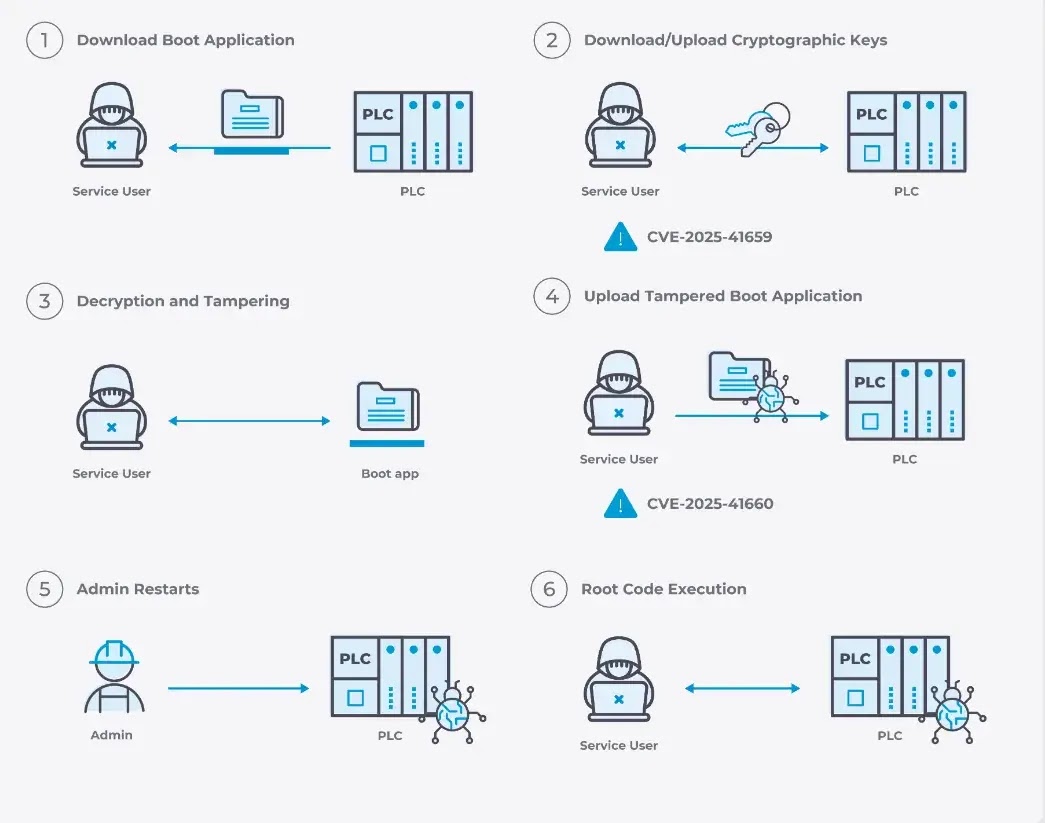
To execute this attack, a threat actor first needs valid Service-level credentials.
Standard security controls usually prevent this, but attackers can steal credentials via default passwords, a compromised engineering workstation, or by exploiting CVE-2025-41658 to extract hashes.
Once authenticated, the attack unfolds in several stages:
- Download the Application: The attacker uses the platform’s backup functionality to download the active boot application from the PLC.
- Steal Cryptographic Keys: By exploiting CVE-2025-41659, the attacker extracts the necessary cryptographic material to bypass optional code encryption and signing protections.
- Tamper and Restore: The attacker injects malicious machine code into the binary, re-signs it if necessary, and exploits CVE-2025-41660 to upload the backdoored application back to the device.
- Achieve Root Execution: The attacker waits for an operator to restart the application or reboot the system. Upon restart, the injected backdoor runs with root privileges.
- Escalate Privileges: With root access, the attacker modifies the local user database to grant themselves full Administrator rights.
A compromised Soft PLC allows adversaries to alter actuator behavior, change safety setpoints, and override critical system interlocks.
This attack aligns with several MITRE ATT&CK for ICS techniques, including Manipulation of Control (T0831), Module Firmware modification (T0839), and Theft of Operational Information (T0882).
CODESYS Group has fully resolved these issues in CODESYS Control Runtime version 4.21.0.0 and Toolkit version 3.5.22.0.
According to Nozomi Networks, to prevent further tampering, CODESYS has made code signing mandatory by default for all PLC code before it can be deployed or executed.
Administrators should apply these updates immediately, enforce strict network segmentation, and continuously monitor industrial network traffic for suspicious activity.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.