Microsoft Store Vibing.exe App Harvested Screens Allegedly Audio
A suspicious executable named “Vibing.exe,” available on the Microsoft Store, has prompted serious privacy and security warnings from cybersecurity researchers. Marketed as an interface...
A suspicious executable named “Vibing.exe,” available on the Microsoft Store, has prompted serious privacy and security warnings from cybersecurity researchers.
Marketed as an interface to the “AI-native world” by the elusive Vibing-Team, the application reportedly harvests sensitive user data without explicit consent.
According to Kevin Beaumont, once installed on a Windows endpoint, Vibing configures itself to launch automatically upon login.
The application aggressively monitors user activity and transmits telemetry to a preconfigured Azure Front Door endpoint.
It utilizes WebSockets for communication, a known method for bypassing certain proxy blocking configurations.
The application covertly captures several types of sensitive user data:
- Base64-encoded screenshots of the user’s active desktop.
- Raw audio recordings captured directly from the system microphone.
- Hijacked the clipboard contents containing copied text and files.
- Specific keywords, window titles, and active application names.
Every piece of transmitted data is tagged with a unique hardware GUID.
This identifier allows the developers to track individual users and link screenshots to specific machines over time.
This highly invasive tracking practice is completely omitted from the application’s user interface and documentation.
Microsoft GenAI Links Discovered
Although presented as an open-source tool built by the community, OSINT investigations reveal the application is directly tied to Microsoft GenAI research labs in Beijing.
The official GitHub repository for Vibing contains no actual source code; it merely hosts an 80MB binary file.
This executable is digitally signed by Microsoft researcher Yaoyao Chang using an SSL.com co-signer.
Key evidence tying this alleged community project back to Microsoft includes:
- The Azure endpoint that receives the harvested data belongs to a Microsoft corporate-owned tenant.
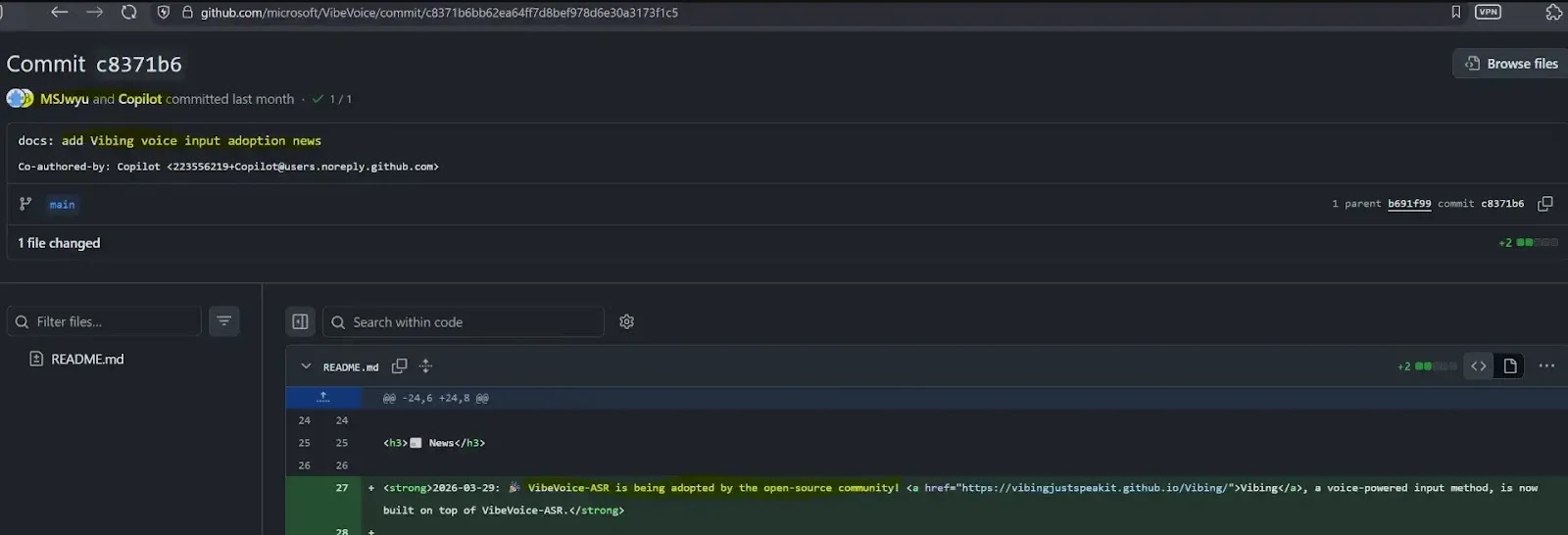
- Initial mentions of Vibing appeared directly on Microsoft’s official VibeVoice GitHub page.
- Installation documentation features screenshots taken from authenticated Microsoft corporate devices.
- The project uses the same logo as Microsoft’s official VibeVoice product.
Privacy and Security Implications
By masquerading as a community-driven initiative, the developers appear to have bypassed Microsoft’s rigorous internal governance, privacy, and security review processes.
According to researcher Kevin Beaumont on DoublePulsar, the application exposes a massive attack surface and operates with troubling opacity.
Security teams and administrators should note several critical privacy violations:
- The Microsoft Store privacy policy falsely claims that no data is sent to third parties.
- Users receive no in-app prompts or consent requests before audio and screen transmission begins.
- There is no designated data controller, and there is no transparency regarding data retention policies.
- Tracking keystrokes and screenshots via hardware GUIDs creates severe long-term surveillance risks.
Despite mounting pressure from the developer community, Microsoft has yet to issue a formal response.
Developers have tagged the involved Microsoft employees on GitHub to highlight the covert data collection.
However, individuals associated with the project have either ignored the tags or abruptly closed the issues, leaving the security community without answers.
Threat hunters and security teams should monitor their environments for the following indicators associated with this software: vibing.exe, Vibing Installer.exe, vibing-api-ccegdhbrg2d6bsd7.b02.azurefd.net
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.