Weaponized Shipping Docs Deliver Remcos RAT Malware Threat
A new and dangerous campaign has emerged, with threat actors weaponizing seemingly innocuous shipping documents to deliver Remcos, a potent remote access trojan (RAT). This phishing scheme uses fake...
A new and dangerous campaign has emerged, with threat actors weaponizing seemingly innocuous shipping documents to deliver Remcos, a potent remote access trojan (RAT).
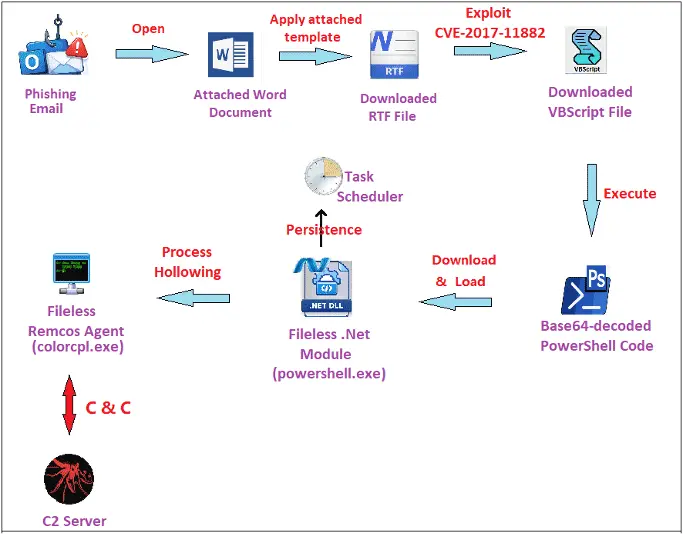
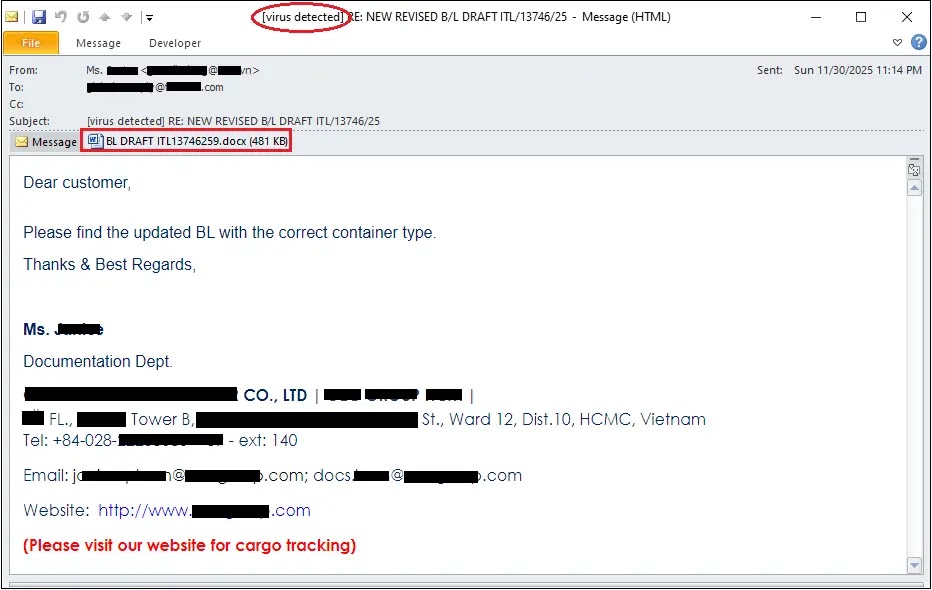
This phishing scheme uses fake shipping emails as the entry point, tricking users into opening malicious Word documents disguised as legitimate cargo documentation.
Once a victim opens the document, the attack chain begins silently, compromising the system without visible warning.
The malware delivers a commercial-grade remote access tool capable of taking complete control of infected machines.
The Remcos variant identified in this campaign represents a particularly troubling advancement in attack sophistication.
Unlike traditional malware that leaves obvious traces, this version operates in a fileless manner, meaning it executes entirely in system memory without writing suspicious files to disk.
This stealthy approach makes detection significantly harder for security teams relying on traditional file-based threat detection.
The campaign specifically targets Windows users and represents a high-severity risk to any organization that hasn’t implemented robust email security measures.
