Vimeo Confirms Data Breach: Hackers Accessed User Database
The video hosting platform Vimeo has confirmed a data breach, revealing unauthorized access to its user database. The security incident stems from a compromise at Anodot, a third-party analytics...
The video hosting platform Vimeo has confirmed a data breach, revealing unauthorized access to its user database.
The security incident stems from a compromise at Anodot, a third-party analytics vendor utilized by Vimeo and several other major organizations.
This event highlights the escalating threat of supply chain attacks within the software-as-a-service (SaaS) ecosystem.
The breach has been linked to the notorious threat actor group known as ShinyHunters.
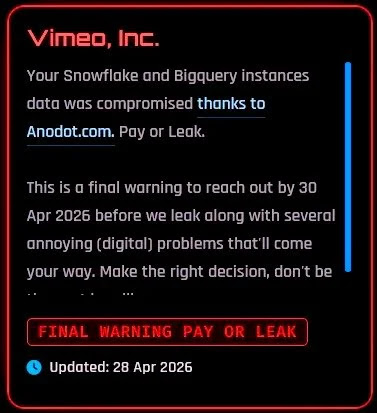
According to a recent Google Threat Intelligence report, ShinyHunters has been actively conducting widespread SaaS data theft campaigns.
The attackers likely leveraged trusted API connections between Anodot and its clients to access Vimeo’s environment.
This method represents a classic supply chain compromise, allowing threat actors to bypass a primary target’s perimeter defenses by exploiting a vendor link.
Scope of Compromised Data
Vimeo’s security team has completed an initial forensic analysis to determine the extent of the data exposure.
The unauthorized actor successfully extracted specific datasets from the company’s infrastructure.
The compromised databases contained the following information:
- Internal technical operational data.
- Video titles and associated metadata.
- Customer and user email addresses in certain instances.
Vimeo has confirmed that the core infrastructure remains intact and highly sensitive user data was not exposed.
The threat actors did not access actual video content, valid user login credentials, or any payment card information.
Upon detecting the unauthorized access, Vimeo executed an immediate incident response protocol to contain the threat and prevent further data exfiltration.
The company implemented the following security measures:
- Promptly disabled all active Anodot service credentials.
- Completely severed and removed the Anodot integration from Vimeo’s internal systems.
- Engaged external digital forensics and incident response experts to assist with the investigation.
- Notified relevant law enforcement agencies to track the threat actor’s activities.
Vimeo has assured its customer base that the security incident did not disrupt its hosting services or internal systems.
Because user passwords and financial data remain secure, Vimeo has not forced a mandatory password reset for its platform.
Since some user email addresses were exposed, customers should remain vigilant against potential targeted phishing campaigns.
Threat actors often use stolen emails in combination with scraped metadata to craft convincing social engineering attacks.
Vimeo stated that the investigation is still ongoing and promised to provide further updates as new forensic evidence emerges.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.