LofyStealer Targets Minecraft Players with Node. Targeted Using
By analyzing public submissions, security researchers have linked a recent cyber campaign to the LofyGang group. This Brazilian-origin cybercrime organization was first identified by Checkmarx in...
By analyzing public submissions, security researchers have linked a recent cyber campaign to the LofyGang group. This Brazilian-origin cybercrime organization was first identified by Checkmarx in October 2022.
The attribution is backed by hardcoded Brazilian Portuguese strings found inside the code, a C2 server hosted at a small Brazilian datacenter with the IP address 24.152.36.241, and the command-and-control panel branding itself as “LofyStealer, Advanced C2 Platform V2.0.”
Threat actors spread the malware entirely through social engineering. They package the malicious file as a Minecraft cheat called “Slinky” and use the game’s official icon to make it look completely legitimate.
This method works particularly well because Minecraft attracts a younger audience that is far more likely to download cheats or mods from unofficial sources.
Once the file is executed, the infection starts silently in the background with no visible warning signs shown to the user.
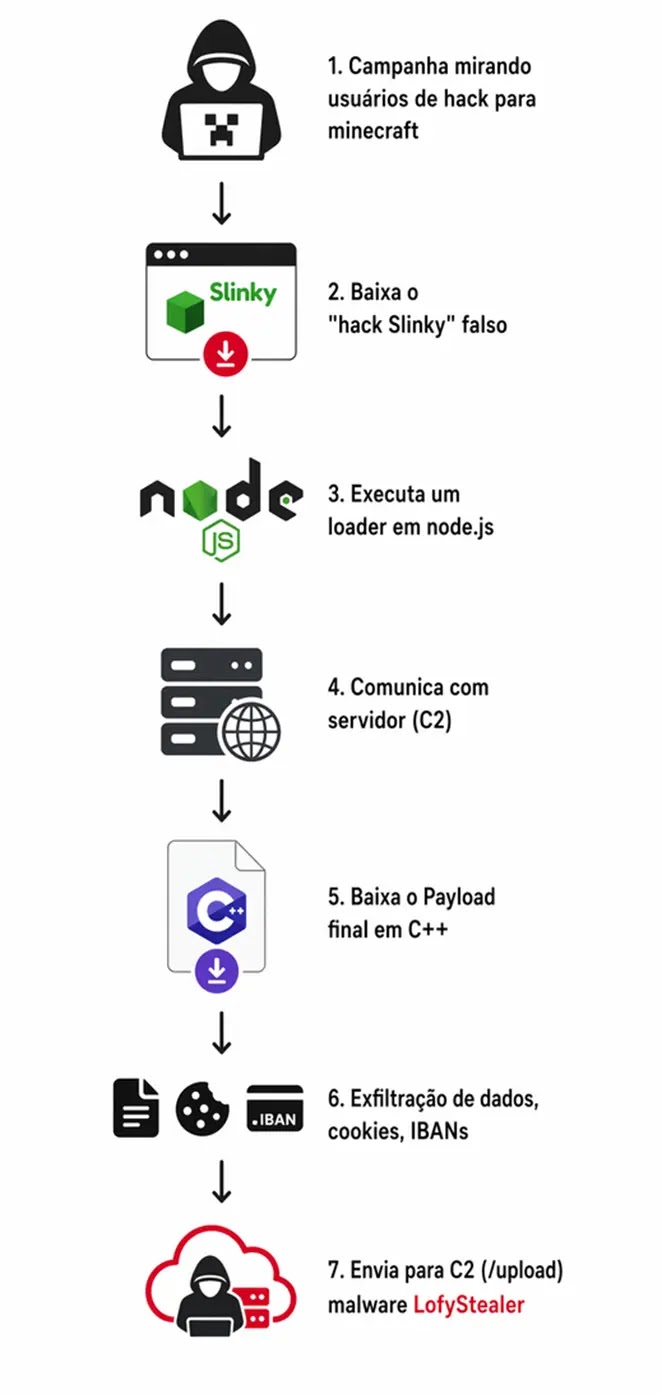
LofyStealer operates as a Malware-as-a-Service (MaaS) platform, offering Free and Premium tiers to criminal buyers through a web-based dashboard. Premium users gain full access to a victim management panel, a custom executable builder called “Slinky Cracked,” and real-time monitoring of compromised machines.