Fortinet analysts identified the malware after discovering the phishing emails being sent in the wild.
The security researchers documented how attackers crafted the shipping document emails with authentic-looking branding and reference numbers to maximize the chances of victims opening the attachments.
Once opened in Microsoft Word, the document automatically fetches a malicious template from a remote server, triggering a chain of exploits that ultimately installs Remcos on the target system.
The attack uses a known but still-critical vulnerability called CVE-2017-11882 in the Microsoft Equation Editor.
When the downloaded template file is processed, it contains specially crafted data designed to crash the Equation Editor in a controlled way.
This crash allows attackers to execute arbitrary code with the same permissions as the Word application, providing a perfect launching point for the malware installation process.
Infection Chain and Persistence Mechanisms
The way this malware achieves persistence demonstrates careful engineering by the attackers. After the initial exploitation, the attack downloads a Visual Basic Script that further downloads a .NET module.
This module is then loaded into a PowerShell process where it operates invisibly.
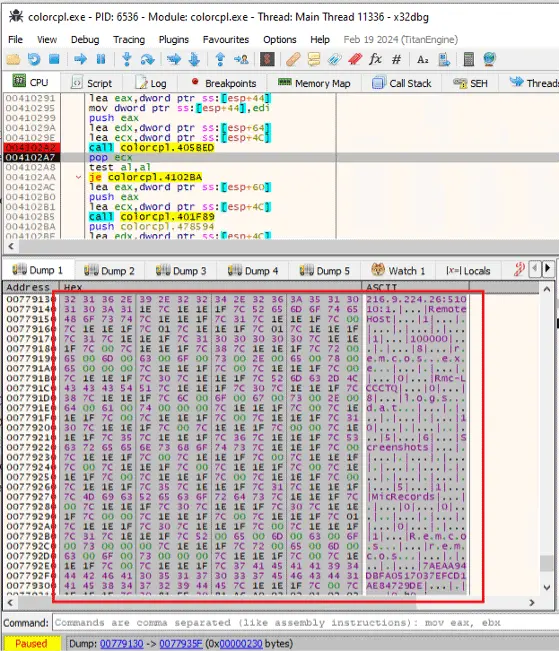
The Remcos agent itself masquerades as a legitimate Windows utility file called colorcpl.exe, which helps it blend into normal system operations.
To ensure the malware survives system reboots, the threat actors leverage Windows Task Scheduler to create scheduled tasks that relaunch the malware whenever the infected computer starts.
The most concerning aspect is the range of capabilities this RAT provides once installed.
Remcos can capture screenshots, record keystrokes, monitor microphone and camera input, and access sensitive files stored on the infected machine.
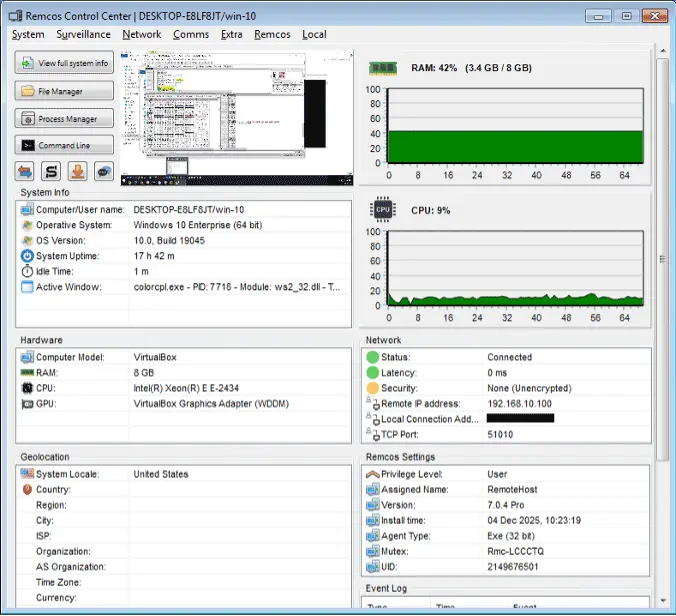
It can establish connections back to command-and-control servers at 216.9.224.26:51010, allowing attackers to issue remote commands.
The malware uses Transport Layer Security encryption to protect its communication with attackers, making network-based detection even more difficult.
Organizations discovered with Remcos infections face complete system compromise, as attackers gain administrative-level remote control over their Windows infrastructure.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.