Cardano Wallet Phishing Targets Users via Eternl Desktop
Phishing Targets Users via Eternl Desktop
Heads up, Cardano users! A pretty sophisticated phishing campaign is currently making the rounds in your community. It’s putting anyone trying to download the newly announced Eternl Desktop application at some serious risk.
The attack leverages a professionally crafted email claiming to promote a legitimate wallet solution designed for secure Cardano token staking and governance participation.
The fraudulent announcement references ecosystem-specific incentives, including NIGHT and ATMA token rewards through the Diffusion Staking Basket program, to establish credibility and drive user engagement.
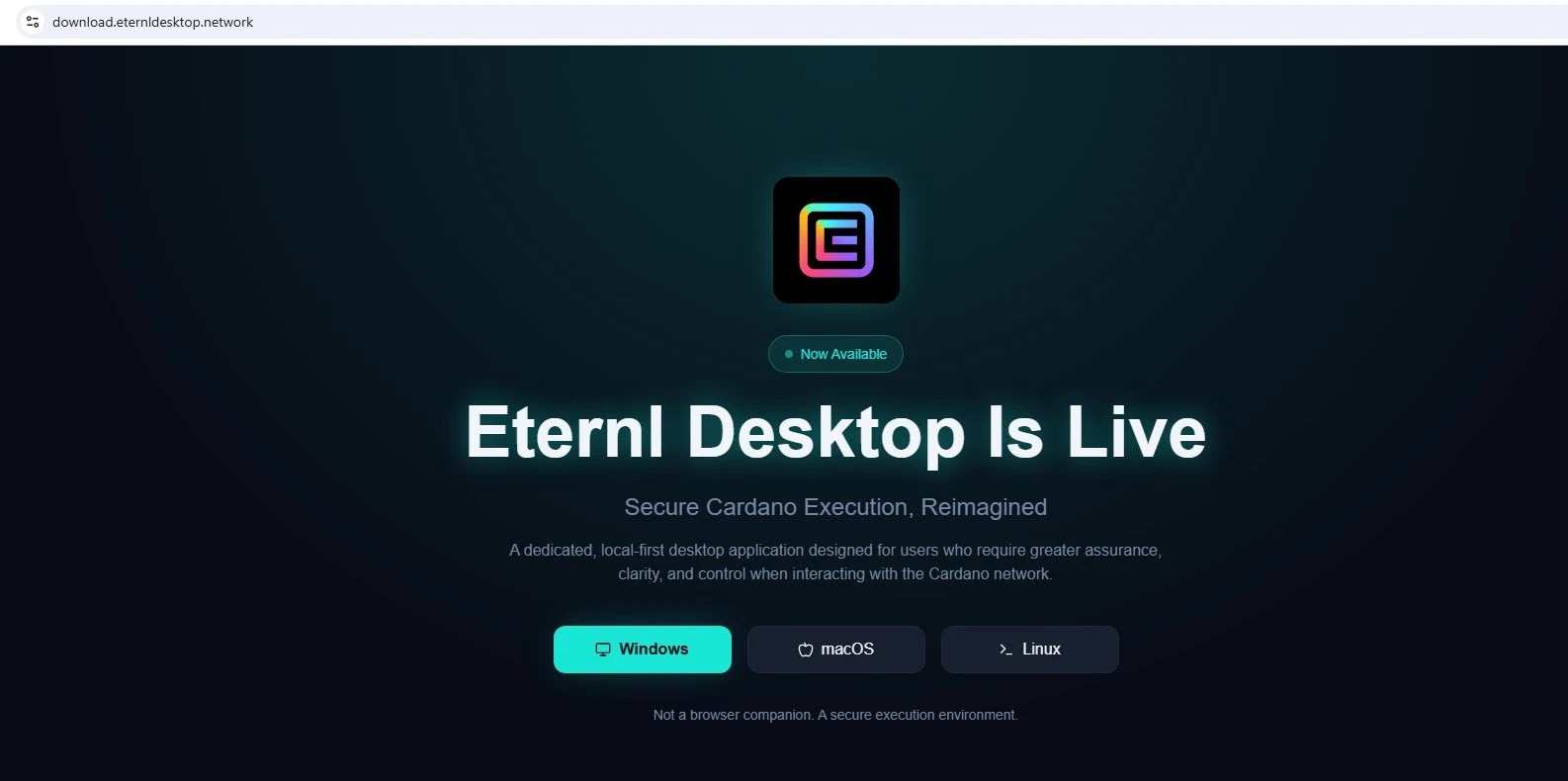
The attackers have created a nearly identical replica of the official Eternl Desktop announcement, complete with messaging about hardware wallet compatibility, local key management, and advanced delegation controls.
The email maintains a polished, professional tone with proper grammar and no visible spelling errors, making it particularly effective at deceiving community members.
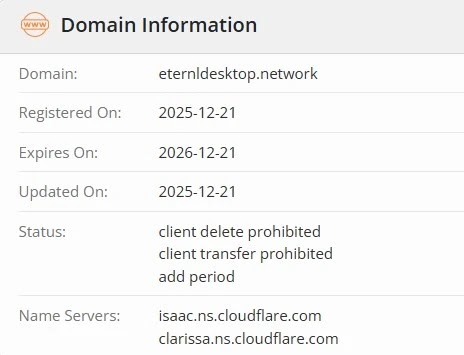
The campaign uses a newly registered domain, download.eternldesktop.network, to distribute a malicious installer package without any official verification or digital signature validation.
Independent threat hunter and malware analyst Anurag identified the malicious installer through detailed technical examination, revealing that the seemingly legitimate Eternl.msi file contains a hidden LogMeIn Resolve remote management tool bundled within its installation package.
This discovery exposed a significant supply-chain abuse attempt aimed at establishing persistent unauthorized access on victim systems.
Malicious MSI installer
The malicious MSI installer, measuring 23.3 megabytes with hash 8fa4844e40669c1cb417d7cf923bf3e0, actually drops an executable called unattended-updater.exe bearing the original filename GoToResolveUnattendedUpdater.exe.
During runtime analysis, this executable creates a uniquely identified folder structure under the system’s Program Files directory and writes multiple configuration files including unattended.json, logger.json, mandatory.json, and pc.json.
The unattended.json configuration file enables remote access functionality without requiring user interaction or awareness.
The dropped executable attempts to establish connections to infrastructure associated with legitimate GoTo Resolve services, including devices-iot.console.gotoresolve.com and dumpster.console.gotoresolve.com.
Network analysis reveals the malware transmits system event information in JSON format to remote servers using hardcoded API credentials, establishing a communication channel for command execution and system monitoring.
Security researchers classify this behavior as critical because remote management tools provide threat actors with capabilities for long-term persistence, remote command execution, and credential harvesting once installed on victim systems.
This campaign demonstrates how cryptocurrency governance narratives and legitimacy-lending ecosystem references are weaponized to distribute covert access tools.
Users should verify software authenticity through official channels only and avoid downloading wallet applications from unverified sources or newly registered domains, regardless of how polished the distribution emails appear.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.