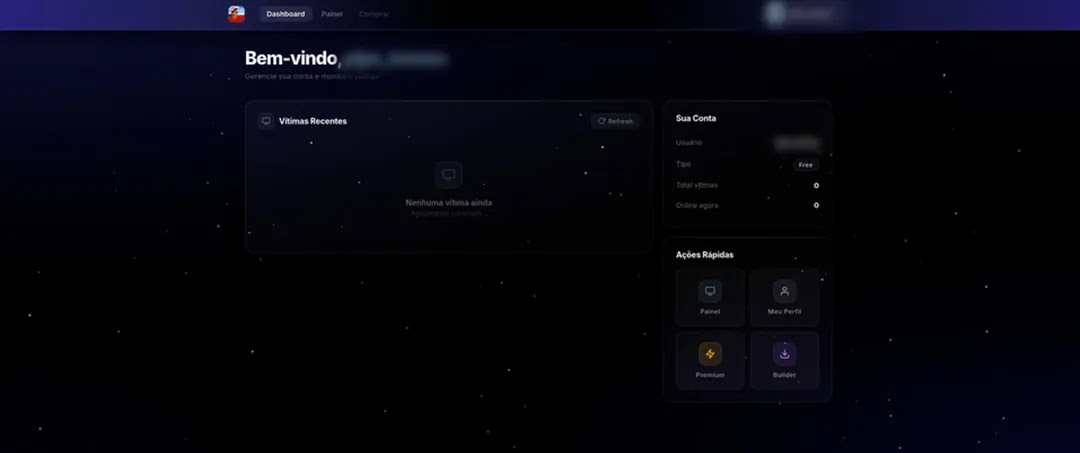
This structured business model reflects a mature and professionalized operation that has grown well beyond its early roots as a JavaScript supply chain attack distributed via the NPM package registry.
In-Memory Browser Injection: How LofyStealer Bypasses Security Tools
The most technically notable part of LofyStealer is the way its second-stage payload, chromelevator.exe, gets injected into active browser processes without triggering common security defenses.
Once the loader, load.exe, runs on the victim machine, it queries the Windows registry to locate installed browsers and then launches the identified browser in a suspended state, temporarily halting the process before it becomes fully active.
The loader then maps the payload directly into the browser’s memory space using kernel-level Windows calls. Rather than relying on common API functions that endpoint security products actively watch, it resolves low-level functions from ntdll.dll at runtime through direct syscalls.
This technique bypasses EDR and antivirus hooks that only monitor high-level KERNEL32.dll calls, giving the payload a clean and undetected path into the running browser process.
Once injected and fully active inside the browser, the payload extracts cookies, stored passwords, session tokens, payment card data, and IBANs across eight targeted browsers.
Stolen data is compressed using a hidden PowerShell command, encoded in Base64, and sent to the C2 server via an HTTP POST request with a SHA-256 integrity signature attached. The server then makes all stolen records available to operators through the live web dashboard.
Users and organizations should avoid downloading Minecraft mods, cheats, or game utilities from unofficial or untrusted sources, particularly those shared through Discord channels or unknown file-sharing sites.
Endpoint security solutions capable of detecting in-memory injection behavior offer stronger protection against this malware than traditional file-based scanning alone.
Multi-factor authentication should be enabled on all gaming, streaming, and financial accounts to reduce the risk of credential theft.
Security teams are advised to block outbound traffic to IP 24.152.36.241 on port 8080 and monitor systems for PowerShell execution running in hidden mode as a key behavioral indicator of compromise.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.