Threat Actors Hide Stealthy PURELOGS in Hiding Payload
A newly discovered attack campaign has exposed a sophisticated delivery method for the PURELOGS infostealer. This commodity malware is widely sold as a service on underground forums. Threat actors...
A newly discovered attack campaign has exposed a sophisticated delivery method for the PURELOGS infostealer. This commodity malware is widely sold as a service on underground forums.
Threat actors are using weaponized PNG files hosted on legitimate infrastructure to deliver the payload while evading detection systems.
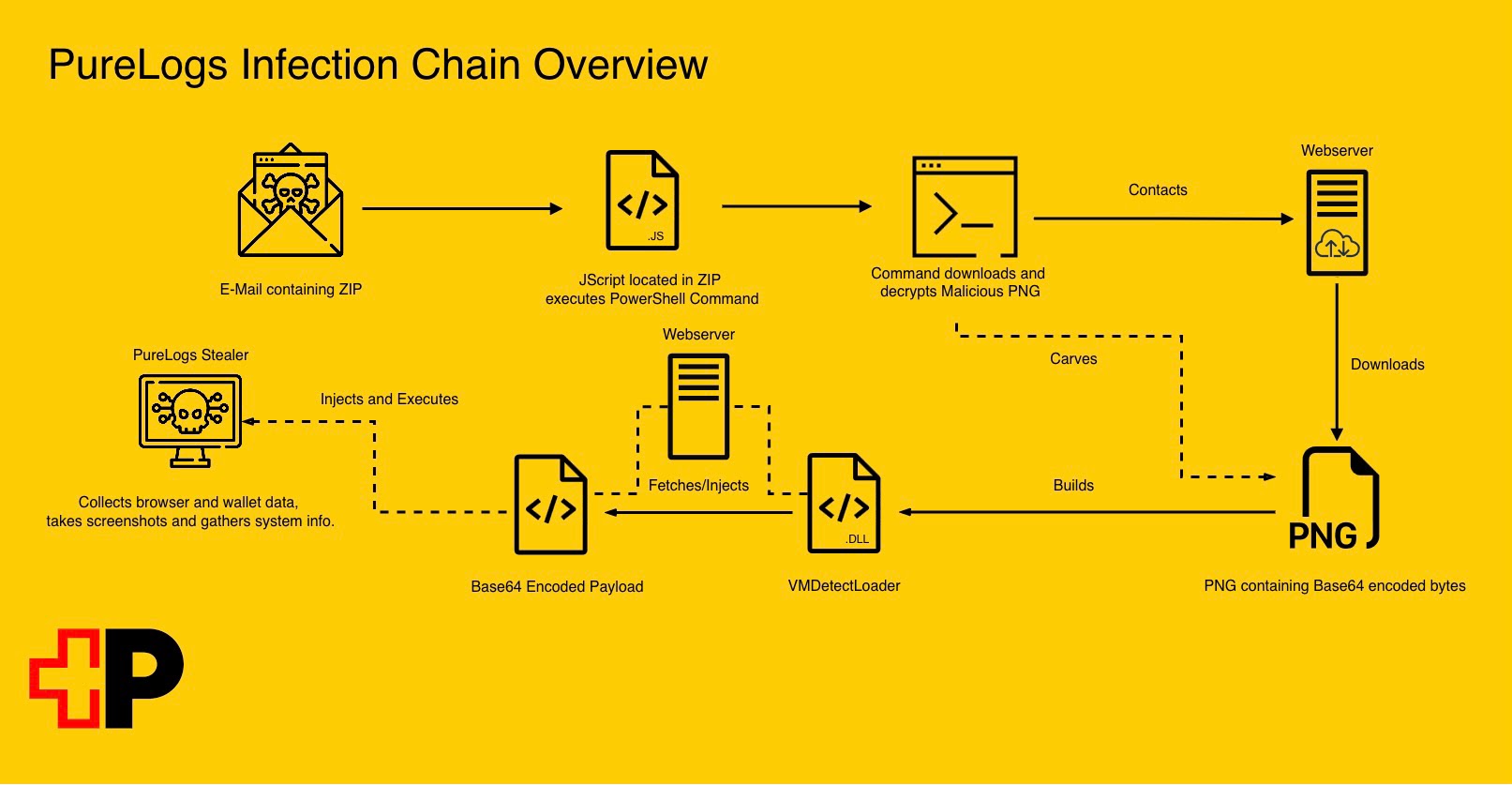
The campaign begins with deceptive phishing emails disguised as pharmaceutical invoices, containing a malicious ZIP file that triggers a multi-stage attack chain designed to bypass traditional security controls.
