Turla’s Kazuar v3 Loader Leverages Event Tracing for Windows and
Sophisticated threat actor Turla has deployed an upgraded version of its Kazuar v3 loader. Known for targeted cyber attacks, Turla’s latest loader introduces advanced evasion techniques...
Sophisticated threat actor Turla has deployed an upgraded version of its Kazuar v3 loader. Known for targeted cyber attacks, Turla’s latest loader introduces advanced evasion techniques engineered to bypass modern security defenses.
This latest iteration, discovered in January 2026, showcases a remarkable evolution in the group’s malware capabilities.
The malware operates through a multi-stage infection chain that begins with a seemingly harmless VBScript, which then deploys a native loader and several encrypted Kazuar payloads.
This architecture demonstrates the attackers’ deep understanding of Windows internals and their ability to manipulate legitimate system processes for malicious purposes.
The infection starts when a VBScript file, tracked as 8RWRLT.vbs, downloads multiple components from a command and control server hosted at 185.126.255.132 in Ukraine.
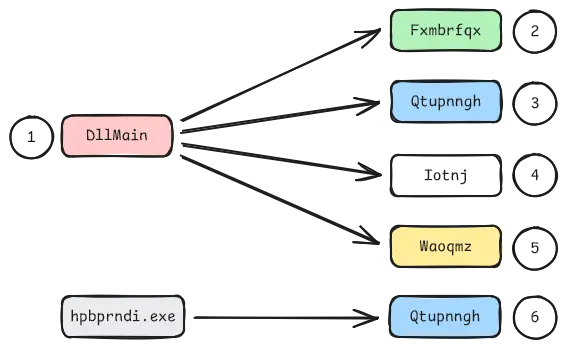
The initial stage deploys a legitimate Hewlett-Packard printer driver installer alongside a malicious DLL, which are executed together through a technique known as DLL sideloading.
The script then creates multiple encrypted payloads that eventually execute within the Windows COM subsystem, allowing the attacker to maintain persistence while evading detection.
The infrastructure behind this campaign mirrors tactics previously documented by ESET in their analysis of Gamaredon and Turla collaboration, suggesting ongoing coordination between different threat actor groups.
Security analyst Dominik Reichel identified and documented this sophisticated attack chain after careful reverse engineering of the malware samples.
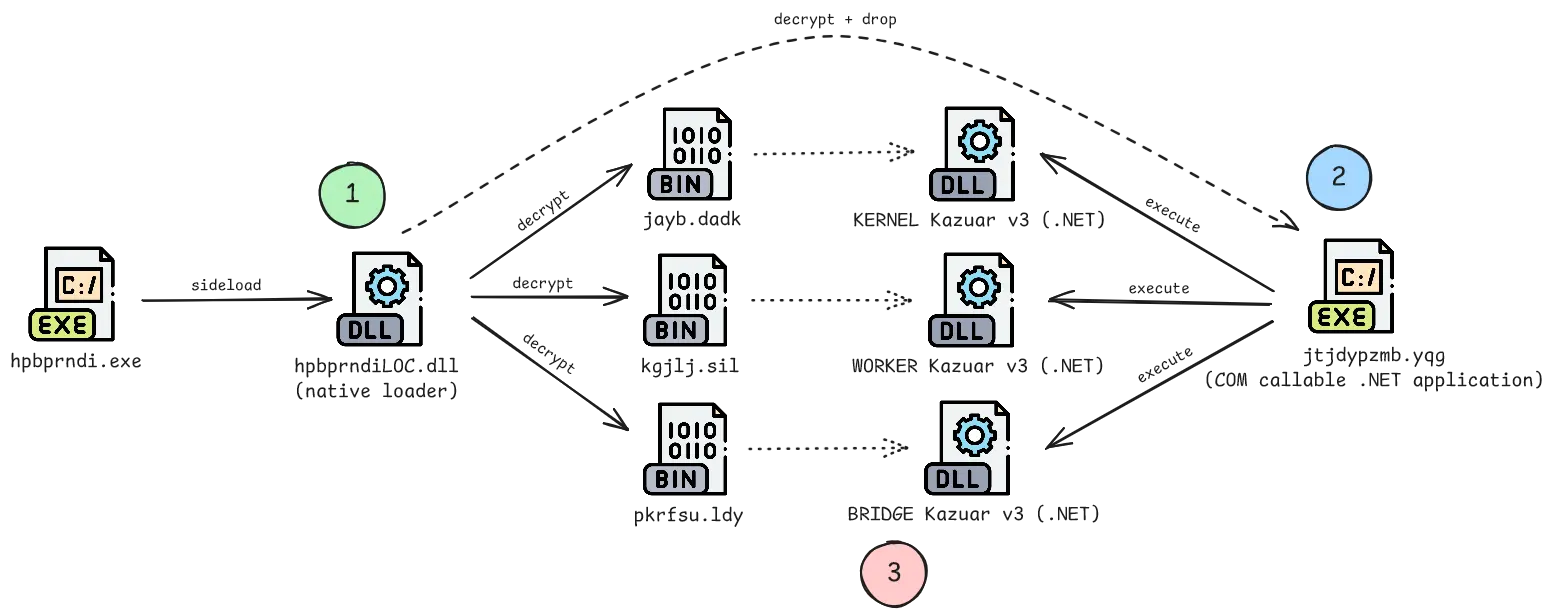
His analysis revealed that the threat actors embedded execution logic directly into the Windows COM subsystem, enabling the malware to masquerade as legitimate system interactions.
This discovery highlights how advanced threat groups continue to innovate their evasion methods to circumvent both traditional antivirus solutions and modern endpoint detection systems.
Detection Evasion Through Hardware Breakpoints and System Integration
The most remarkable aspect of Turla’s Kazuar v3 loader lies in its implementation of patchless bypasses for Event Tracing for Windows (ETW) and Antimalware Scan Interface (AMSI), the two primary monitoring systems that protect Windows systems.
Rather than modifying code on disk, the malware uses hardware breakpoint hooking to intercept security function calls without leaving traditional code patches.
The technique works by registering a vectored exception handler that monitors two critical functions: NtTraceControl for ETW and AmsiScanBuffer for AMSI.
When the malware sets hardware breakpoints on these functions, the CPU automatically triggers an exception whenever they are executed, allowing the custom handler to spoof their results before returning control.
The implementation begins by calling GetThreadContext to capture the current thread’s CPU state, then modifies the hardware debug registers DR0, DR1, and DR7 to activate monitoring on the target function addresses.
Once these hardware breakpoints are committed using NtContinue, the system watches for any execution of those specific memory addresses.
When a security function is called, instead of allowing it to perform its intended checks, the handler intercepts the execution. For ETW, the handler simply jumps over the entire function, effectively blinding the event tracing system.
For AMSI, the handler manually overwrites the AMSIRESULT pointer on the stack with AMSIRESULTCLEAN and sets the return value to indicate a successful scan, completely bypassing the malware detection layer.
This approach offers significant advantages over traditional patching methods because it works immediately upon execution and leaves no evidence on disk.
The malware additionally employs a control flow redirection trick that manipulates the Windows stack to execute code twice, allowing it to hide its primary malicious routines until after the initial execution appears to complete.
Combined with legitimate printer driver execution and COM object manipulation, these evasion techniques create multiple layers of obfuscation that delay analysis and frustrate automated detection systems.
Security researchers analyzing this malware must now account for these low-level CPU register manipulations when developing detection rules and response strategies.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.