Vidar Malware Hides Second-Stage Payloads in JPEG and TXT Files to
Vidar, one of the most active information-stealing malware families, has adopted a concerning new evasion tactic in 2026. A recent analysis reveals Since its first appearance in 2018, Vidar started...
Vidar, one of the most active information-stealing malware families, has adopted a concerning new evasion tactic in 2026. A recent analysis reveals
Since its first appearance in 2018, Vidar started as a basic credential stealer built on the Arkei framework.
Over the years, it grew into something far more dangerous. By 2026, it has embraced a Malware-as-a-Service (MaaS) model, supports multi-stage delivery chains, and uses social media platforms like Telegram for command-and-control operations.
The malware no longer just steals passwords. It now executes entire infection chains inside a computer’s memory, leaving very little trace behind on the infected system.
Analysts from the Lat61 Threat Intelligence Team at Point Wild identified this new variant and published their findings on April 24, 2026. Researchers Kedar Shashikant Pandit and Prathamesh Shingare examined the full infection lifecycle, from the very first entry point all the way to the final data exfiltration phase.
Their analysis revealed that this specific Vidar variant depends heavily on obfuscated scripts, trusted Windows tools, and staged delivery through non-executable file formats to stay hidden from security tools.
The malware spreads through multiple entry points. Fake GitHub repositories disguised as developer tools or leaked software have been used to distribute Vidar. Compromised WordPress websites and fake CAPTCHA pages, known as ClickFix pages, trick users into running Windows commands that trigger the infection chain.
Gaming communities have also been targeted through fake cheat tool repositories shared on platforms like GitHub, Discord, and Reddit, where users are more likely to ignore security warnings in exchange for in-game advantages.
The campaign carries a wide impact. Vidar targets over 200 browser extensions, including crypto wallets like MetaMask, Phantom, and Coinbase Wallet, along with password managers such as Bitwarden, LastPass, and KeePass.
This goes well beyond simple credential theft and puts both individuals and organizations at serious risk of financial loss and large-scale data exposure.
Infection Mechanism: How Vidar Executes Through Staged File Delivery
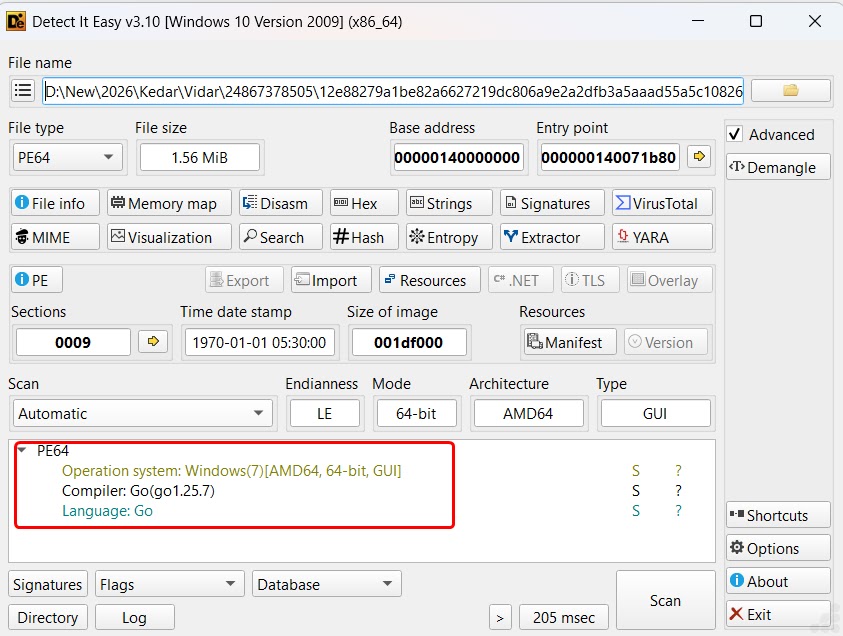
The infection starts with a Go-compiled dropper binary that acts as the initial entry point. Since Go is not a language commonly tied to malware, this choice helps the sample avoid detection by many traditional security tools.
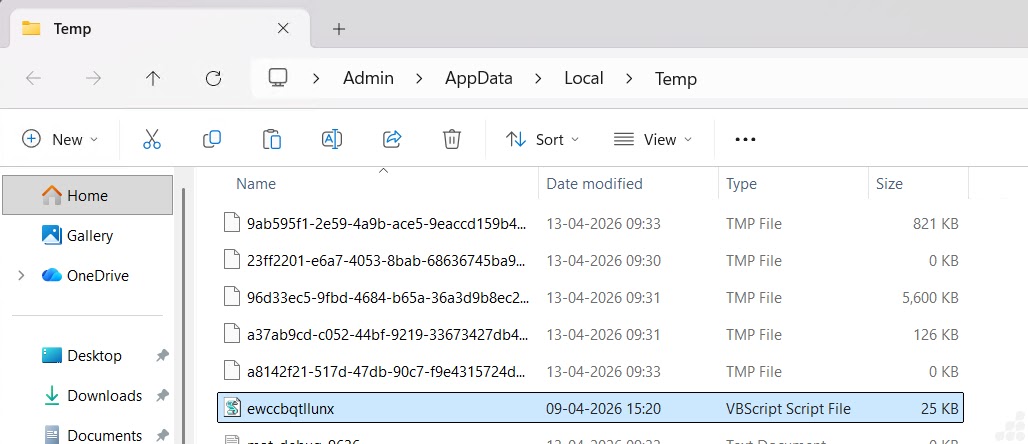
Once executed, the dropper places a VBScript file named ewccbqtllunx.vbs into the Windows Temp folder.
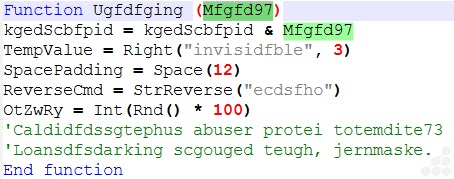
The VBScript first checks if the system is running inside a sandbox environment. If a sandbox is detected, the script exits right away. If not, it constructs an obfuscated PowerShell command and runs it with a hidden window.
This PowerShell script then connects to a remote IP address at 62.60.226.200 over TLS 1.2 and downloads a file called 160066.jpg.
The file appears to be a normal image but holds a hidden Base64 payload between custom markers labeled BASE64_START and BASE64_END.
The malware locates these markers, pulls out the encoded content, decodes everything in memory, and loads the result as a .NET assembly without saving anything to disk.
A second request then fetches KGVn4OY.txt from the same server. This text file holds reversed and obfuscated Base64 content. The malware reverses the string, replaces junk characters, decodes the result, and runs it entirely in memory.
The final payload is a 64-bit C++ executable protected by a crypter that resolves Windows API calls at runtime to avoid detection.
Security teams should block outbound connections to direct IP-based HTTP endpoints, monitor for WScript and PowerShell process spawn chains, restrict RegAsm.exe execution to signed, verified processes only, and regularly audit startup folder contents for unauthorized modifications.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.