The attack chain demonstrates how modern cybercriminals leverage legitimate services to hide their tracks.
After users execute the initial JScript dropper within the ZIP archive, the malware reaches out to archive.org, a trusted website, to download what appears to be an innocent image file.
However, this polyglot PNG contains a hidden Base64-encoded payload embedded after the official image data ends, allowing the file to render normally while concealing malicious code from both users and security tools.
Security analysts from Swiss Post Cybersecurity identified and analyzed this previously unnoticed campaign after the unusual phishing sample caught their attention.
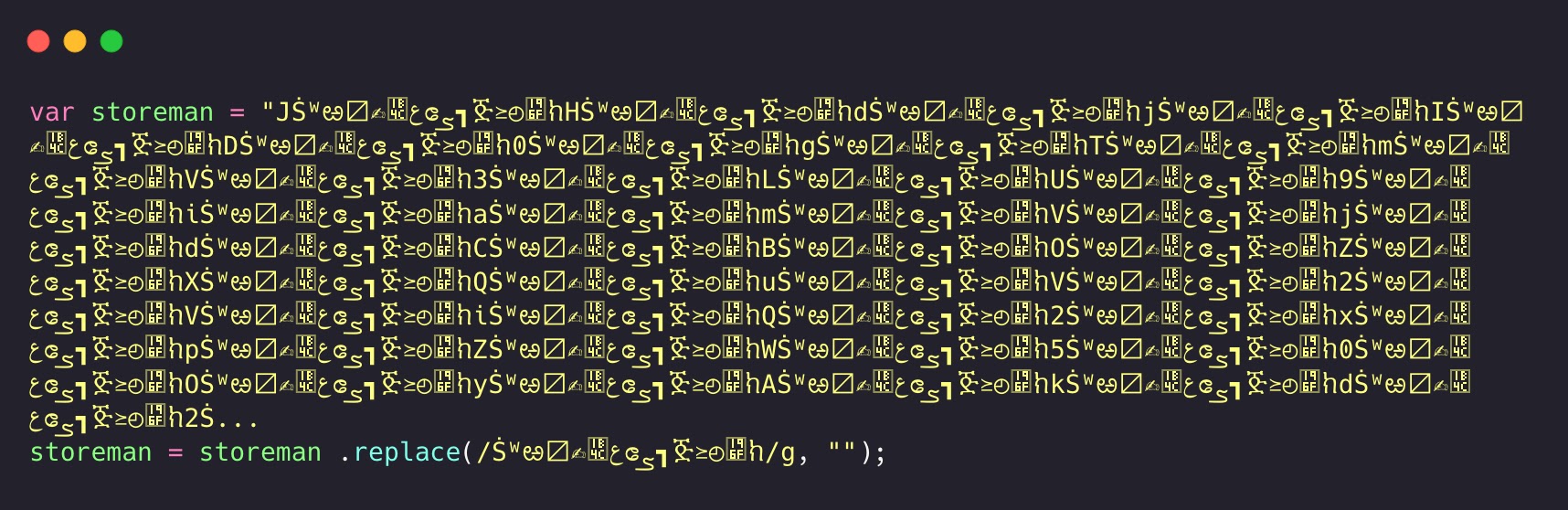
Louis Schrmann, Security Analyst at Swiss Post Cybersecurity, detailed how the loader bypasses four layers of obfuscation to reveal PURELOGS at its core.
The discovery highlights how attackers combine known malware with innovative staging infrastructure to maximize evasion and delivery success.
What makes this attack particularly concerning is its use of fileless execution techniques throughout the entire infection chain. The PowerShell payload never touches the disk, existing only in memory during its execution phase.
This approach renders file-based antivirus signatures and hash-based detection methods completely ineffective against this threat.
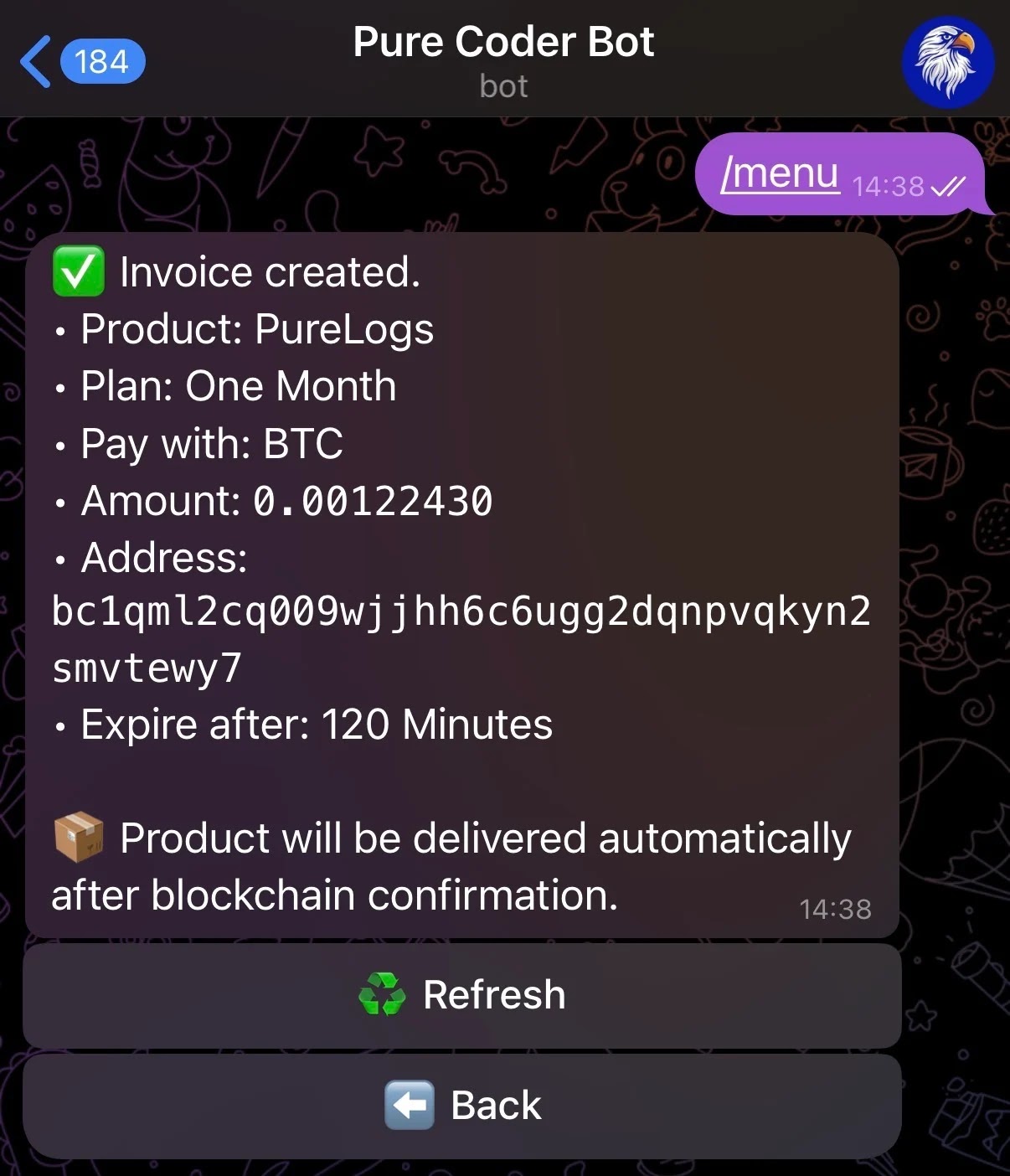
The financial incentive behind these attacks is substantial. PURELOGS operates as Malware-as-a-Service, with subscriptions starting at just $150 per month, making it accessible to operators with varying levels of technical skill.

This democratization of malware means organizations face threats from both sophisticated groups and novice attackers using identical tools.
Detection Evasion Through Polyglot PNG Architecture
The core innovation in this campaign lies in how threat actors weaponized PNG files to hide the PURELOGS payload while maintaining file integrity.
The decoded PowerShell script from stage one doesn’t fetch an executable from a disposable domain, which would immediately raise flags during network analysis.
Instead, it downloads a PNG image from archive.org, a request that appears benign to network defenders and security monitoring tools.
The technical sophistication becomes apparent when examining the file structure. The attackers embedded their Base64-encoded payload after the IEND chunk, which marks the formal end of PNG image data according to the image format specification.
The payload sits between custom markers labeled “BaseStart-” and “-BaseEnd,” remaining completely hidden within the image file while the image continues to render perfectly in any image viewer.
This polyglot approach allows the file to function as both a legitimate PNG image and a container for malicious code.
The malware extracts the payload using regex pattern matching to find content between the custom markers, then Base64-decodes the results and loads the assembly directly into memory using .NET Reflection.
This two-stage extraction process ensures the actual malware code never exists on disk in its executable form.
The PowerShell process launches a hidden execution environment and runs the decoded payload through the Invoke-Expression cmdlet, completing the in-memory execution that defeats disk-based security controls.
The sophisticated use of archive.org’s reputation as cover demonstrates how attackers weaponize trust relationships established by legitimate infrastructure to blend their traffic with normal internet activity.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.